Security Now Episode 912 Transcript
Please be advised this transcript is AI-generated and may not be word for word. Time codes refer to the approximate times in the ad-supported version of the show.
Leo Laporte (00:00:00):
It's time for security. Now, Steve Gibson is here. A mistaken Windows update. Steve explains. We'll also talk about last pass. Now that more details are coming out, it's really kind of a stunning hack. Signal says Tata to the uk. Well, it will if the UK does something bad. And believe it or not, the NSA's security recommendations, they're pretty good. All that and more. Coming up next on Security Now podcasts you love
... (00:00:31):
From people you trust.
Leo Laporte / Steve Gibson (00:00:34):
This is twit. This is Security Now with Steve Gibson, episode 912, recorded Tuesday, February 28th, 2023. The NSA at Home Security now is brought to you by Kolide. Kolide is a device trust solution and ensures that if a device isn't secure, it can't access your apps, it's zero trust for Okta. Visit kolide.com/securitynow and book a demo today.
(00:01:09):
Thanks for listening to this show. As an ad supported network, we are always looking for new partners with products and services that will benefit our qualified audience. Are you ready to grow your business? Reach out to advertise at twit tv and launch your campaign. Now it's time for security. Now, the show we cover the latest in security with the most important guy in this building right now. Mr. Steve Gibson, and he's not even in the building. Hey, hey. Grc.Com again. Yes, it's good to see you. Yeah. Time once again to talk about how bad the world is. Oh, we squeaked One more episode in on this last day of February. Of course February ended early, so, you know, that's what made it squeaky tight. <Laugh> <laugh>. So we've got a bunch of questions in our new style that we're going to answer, and I really do wish that our audience had ha had heard you encounter our picture of the week for the first time.
(00:02:12):
Oh, it's a belly laugh. Wow. It is. Every time I look at it, it cracks me up again. But we're first gonna answer some questions. What mistake did Windows update make last week? What if you don't want a paste with formatting? What browser is building in a limited bandwidth vpn? N huh. What more did we just learn about Last passes second breach. What did Signal have to say to the UK about scanning its user's messages? What was just discovered hiding inside the Python package Index repository. What proactive move has qap finally taken? Ah, what disastrous bug did spin rights testers uncover last weekend in motherboard bios? What amazingly useful best practices advice has the NSA just published for home users? Answers to all those questions and some additional thoughts will be yours Before you know it. <Laugh> on this week's 912th episode, still going strong of security now titled the NSA at home.
(00:03:28):
Oh. Oh, that's gonna be interesting. Bring your NSA home with you. Yeah. And that last pass thing. Holy cow. What a revelation. Yeah. the finally, the gay gave us some details and it's not good. Yep. It's it's bad. It's very bad. I, you, you, you know, I had to, I had the feeling. You don't, you don't want these bad guys on your tail because I mean, I, and none of us. No, no kidding. These, this was a very aggressive attack. Attack. They really knew what they wanted, which is kind of does not bode well for those of us whose last pass vaults are now in their hands. Yeah. I mean, they're, they were, they went after 'em. That wasn't some, you know, some script kitty, he accidentally found them. Anyway, we'll get to that in a second. But first we will first a word from our sponsor and some really good folks.
(00:04:18):
I'm big fans of Kolide, K O L I D E. It's a device trust solution that ensures that unsecured devices can't access your apps. This is the kind of thing honestly, LastPass probably should have had. Kolide has some big news. If you are an Okta user, I know you know Okta, we use it Kolide can get your entire fleet to 100% compliance. Wait a minute, I think I better explain that. Huh? Kolide patches one of the major holes in zero trust architecture, which is device compliance. I mean, this was what bit last pass. I mean, your identity provider only lets known devices log in apps. Right? But just because a device is known doesn't mean it itself is in a secure state. In fact, plenty of the devices in your fleet probably should not be trusted. Maybe they're running on an out-of-date OS version, or maybe they've got unencrypted credentials lying around.
(00:05:21):
Maybe they've got Plex <laugh> running on them. If a device is not compliant or isn't running the Kolide agent, it can't access the organization's SaaS apps or their other resources. Lemme say that again. If the device isn't running the Kolide agent, it can't get in. The user can't log into your company's cloud apps until they fix the problem on their end. It's that simple A device. Here's an example. If a, if an employee doesn't have an up-to-date browser, that happens all the time. Using end user remediation helps drive your fleet to a hundred percent compliance. And it's not on you, the IT team. That's what I love about Kolide, Kolide enrolls your end users on your side as part of your overall defense. They do the work, they get the notification your browser needs to update. Here's how we do it. Here's why we do it.
(00:06:13):
And it's done without Kolide IT. Teams have no way to solve these compliance issues. You may not even know, right? Or stop insecure devices from logging in with Kolide. You could set and enforces compliance across your entire fleet. And here you'll love this. It's cross-platform. Nowadays, it's not unusual. We got multiple operating systems. We got Mac, we got Linux, we got Windows. Kolide, works on all three. Kolide is unique in that it makes device compliance part of the authentication process. So when a user logs in with Okta Kolide alerts them to compliance issues and says, stop. If you've got an you know, problems, it prevents unsecured devices from logging in, that's gonna make you feel a lot better. Frankly, there's a number of cases where this would've made me feel a lot better. Like, well, we'll talk about it a little bit later.
(00:07:06):
Kolide is secure. You can feel good about, because Kolide puts transparency and respect for users at the center of their product. To sum it up, Kolide s method means fewer support tickets, less frustration from your users, and most importantly, 100% fleet compliance. It is a critical part of your zero trust network. Kolide.Com/Securitynow to learn more. You can book a demo K o l i d e.com/securitynow, and we thank 'em so much for their support and I strongly encourage you to check out Kolide. There's a lot of good stuff in there we don't even have time to talk about. Now, Steve, talking about zero knowledge, <laugh>.
(00:07:54):
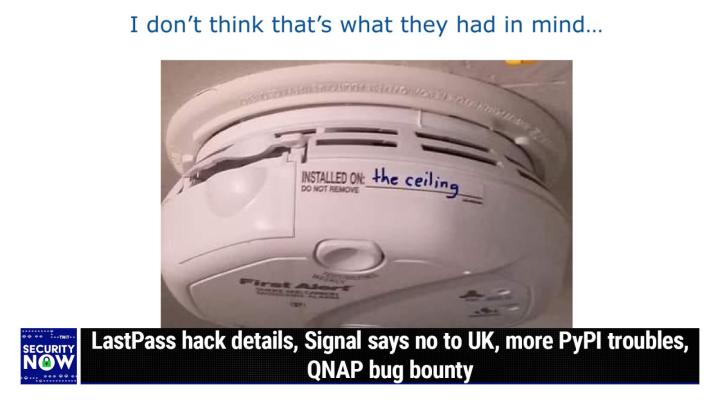
Okay, so our picture of the week what we have is a closeup photo that I presume someone took when they were checking out the smoke alarm on the home they just bought. Or maybe the apartment. They're rent, I don't know. So we've got a first alert smoke alarm in closeup. You can over on the left, you see the little door you can, you can pull off probably to change the, the nine volt battery and so forth. Anyway, the focus of this picture and the intent of taking a picture of a smoke alarm is that it, there's a printer on the side is a field where you can indicate the date at which this was installed because, you know, that can be important. Like fire extinguishers have an expiration date. You need to, you know you know, change, change them out every so often. So this says installed on colon, and then there's an underline where clearly you're intended to indicate the date of installation. <Laugh>, what we have instead written here is installed on the ceiling. <Laugh>.
(00:09:10):
Oh boy. Oh boy. That's where it is. That's why I'm on a ladder. Okay. Yeah. Installed on the ceiling where, I'm not sure where else you would install it, you know, on the wall, on, on the floor. <Laugh>. I, I don't, I think Joe though inspection will reveal that is in fact installed on the ceiling. No need to write that down. That's true. Yeah. You're looking at, yeah, you don't wanna leave that field blank. However, maybe the maybe it won't work without something written there. So let's see. What could they possib? What were they installed on? What did they want me to, it's obvious they, they wanna know where it was installed. What's it installed on? Not a hard time getting outta high school because of those multiple choice tests, you know, oh Lord. Installed on the ceiling. Okay, good. So, okay. <Laugh> Windows 11.
(00:09:59):
Anyone? Yesterday morning I received a following email from a podcast listener and happened to be a spin, right? 61 tester Jeremy wrote from Texas. Hi fyi, about Wednesday of last week, windows 10 update offered to update me to Windows 11. Even though my HP a i o, that's an all in one, does not, he has in caps qualify because it does not have the latest boot security level. I immediately switched over to grc.com and downloaded in control and set my PC to stay on Windows 10 22 H two with security updates. When I reloaded Windows. Update Windows 11 was no longer being offered. I thought I was safe from Windows 11 <laugh>. He writes, since I didn't qualify, but I guess not, just wanted to let you know to combine my efforts with others, if any. It's a reminder to be proactive rather than rely on assumptions.
(00:11:04):
I've invested a lot of muscle memory in Windows 10 and don't think Windows 11 will offer me much. I don't know if it was a momentary glitch in one up in WIN update or a real offer since I got in control immediately. And he signed off regular listener and 6.1 tester Jeremy in Texas. Well also yesterday came the news that Microsoft had fixed a bug that was responsible for causing upgrade offers to unsupported PCs. Apparently the issue came to light last Thursday for Microsoft and it was quickly resolved and the fix was then pushed out to affected devices over this past weekend, and this isn't the first time this has happened, windows 1122 H two was previously offered to Windows 11 insiders in the release preview channel, even when they were using ineligible devices. So it was that after Microsoft was aware of this, but before they had pushed the update that Windows users were reporting many more than just Jeremy, Jared in Texas via Reddit and Twitter, that their unsupported devices were, to their surprise, suddenly being offered windows 11 upgrades.
(00:12:22):
So, so Microsoft MI Microsoft confessed this and they said some hardware ine ineligible Windows 10 and Windows 11, version 21 H two devices were offered an inaccurate upgrade to Windows 11. These ineligible devices did not meet the minimum requirements to run Windows 11 devices that experienced this issue were not able to complete the upgrade installation process. So apparently some users with Windows 10 and even some who were using Windows 1121 H two were surprised and I presume delighted by this news. Whereas Jeremy and I were would've both been horrified by it. The impacted devices included those running Windows 1121 H two, windows 10 21 H two, and Windows 10 20 H two. And as Microsoft indicated, some later portion of the upgrade process apparently recognized the mistake that had been made and aborted the upgrade. So, and remember that last month, Microsoft announced that it had started a forced rollout of Windows 1122 H two which is also known as a Windows 11 20 22 update to systems running Windows 1121 H two, which will be approaching their end of support date later this year on October 10th, actually is when it officially ends in, of course, 2023.
(00:13:57):
And this automated feature update rollout phase came after the Windows 11 20 22 update also became available for broad deployment. The same data users with ineligible devices via Windows update. Now as it happens, the little Windows TED Machine I use weekly for zooming this podcast to all of our listeners and Leo a twit and everything, it's recently been updated been bugging me, I think the last maybe two or three weeks to upgrade it to Windows 11 since, you know, I only turn it on before the podcast and then off immediately afterward. I just say, no. You know, there's got a wonderful program from a guy named Steve Gibson called in controlled when <laugh>, you don't use that, huh? Are you reading ahead? Oh, no, I'm not. Okay. <laugh>,
(00:14:52):
I'd like to be surprised I hadn't gotten around to running GRCs in Control Utility. Okay. What do you know to tweak the registry to get Microsoft to leave me alone? Now, re recall that in control is the spiritual successor to never 10. And Leo, I still remember your laughter when you first heard that name. <Laugh>. never 10. That's right. Never. 11 in this case. F off Microsoft. Yeah. Anyway, the expectation was that never 10 would be all that was ever needed. Yeah. but then Microsoft decided that Windows 10 would not be the last windows after all. But then you know, so there was some tendency, there was, there was, you know, rather than create, I thought about creating never 11, that's what people were asking for, you know, but then I'd have to do never 12 and never 13. I wonder if they would do Windows 13.
(00:15:47):
I'll bet not anyway. And then I'd have to keep changing the name. So instead I switched to in control, which now no longer at least has to change its name. As long as they leave this facility in place, I won't have to change it at all. So anyway, the point is that this story from Jeremy and the fact that I kept, you know, just saying, no, no, no, every week finally prompted me to take action. And it worked beautifully. What do you know? Initially it was showing the upgrade offer up at the top of the Windows update screen. So I ran in control and told her that I wanted to stay put where I was at Windows 10 22 H two. So I clicked the button, it tweaked the registry, and that was that. Then I reran Windows update, and the offer for Windows 11 was still there since it hadn't refreshed.
(00:16:40):
So I asked Windows update to recheck for any updates, and that refreshed the screen and the Windows 11 offer disappeared. And I received what I remembered. Now, when I was originally testing this thing, the little red asterisk notice up at the top of Windows update, which says, asterisk in red, the whole thing's in red, some settings are managed by your organization, which is, you know, yes, perfect. Leave me alone. So, you know, what we're essentially telling it is that, you know, the higher ups have decided that they're gonna be in charge of upgrading. So Microsoft shouldn't be bothering us minions with any of that. So anyway, I just wanted to remind everybody that that exists because, you know, as Microsoft has said, they're gonna get more insistent about this and no thank you. Okay oh, this next item is not security related at all, but something some news popped up at what I was looking for, security stuff that I just wanted to make sure everyone was at least aware of.
(00:17:54):
I also have no sense for how large the audience for this might be, but the facility is one of my most used keystroke combinations. It is pasting from the clipboard without formatting. I'm a big user of copy and paste for moving things around, but I almost never want to also copy and paste any of the text formatting of the source text, which may be present when I move it somewhere else to paste it. You know, it's quite annoying when I paste something and it jumps into the appearance that it had typically not even correctly. What all I want is the textual content itself. You know, I wanna lose the text metadata. So finally, a couple of years ago, after several years of annoyance, and I, I would even, I was even doing things like using Windows Notepad as an intermediate stop, where, you know, in, in order to force the dropping of the formatting, I would open notepad, copy something that had formatting paste it in a notepad, which can't hold formatting.
(00:19:01):
So it would force it to be lost. And then I would copy that again and paste it into its destination. So I thought somebody must have fixed this problem. So I went Googling and I found a slick little utility that I've been using ever since, known as Pure Text. And that's all it does. It sits in my system tray. It allows you to set any combination of shifts and an action key. I use Control Alt V rather than just control v to perform a non formatted textual clipboard paste. It's beautiful. Also you can sign a sound if you want. And I know lots of people don't like sounds, I love sounds. So it makes a nice little clunk sound to just confirm that I, you know, I got what I wanted. Anyway, I'm mentioning this because Windows Power Tools will completely separately from that soon be getting a new module called Paste as Plain Text.
(00:20:01):
In other words, I'm not the only one and or ne neither was the guy Steve Miller, who wrote this thing. The the one I'm using I'm, as I said, I'm using Pure Text both on my Windows 11 and my Windows 10 machines. But Power Tools won't run under Windows seven. You know, you gotta use the Windows store, and they won't let you do that from Windows seven. So I'll be sticking with Pure text. But you know, for what it's worth, if any of you else, you know, if anyone else has this problem, windows Power Tools will soon be getting placed as paste as plain text. But Steve miller.net is the site, and this guy's been writing code since Windows 95. He's got stuff dating from then. Still some of it useful, so you might wanna just check it out. Anyway, Steve miller.net. Okay, nearly a year ago, last April, the Verge carried the news.
(00:20:58):
Microsoft is adding a free built-in VPN to its edge browser with a subhead Edge secure network as it's being called. Actually now they're call it Microsoft Edge Secure Network will roll out, they said as part of a security upgrade. They, they didn't say when, and it took like 10 months, but it's now appears to finally be happening. It's going to be becoming available. Two days ago on Sunday, bleeping computer posted Microsoft Edges built-in VPN n functionality could soon begin rolling out to all users in the stable channel with some users already getting access to the feature. And they linked to Microsoft's announcement of this. It was the, it was the original posting, and it's one thing's not clear about from a UI standpoint what'll be changing. But, so here, here's what we know about what Microsoft is, is explaining that they'll be bringing to the Microsoft Edge Secure network.
(00:22:06):
They said, encrypts your connection encrypts your internet connection to help protect your data from online threats like hackers. When using Microsoft Edge Secure Network, your data is routed from edge through an encrypted tunnel to create a secure connection. Even when using a non-secure r l that starts with H TT P, this makes it harder for hackers to access your browsing data on a shared public wifi network. We know, of course that's true and that's probably the, the strongest use case for a a for using A V P N if you're not, you know, u using one to dial into your corporate network. Second feature helps prevent online tracking, right? By encrypting your web traffic directly from Microsoft Edge. We help prevent your internet service provider from collecting your browsing data, like details about which websites you visit. Third, keeps your location private. Online entities can use your location and IP address for profiling and sending you targeted ads.
(00:23:07):
Microsoft Edge Secure Network lets you browse with a virtual IP address that masks your IP and replaces your geolocation with a similar regional address to make it more difficult for online trackers to follow you as you browse. And finally is free to use, get one gigabyte of free data every month when you sign into Microsoft Edge with your Microsoft account, a few early adopters will be in a data upgrade trial at the end of their 30 day trial period. The experience will reflect the, not the normal p n gigabyte limits. I dunno what that last sentence. Okay, but not surprisingly, my Edge browser doesn't have it yet. You know, I'm not in any advanced leading edge mode. But under Edge's main menu, near the menu's bottom, you'll find current entries for read aloud and then more tools. And assuming that Edges UI hasn't changed since this posting was last updated, and the rest of it does look the same, there will appear a new secure network entry in between read aloud and more tools.
(00:24:26):
The other piece of interesting news is that this is being done in affiliation with our friends at CloudFlare. Microsoft wrote, Microsoft Edge Secure Network is a service provided in partnership with CloudFlare. Cloudflare is committed to privacy and collects a limited amount of diagnostic and support data acting as Microsoft's data sub-process in order to provide the services. Cloudflare permanently deletes the diagnostic and support data collected every 25 hours. Now, they didn't say that Microsoft doesn't collect it and de and Holt retain it, we don't know, but there's, but they are saying Cloudflare's not keeping it. And presumably Microsoft is not either. They said to provide access, we store minimal support data and access tokens, which are only retained for the duration of the required service window. A Microsoft account is required to access Microsoft Edge Secure Network and is retained to keep track of the amount of Microsoft Edge Secure Network data that is used each month.
(00:25:36):
This data retention is necessary to provide one gigabyte of free Microsoft Edge secure network service and to indicate when the data limit has been reached. So I don't really have any calibration on how quickly one gigabyte will be consumed, but that doesn't sound like much data For a month I checked my phone, which, you know, I don't use very much for any heavy work cuz I've al I'm always sitting in front of a computer and, and I have the small Verizon plan, which is limited to two gigabytes a month. As I said, I'm not doing much with my phone. Turns out I've used less than 0.3 gigabytes per month for the past three months. So I'm not a heavy data user on my phone. I expect that this might be something that's used sparingly and only when necessary. And, you know, you're not gonna watch movies o over your one gigabyte of free Microsoft Edge VPN data.
(00:26:40):
Their, their UI does have a bites used per so far this month meter. So it'll be possible to track one's usage and get a sense for, you know, how it's going and whether you need to scale back and so forth. Anyway, overall, this seems like a useful and welcome feature. You know, it's limited, but it's free. And you, you just need to be logged into Edge or Microsoft through Edge, which I imagine Edge users would be. So it'll, you know, it's, it'll be there in a pinch. Okay, <laugh> last pass incident update yesterday, last pass provided by far more detail about that second more devastating attack that they suffered. And that's of course the one that inspired the Leaving Last Pass podcast. And the one that followed just that was just titled the numeral one when we found out that that's what iteration counts in some cases had been left at.
(00:27:44):
And I have to admit that the forensics which were presented were impressive. This doesn't forgive them in any way from screwing up in the several other ways that we know they did. But as far as forensics examinations go, it's impressive. It's easy to tell a story in retrospect, but as I'm describing what they have determined actually happened, imagine figuring this out. That's again, I said, you know, as I said, it's, it's impressive. So I have a link to the incident details. I'm not gonna cover all of it because it goes into way more detail than we need, but what they wrote was Last Pass has now learned unexplained to us. They said to access the cloud-based storage resources, notably S3 buckets, which are protected with encryption. The threat actor needed to obtain a w s access keys. And the last pass generated decryption keys, the encrypted cloud-based storage devices housed backups of LastPass customer and encrypted vault data.
(00:28:55):
Right? And that's what got away from them. They wrote, as mentioned in the first incident summary, certain LastPass credentials stolen during the first attack were encrypted and the threat actor did not have access to the decryption keys, which could only be retrieved from two locations. First, a segmented, I'm sorry, a segregated and secured implementation of an orchestration platform and key value store used to coordinate backups of LastPass development and production environments with various cloud-based storage resources. That's the first place where the keys were, or a highly restricted set of shared folders in a last pass Password Manager vault that are used by DevOps engineers to perform administrative duties in these environments. Okay, they said, due to the security controls protecting and securing the on-premises data center installations of LastPass production, the threat actor targeted one of the four DevOps engineers who had access to the decryption keys needed to access the cloud storage service.
(00:30:17):
This was accomplished by targeting the DevOps engineers home computer, ah, and ex and ah-huh and exploiting a vulnerable third party media software package, which enabled remote code execution capability and allowed the threat actor to implant key logger malware. The threat actor was able to capture the employee's master password as it was entered after the employee authenticated with multifactor authentication and gain access to the DevOps engineers LastPass Corporate Vault. The threat actor then exported the native corporate vault entries and content of shared folders, which contained encrypted secure notes with access and decryption keys needed to access the A W S S three, LastPass production backups, other cloud-based storage resources and some related critical database backups. <Laugh>. So yes, Leo, as, as you gasped this was quite an attack. I mean, and I saw rumor that it was Plex, that it was a flaw or they thought it might be a flaw in Plex, which just engineer had been running.
(00:31:40):
So this was a very sophisticated attack. I mean, not just targeted, but they were rooting around in this guy's machine and able to find another flaw. Yep. And then, and of course, Plex is a media software package, so that tracks with that rumor that you heard. Yeah, yeah. And it was, and it was online because people often put their plex servers on the public internet, so that that's, yeah, there's your, they're in there in lies your problem, right? So as I'm, as I'm reading this, I'm thinking, wow, no one wants these guys on their tail. No kidding. Because, yeah. Wow. Okay. So listen to the steps. Last pass has since taken in an effort to recover from this attack. Never. Well, they should get lied is the first thing they should do. <Laugh>, yeah. Okay, go ahead. Yeah. Remember how last week I was talking about how difficult it would be to ever be able to trust anything ever again?
(00:32:37):
Yeah. So they zero trust. As we pro uhhuh, as we progress through incident response and as part of our ongoing containment, eradication and recovery activities related to the second incident, we have performed the following actions with additional work currently being accomplished in scoping and planning. In other words, they're not even done yet as of yesterday. So they said, with the assistance of Mandiant, we forensically imaged devices to investigate corporate and personal resources and gather evidence detailing potential threat actor activity. We assisted the DevOps engineer with hardening the security of their home network and personal resources. We enabled Microsoft's conditional access pin matching multifactor authentication using an upgrade to the Microsoft Authenticator application, which became generally available during the incident. We rotated critical and high privileged credentials that were known to be available to the threat actor. Well, okay, good. We continue to rotate. We, we continue to rotate the remaining lower priority items that pose no risk to our last pass for our customers.
(00:34:00):
Again, good. We began revoking and reissuing certificates obtained by the threat actor. We analyzed last pass a w s three cloud storage resources and applied or started to apply additional S3 hardening measures. We put in place additional logging and alerting across the storage, the cloud storage environment with tighter iam. That's identity and access management policies enforced. We deactivated prior development IAM users. In other words, they had not, that had not been done before. So good. We enabled a policy that prevents the creation and use of long-lived development IAM users in the new development environment. So that's good. They're, they're changing policies and tightening security. When they re when they looked and realized, oh crap, we've got a bunch of X X user X development users who still have credentials here. Then they said, we rotated existing production service. IAM user keys applied tighter IP restrictions and configured policies to adhere to lease privilege.
(00:35:18):
We deleted obsolete service. I aam users from the development and production environments. We are enabling IAM resource, tagging enforcement on accounts for both users and roles with periodic reporting on non-compliant resources. We rotated critical SAML certificates used internal and external services. We deleted obsolete slash unused SAML certificates used for development services or third parties. And again, that hadn't been done previously. Good that they did it need to make that a policy. We revised our 24 7 threat detection and response coverage with additional managed and automated services enabled to facilitate appropriate escalation. And finally we developed an enabled custom analytics that can detect ongoing abuse of a w s resources. So, okay. Law, it's, it's evident that things are way better now than they were before, which, you know, that's always sort of been the double edged sword of this is, you know, do you, do you trust better somebody who's learned from their mistake?
(00:36:33):
There's obviously lots of, if I may use the term learnings, <laugh> here. On the other hand, they were clearly doing some things wrong by policy and that's difficult to forgive. And that's what finally, you know, caused us a mass to leave last pass. Well, and also do you want those four DevOps guys who have the keys to be able to bring those home? I guess you do now this all because of covid probably, right? Yeah. And, and it was probably VPNing in one of the things I noticed that I, I commented on here in passing is they said we rotated existing production service user keys, applied tighter IP restrictions. If they didn't have any, then Russia could have connected to, to their S3 buckets. Right? Right, right. So it makes absolute sense to allow, first of all, the IP of somebody VPNing will be the same as the corporate IP network, right?
(00:37:40):
The, so if you weren't VPNing, your IP would be at home, but at least you'd be in the vicinity. So, you know, again, the, the, there's this, the, the, the, the, the problem we've always had is that, is this, this Tennessee not to want support calls, right? It's like, you know, we don't want tech support calls. So, you know, if we, if we don't, don't default to things being open, then, then we're gonna get complaints when things don't work, right? So we're still sort of in that mode. And, and, and also looking at this list of stuff, one of the, the bugaboos of, of evolution over time and LastPass has been around for a long time, is that things tend to become more complicated over time. Yeah. You know, this is usually driven by inevitably changing requirements. New systems are added to improve or to enable some new job, but the new system doesn't completely take over for the old one.
(00:38:46):
So that older system needs to still stay around to do some of those few things that the newer system doesn't quite do the same. Then the requirements change again, and some customizations are required. You know, some glue code is created by somebody who then later quits and takes his notes and knowledge with him. Now, no one wants to touch that weird box in the corner since no one's quite sure how it works. You know, and that's the way this, I mean, this actually happens in the real world. And Leo, I've heard you at the beginning of some of the podcast recently, like trying to figure out how to, I don't know what it is that's going on over there, but Oh boy, I don't either. Which, and exactly that's what happens is, you know, so I used to know how everything worked here. Now I know nothing.
(00:39:34):
Anyone who's, who's been working in within a complex environment with many players and constant time pressure where needs are dynamically changing will probably be able to relate to this sort of mess. You know, that winds up evolving from a what was originally a simple solution. And so my point is in the context of security, this sort of creeping evolving complexity makes both keeping things truly secure and recovering rapidly from an incident if one happens much more difficult. And, you know, it, it occurred to me that there, there really needs to be somebody who is assigned the task of stepping back from the day-to-day fray to take sort of a holistic view of an enterprise's systems and be constantly working to reintegrate the inherently disintegrating systems that just naturally form, you know, keeping things as simple as possible has tremendous benefits for an organization and in a sufficiently large organization. I, I think it really ought to be a job title. There ought to be like a job title, you know, like, I don't know, holistic system reintegrate or something, you know, and he, you know, he could like not shave and dress funny and that, cuz that would sort of fit the title, but really somebody who's working against these otherwise sort of natural forces of entropy, which tends to disintegrate things over time. <Laugh>.
(00:41:20):
Okay. Exactly as we predicted <laugh> three days ago, b BBC News headlined their signal would walk from UK if online safety bill undermined encryption with the subhead. The message encrypting app signal has said it would stop providing services in the UK if a new law undermined encryption signals President Meredith Whitaker told A B B C that if they were forced to weaken the privacy of their messaging system under the online safety bill, the organization quote would absolutely 100% walk. Of course, the government said that his proposal is not a ban on end-to-end encryption, but the bill which was introduced by Boris Johnson is currently going through Parliament. And as we recently covered in detail under the revisions proposed by this new legislation, companies would be required to scan messages on encrypted apps for child sexual abuse, material language suggestive of grooming or terrorism content.
(00:42:48):
Whatsapp previously told the B BBC that it would also refuse to lower its security, and I put that in air quotes for any government in the case of WhatsApp. The question might come down to the definition of the term security but the folks behind signal are likely to be far more clear about that. The BBC's coverage reminds us that, you know, the government and prominent child protection charities have long argued that encryption hinders efforts to combat online child abuse, which they say is a growing problem. The UK's home office said in a statement, it is important that technology companies make every effort to ensure that their platforms do not become a breeding ground for pedophiles. The home office added. The online safety bill does not represent a ban on end-to-end encryption <laugh>, but makes clear that technological changes should not be implemented in a way that diminishes public safety.
(00:43:56):
Yeah. Especially the safety of children, online children think of the children. That's right. It is not a choice between privacy or child's safety. We can and we must have both. Right? <laugh> We can because we say we can. Right. We're willing to go as far as to change the definitions of words <laugh> in order to have both the safety of our children and total privacy for everyone, even though we may need to change the meaning of total. Yeah. But just, just a little bit <laugh>, you know, that, that pesky math is so annoyingly absolute. Yes. After all, we create laws, that's what we do. Unfortunately, not the laws of nature or of mathematics, but still this is what we want and we're used to getting our way. So the UK's Child protection charity, the N S P C C said in reaction to signal's announcement, tech companies should be required to disrupt the abuse that is occurring at record levels on their platforms, including in private messaging and end-to-end encrypted environments.
(00:45:15):
But the digital rights campaigners on the other side, the open rights group said this highlighted how the bill threatened to undermine our right to communicate securely and privately. The signals Ms. Whitaker said, back doors to enable the scanning of private messages would be exploited by malignant state actors and create a way for criminals to access these systems. When asked if the online safety bill would jeopardize signals ability to offer a service in the uk, she told the B BBC quote it could and we would absolutely 100% walk away rather than ever undermine the trust that people place in us Good to provide a truly private means of communication. Right on. She said, we ha we have never weakened our privacy promises and we never will. Good. Yep. Matthew Hodson, chief Executive of Element, a British Secure Communications company, said that the threat of mandated scanning alone would cost him clients.
(00:46:26):
He argued that customers would assume any secure communication product that came out of the UK would necessarily have to have back doors in order to allow for illegal content to be scanned. Matthew added that it could also result in a very surreal situation where a government bill might undermine security guarantees given to customers at the Ministry of Defense and other sensitive areas of government. Hmm. He said that his firm might have to cease offering such services. Hmm. And that raises a great point. Would the most sensitive users within the government also be consenting to having all of their communications intercepted, scanned, and possibly forwarded to a central clearing house for human oversight? That seems unlikely. As for child safety signals, Ms. Whitaker said quote, there's no one who doesn't want to protect children. Some of the stories that are invoked have been harrowing. When asked how she would respond to arguments that encryption protects abusers, Ms. Whitaker pointed to a paper by Professor Ross Anderson, which argued for better funding of services working in child protection and warned that quote, the idea that complex social problems are amenable to cheap technical solutions is the siren song of the software salesman <laugh> unquote. Wow. Yeah. The idea that complex social problems are amenable to cheap technical solutions is the siren song of the software salesman.
(00:48:19):
So there's no question that the issue of child safety is real, but terrorism content was also mentioned. And doesn't everyone also appreciate that no government, no matter how respectful of its citizens inherent and often constitutionally guaranteed privacy rights is comfortable with not having some capability for oversight over its citizenry when it believes that such might be needed? As I've noted of our own constitutional government in the us, the constitution's guarantee for privacy is conditional. Courts are able to issue search warrants when presented with probable cause. We've been watching the approach of this slow motion collision for years. So it's gonna be very interesting to see how this all shakes out. We know that Signal and Telegram and three MA will not capitulate. There's just no way they would. But it's difficult to see how meta's various services Google with Android and Apple may not be forced to go along rather than lose access to those huge markets.
(00:49:34):
Apple already demonstrated a willingness to find some compromise by performing that local fuzzy hash scanning. Of course, the backlash from that was epic. Ultimately I think governments are probably gonna win this legal battle since they're the ones who write the laws and thus it's possible for them to delineate what behavior is legal and what is not. At that point, any use of fully secure end-to-end encrypted solutions will be outlawed. At which point, as we know, only outlaws will be using them so downloaded now. So you too can be an outlaw <laugh>. That's right. Get your soon to be illegal to use software. Yeah. Yeah. Oh, I do know some people actually who have purchased guns cuz they were worried that, you know, they were soon gonna be outlawed. It's like not only, you don't have to worry about that in the us not in the US baby.
(00:50:32):
Okay. okay. More pi pie troubles. Remember last week how I felt that I needed to at least mention the continuous background of ongoing attacks on open source repositories and registries. Well, last Friday the security firm Phum posted some news regarding the pii that's, you know, the Python package index. Their postings headline was Phum discovers aggressive attack on pii, attempting to deliver a rust executable. They wrote on the morning of February 23rd, 2023, phylum's automated risk detection platform started lighting up with another series of strange publications on pii. After digging into it, we were able to link it to another cast, another smaller campaign from January last month. First they said, we can confirm that this is an ongoing attack. As we worked on this writeup, we saw the list of packages published go from a few dozen to over 500. I know the most recent packages appear to be getting published at around one every four to eight seconds.
(00:51:57):
So we suspect that this may continue for some time. You can look at the package publication section at the bottom of this post to see the packages. We've seen as of the publication of this post, we've already seen 1,138 malicious packages published. Anyway. They go on to explain in detail the nature of the malware. The short version is that the malicious packages connect to a Dropbox account to download and install a rust based malware strain. Phum says the attacker appears to be the same group that was previously spotted by Fortinet and Reversing Labs the week before in a separate smaller campaign. Now, as I was saying last week when we talked about this, our open source repositories are now under more or less constant attack. And Leo, as you commented last week, the industry, you know, needs to come up with some solution to the poisoning of our open repositories.
(00:53:01):
The only solution I can see is a future where internet identity and reputation can be rigorously established and verified. And I know people love the freedom of using synthetic online identities and monikers a and I think that's a hundred percent fine, so long as they don't also want the, that accrue from being known and trusted. At least at the moment. It's unclear how it's po possible to have both. At the moment, we have neither. So again, I just, you know, we want this stuff to be open, but you know why we can't have nice things in the interest of giving credit where it's due the often in the doghouse Taiwanese hardware vendor qap, right? The manufacturer of the always apparently in trouble NAS devices, which are exposed to the internet on Friday announced the launch of its own bug bounty program. Yay.
(00:54:18):
Vulnerabilities relating to qap operating systems, applications and cloud services are all in scope and rewards can go up to US $20,000. They do still need to find some way of keeping their devices patched when problems are found. But we've, you know, as we've just seen with VMware, they're not alone in having that problem to solve. I think that tomorrow's systems that is globally some, one way or another, we're all gonna have to phone home just as our consumer operating systems have all been doing for some time. And there will either have to be an autonomous upgrade and reboot facility or some reliable notification path to the devices administrators. This problem needs to get solved, but finding and fixing those problems comes first and QAPs Bounty, while not huge, is a clear step in the right direction.
(00:55:21):
And Leo, let's talk about the club for a minute. <Laugh>, I'm gonna tell, I can tell talk. Yeah, I know. Take a break. I know. And you get a little thirsty. Yeah. And and then we're gonna talk about a, an unbelievable bug, which we have found in motherboard biases, which is gonna ne necessitate a change in spin, right? Wow. and then we're gonna talk about what the nsa tells us we should do at home. Okay? And of course, for those of you in the club, this will be merely a thank you. And back to Steve, the rest of you <laugh>, I want to give you a little pitch. One of the reasons people join the club is because you don't get any ads including this ad. They're all cut out. So you just get the content in the show. And the reason we do that is if you pay us seven bucks a month, we don't need to sell ads.
(00:56:12):
We don't need to sell your attention. And I think that's a fair trade, but that's not all you get with Club Twit. You also get access to one of the best social networks ever. The Club Twit Discord inside our Discord are all, you know, thousands of other Club Twit members. Sure. They're talking about the shows when the shows are on. There's a Security Now segment or a section on the Discord. But there's also sections on anime and comic books and cars, travel, photography, coding, everything that our smart and interesting audience is interested in. And so it turns out hanging out in the, in the Discord is a 24 7 thing. I mean, it's just so much fa okay, you can sleep. So, you know, let's make it 16, seven, how about that? But it's still a really great place to hang. You get that too. So ad free, you get the Discord, you get events too in the discord that aren't anywhere else. For instance, we have shows that like the boy, it's really blown up big. Let me see if I can make this smaller so you can, so you can see it. We have in the Discord, we have shows that we don't put out as as podcasts. For instance, here's the <laugh>. I don't know what's going on there. <Laugh>.
(00:57:36):
We have animated gifts, which really make the discord a lot of fun. But we should put out shows that are not podcasts like Micah Sergeants, hands on McIntosh, HandsOn Windows with Paul Thout, the Untitled Linnux Show. We have a lot of events that our community manager puts together. Mr. Aunt Pruit, for instance. Aunt has gotta ask me anything on Thursday with our car guy Samal Sam. So I know a lot of you be interested in that Stacy's book club every other month. This month it's gonna be the Sea of Tranquility. Actually it's in April. Also coming in April, an A inside twit with Victor Bog. Not one of our great editors, Alex Wilhelm, you know him from Tech Crunch. And as many appearances on Twit will be doing an Ask Me Anything in May and from Floss Weekly. Sean Powers will be doing an ask Me Anything. But there's more events coming all the time. <Laugh>, that's Mean <laugh>.
(00:58:35):
If, if, if that's as if that weren't enough. There's also the twit plus feed, which contains before and after show conversations little tidbits and twits and all sorts of stuff. You're also supporting. And this maybe is the most important thing you're doing when you give us your $7. You're supporting everything we do. There's only one ad in this show. There was only one ad in Mac Break Weekly that's barely breakeven, might not even be breakeven. It's expensive to run this network and to give you all this great content. And if you appreciate it, I'd appreciate it if you'd support us. Podcast advertising is falling off a cliff. Don't know why. It's not just us, it's everybody. NPR had to lay off 30% of its or sorry, 10% of its staff cuz they lost 300 million in podcast advertising last quarter.
(00:59:23):
We don't wanna do any layoffs. And if you join the club, we won't have to go to twit.tv/club twit. It supports what we do. If you can't afford it, I understand completely. We've still got all the free programming this show add support it as always. But if you like what we do and you want to keep it going, you want to hear new shows, we launched this week in space in the club and, and then put it out in the public. This is the best way, the only way forward. I think at least for the next few years, probably forever. Podcasting needs the support of its listeners, people like you. We, we, right now we have I think 7,000 Club members out of 700,000 unique listeners every month. That's 1%. I'd like to do more, maybe get it to three, four, 5%.
(01:00:09):
That means you twit tv slash club twit. We have corporate memberships as well. If you wanna get your company involved, twit.tv/club twit. And I thank you so much to all of our club members because your help has really made a lot possible with twit. And we want to keep going. We've been doing this for, what is it, 18 years now? We're in year 18, so coming up on 19, I'd like to make it to 20. Hey everybody. Leo LaPorte here. I'm the founder and one of the hosts at the TWIT Podcast Network. I wanna talk to you a little bit about what we do here at twit because I think it's unique and I think for anybody who is bringing a product or a service to a tech audience, you need to know about what we do here at twit, we've built an amazing audience of engaged, intelligent, affluent listeners who listen to us and trust us when we recommend a product.
(01:01:08):
Our mission statement is twit, is to build a highly engaged community of tech enthusiasts. Well already you should be, your ears should be perking up at that because highly engaged is good for you. Tech enthusiasts, if that's who you're looking for, this is the place we do it by offering 'em the knowledge they need to understand and use technology in today's world. And I hear from our audience all the time, part of that knowledge comes from our advertisers. We are very careful. We pick advertisers with great products, great services with integrity and introduce them to our audience with authenticity and genuine enthusiasm. And that makes our host Red Ads different from anything else you can buy. We are literally bringing you to the attention of our audience and giving you a big fat endorsement. We like to create partnerships with trusted brands, brands. Were in it for the long run, long-term partners that want to grow with us.
(01:02:08):
And we have so many great success stories. Tim Broom, who founded it Pro TV in 2013, started advertising with us on day one, has been with us ever since. He said quote, we would not be where we are today without the Twit network. I think the proof is in the pudding. Advertisers like it Pro TV and Audible that have been with us for more than 10 years, they stick around because their ads work. And honestly, isn't that why you're buying advertising? You get a lot with twit. We have a very full service attitude. We almost think of it as kind of artisanal advertising, boutique advertising. You'll get a full service continuity team, people who are on the phone with you, who are in touch with you, who support you from, with everything from copywriting to graphic design. So you are not alone in this.
(01:03:01):
We embed our ads into the shows. They're not, they're not added later. They're part of the shows. In fact, often they're such a part of our shows that our other hosts will chime in on the ads saying, yeah, I love that. Or just the other day, <laugh>, one of our hosts said, man, I really gotta buy that <laugh>. That's an additional benefit to you because you're hearing people, our audience trusts saying, yeah, that sounds great. We deliver always overdeliver on impressions. So you know, you're gonna get the impressions you expect. The ads are unique every time. We don't pre-record them and roll them in. We are genuinely doing those ads in the middle of the show. We'll give you great onboarding services, ad tech with pod sites that's free for direct clients. Gives you a lot of reporting, gives you a great idea of how well your ads are working.
(01:03:50):
You'll get courtesy commercials. You actually can take our ads and share them across social media and landing pages. That really extends the reach. There are other free goodies too, including mentions in our weekly newsletter that sent to thousands of fans, engaged fans who really wanna see this stuff. We give you bonus ads and social media promotion too. So if you want to be a long-term partner, introduce your product to a savvy engaged tech audience. Visit twi.tv/advertise. Check out those testimonials. Mark McCreary is the c e o of authentic. You probably know him one of the biggest original podcast advertising companies. We've been with him for 16 years. Mark said the feedback from many advertisers over 16 years across a range of product categories, everything from razors to computers, is that if ads and podcasts are gonna work for a brand, they're gonna work on Twitch shows.
(01:04:46):
I'm very proud of what we do because it's honest, it's got integrity, it's authentic, and it really is a great introduction to our audience of your brand. Our listeners are smart, they're engaged, they're tech savvy, they're dedicated to our network. And that's one of the reasons we only work with high integrity partners that we've personally and thoroughly vetted. I have absolute approval on everybody. If you've got a great product, I want to hear from you. Elevate your brand by reaching out today@advertisetwit.tv. Break out of the advertising norm. Grow your brand with host red ads on twit.tv. Visit twit do TV slash advertise for more details or you can email us, advertise@twit.tv if you're ready to launch your campaign. Now, I can't wait to see your product, so give us a ring. Okay, somebody's gotta pay for Steve's hydration. Go right in. So I haven't talked about <laugh>, I haven't talked about spin right at all for several weeks because I didn't have any significant news to share.
(01:05:50):
But as a result of the work and discoveries over the past week, I have news today which will more than make up for my previous week's silence. A major discovery which had been stymieing. The project for weeks has been solved for the past many weeks. I've been tracking down, as I have mentioned last time I talked about spin, right. Various sources of spin Wright crashes. I've discovered various sorts of misbehavior from doss and motherboard biases. They've been altering values in registers that they assume wrongly, that others won't be using. You know, that's against every rule of good citizenship. You always put things back the way you found it when, when, when you're done using them. But in this case is these things weren't, the only way I can explain this behavior is that they're using, you know, for example, the upper half of 32 bit registers, figuring that in a 16 bit environment, no 16 bit app would notice, but spin right is now largely 32 bit code, and it makes constant use of all of those extra 32 bit resources.
(01:06:57):
And in other cases, they're just not bothering to preserve any part of a register. So a lot of the work I've been doing recently has been defensive computing. Someone suggested that term in, in our, in our development group. And I thought, well, maybe survival computing is the better term because I mean, I have to do it in order to keep spin, right? Running. So spin right already works without trouble for nearly everyone. But for those for whom it does not work, you know, they have my attention because I'm never sure whose fault the problem is. And I need to d deter it needs to determine that, you know, is it something I'm doing that I need to fix or is it something outside of my control? And there's no reason Spin Wright shouldn't be able to protect itself from anything that a system might throw at it.
(01:07:52):
Although that was recently challenged. One Canadian spin Wright tester, Andre was able to get Spin Wright to crash for him reliably. He had a system with a couple of internal drives and 160 gigabyte U SB drive connected. The USB drive was being marked red by Spin Wright, which is a new feature. There's a, there's a whole, I mean, spin, right? Six users are gonna, they'll recognize it, but boy, I mean, the last several years have really changed spin, right? For to moving it from six to six one. Anyway the, the USB drive he had was being marked red, meaning that during its initial appraisal of the drive spin Wright had found something that wasn't right. You know, that's something that we've been seeing with drives that are quite near death. When the user attempts to select the drive for use, they'll receive a pop-up explanation of exactly what's wrong and when possible be given the option to proceed to use that drive anyway, but that 160 gig drive was being marked red.
(01:09:01):
That wasn't the problem. The problem was that shortly after enumerating those three drives, spin Wright would intercept its own attempt to execute an illegal X X86 processor instruction, an illegal op code. That should never happen. I don't recall what made me suspicious, but I first asked Andre just to try unplugging that damaged u SB drive and sure enough, no crash. Then with that drive reattached, I provided Andre with an old school DOS utility called EAT mem. Eat mem simply consumes some amount of RAM memory and then drops back to Doss. Back in the day. This was used to stress test programs by subjecting them to limited memory situations. But it also has the side effect of changing the location in ram, where Doss will load subsequent programs since it eats memory from the bottom up. And sure enough, by eating various amounts of memory before running spin, right, spin rights, crashing behavior would not occur or it would occur differently.
(01:10:22):
Even with that, that 160 gig red marked drive connected around the same time. One of our spin right testing participants, a guy named Paul Farer, who also knows how to write Doss programs, was experimenting with his own o on his own with a similar crash that he and another user were both seeing that other user had attached a one terabyte USB drive to his machine, and it was crashing spin right when he, when he tried to run it. Paul hypothesized that the trouble might be caused by Spin Wright attempting to read above the 1 37 gigabyte region of a drive. I have no idea how that occurred to him, but it turned out to be prescient. Hundred 37 gigabytes is, is one of those many size limitations that we as an industry were constantly plagued with during the PC industry's early growth over and over and over.
(01:11:28):
I mean, it's almost comical in retrospect. We kept outgrowing every upper limit that we assumed would never be exceeded. The classic story was that the 16 bit Apple two had a maximum of 64 kilobytes of main, of main ram memory. Yes, 64 K of main RAM memory. And when the I B M PC came out with its initial maximum of 640 kilobytes, so exactly 10 times as much as the Apple two, the story was that during a trade show in 1981, bill Gates said, we'll never need more than six 40 k. Now today, bill doesn't recall ever having said that, but you know, it's apocryphal in the industry. You know, whether or not he did, although, you know, today it may seem ludicrous. I can easily imagine having been active in the PC industry back at the time that see that it was seemingly reasonable to say that.
(01:12:40):
And that's the point. These were always reasonable seeming limitations because none of us who were in the middle of this could have foreseen. What has happened since the early I d E drives had sizes in the hundreds of megabytes or maybe a few gigabytes, if you know, like you could get some of those. And they were really expensive, you know, like a four gig drive. So the designers of those drives repurposed the addressing bits, which had been used by the original cinders cylinders, heads and sectors registers to scrounge up a total of 28 bits that they could use to linearly address the sectors on an I D E drive. This was called L B A for linear block Addressing the use of those 28 bits to address sectors meant that a drive could have at most two to the power of 28 total physical sectors, since sectors were five 12 bites each, that meant that the maximum size of those 28 bit L B A drives would be 137 gig.
(01:13:54):
But you know, back then 137 gigabytes, no one would ever be able to create a drive that large, let alone have that much data that needed to be stored. I mean, come on, that's 137 billion with a, whoops. So Paul's intuition was that spin rights code was somehow being corrupted when it attempted to access sectors at the end of the drive. If a drive was larger than 137 gig like that 160 gigabyte drive that Andre had was and accessing sectors at the end of the drive is one of the things that Spin Wright does when it's sizing up a drive before listing it for use by its user. So Paul and I each independently wrote testing utilities to better understand what was going on. And what we discovered over this past weekend was a bit astonishing. I ended up writing two utilities. The first one was called BIOS test.
(01:15:01):
It BIOS test first filled all of the systems main ram memory that wasn't already in use by Doss and the bios and buffers and the program itself with a deterministic pseudo random pattern. Then it simply used the systems bios to read several sectors from the front of the drive and from the end of the drive, after each test read, it would re-scan all of main memory looking for the first mismatching of data. It was looking to see whether reading any sector from a drive through the bios would cause the bios to alter main memory. And sure enough, after reading the last sectors of larger than 1 37 gigabyte USB drives on some other boards, it found main memory mismatches. Reading sectors from the front of the drives never caused any problems, but reading any sectors whose linear address had more than 28 bits would actually damage the data stored in main memory.
(01:16:11):
The u sb support in those bios was seriously buggy. During what Spin Wright calls drive discovery and enumeration, it goes out to the very end of every drive it can locate to perform reading and writing confirmation and confidence testing. It's safest to do that out there out at the end because the, the very ends of drives are usually empty and don't contain any user data. In fact, partitions don't tend to go all the way out to the end. They, they have lot like a a, a shorter wrap factor to, to be aligned. But when Spin Wright was doing that on u SB connected drives on motherboards with those broken U USB bios, bugs in the bios were blasting spin right code, which was then causing it to crash. Whereas BIOS test checked a few sectors at the front and back of every bios drive.
(01:17:07):
The second utility I wrote Bioscan, read every sector of a user specified bios drive it also filled memory with a pseudo random test pattern. Then it would scan the entire drive from front to back while Rescanning main memory. Anyway, I have a bunch more of this story in the show notes. I, I've taken up enough of everyone's time. We found a bad bug that some bios have, which occurs when an attempt to read the end of drives larger than 1 37 gigabytes happens. So we've fixed the problem. We're we're going to clamp spin rights access at 137 gigabytes for u SB connected drives until we get to spin right seven because it is not safe for spin right to go any further than that. There's no, there's no reliable way to test whether a bios is buggy or not. They're, they're scattered around the spin, right users that we have.
(01:18:10):
And this is, even though it's a large bunch of users, it's a small sample size. So we're gonna get spin, right? Six one finished, it's, well, one less source of crashing now exists. And the, the first thing I'm adding to spin right seven is native support for U S B host controllers, which will then release th this temporary limit on u SB drive size and also dramatically speed up the r the, the, the, the spin right's ability to use u SB drives in the same way that it has sped up sat and parallel drives running them now like at their absolute maximum speed, they're able to function. So it was an interesting adventure with the help of lots of te of of testing. We were able to track down a bizarre problem, which has gone unseen in the industry.
(01:19:06):
One, one person did find some reference to a, a boot manager saying that you should use it at the beginning of drives or not on drives larger than this 137 gig because of I some bugs that were in bios. But, you know, it certainly hasn't been widely known. I did wanna mention a, an interesting programmer oriented humble book bundle. We've talked about those in the past. And in fact, I found that I, because it's got a, a crazy long U R L I assigned it one of G R C'S shortcuts, and I decided to use the, the shortcut bundle, B U N D L E, which had been taken, I used it before in, in 2021 on a different humble bundle. So we're reusing the same shortcut. It's an 18 book humble bundle of programmer related book. Anyway take a look at it.
(01:20:08):
There's a bunch of programming books by Randall Hyde who's, you know, legendary in the, in in programming circles and a bunch more. So grc.com/bundle, B U N D L e if you are interested and you know, they're as, as Leo and I were talking about this before we began recording you know, they're not absolutely amazing books, but they're the 18 of them, you, you, you pay what you want for them. The money goes to support the E F F. And I can, you know, there are some good ones in the collection as is often the case. Just think like a programmer is a classic and it's got that. Yes. Yeah. And it's got that assembly language book too, which you like. And this if you wanna learn enclosure. Everybody, everybody loves this book, although I think this is online for free.
(01:21:01):
This is all no starch press. They do great stuff. I really love no starch presses stuff. I have a lot of their books. Yep. GRC dot grc sc slash bundle. Okay. So surprisingly the NSA has offered some home security best practices advice. Last Wednesday, the National Security Agency, you know, our NSA published an attractive and end user accessible nine page PDF d f loaded with tips for helping to secure a home network environment. And Leo, it's our shortcut of the week. So if you wanna scroll through it on, on the screen while I'm talking about it GRC sc slash nine 12 GRC sc slash nine 12. Anyway it is really good and I wanna share and comment on some of what the NSA has suggested. Our long, our longtime listeners will feel right at home, so to speak, with everything that the NSA wrote, they let off with three major key points, upgrade and update all equipment and software regularly, including routing devices, exercise secure habits by backing up your data and disconnecting devices when connections are not needed, and limit administration to the internal network.
(01:22:30):
Only the, the, these, these three points are actually pulled out of the, of, of the larger piece, but, you know, clearly keep your stuff up to date, do secure things and do not open anything to remote administration. They also said, and I thought this was interesting, I OT devices on a home network are often overlooked, but also require updates, enable automatic update functionality when available if automatic updates are available. Download and install patches and updates from a trusted vendor on a monthly basis. So it's interesting that the nsa, you know, they too see the threat posed by our out of date or defective IOT devices. Of course, the question is often, who are you gonna call to update some random i o t light switch or wall plug? But moving forward, it would be good to see future devices based on open standards and platforms and for there to be some sort of certification systems in place.
(01:23:42):
We have a long way to go, you know, but such work is underway. Okay. And this one was interesting. They wrote, your internet service provider may provide a modem slash router as part of your service contract to maximize administrative control over the routing and wireless features of your home network. Consider using a personally owned routing device that connects to the I S P provided modem router, in addition to modem router features to create a separate wireless network for guests for network separation from your more trusted and private devices. Okay, now that was a little bit surprising. They're saying even if your internet service provider offers a modem router as part of the service package, get your own that you control and manage and use it to connect your network to the provider's bandwidth. Again, some sound advice and on router guidance, they say your router is the gateway to your home network.
(01:24:52):
Without proper security and patching, it is more likely to be compromised, which can lead to the compromise of other devices on your network as well. To minimize vulnerabilities and improve security, the routing devices on your home network should be updated to the latest patches, preferably through automatic updates. These devices should also be replaced when they reach end of life for support. This ensures that all devices can continue to be updated and patched as vulnerabilities are discovered. Okay, how many times have we seen companies explaining that they won't be offering updates to fix known critical remote code execution problems for older devices because they are e o l, you know, end of life. So anyone still using those devices is s o L. And we've often seen like inventories of these end of life devices still out exposed on the public internet and they're never going to get patched when selecting a router.
(01:26:03):
This suggests an important criteria that's easily overlooked, and that's the active and supported service life that has historically been provided by various competing vendors. If this criteria were to become a popular advertised, you know, selection, it would put more pressure on vendors to keep older devices supported longer. Yeah, even though it might mean reduced sales in the future due to the longevity of previous products, which were still supported and going strong. I don't know that you know, anybody is actually yet buying a new device to replace a working old device simply because the old device is no longer receiving updates. I don't think most people even know whether, you know, devices are receiving updates or not. But I I've appreciate the NSA saying, you know, if a device you've got is so old that it is no longer receiving updates, and if a problem were found that could never be fixed, and if you care about security, these things aren't that expensive anymore.
(01:27:15):
The NSA also talked about W P A three. We briefly touched on this next generation wifi six and W P W P A three encryption, but we haven't yet given it a deep dive and it's probably time for us to do so. It's had a somewhat slow liftoff since the wifi alliance's wpa. A certification process started back in 2018, so, you know, between four and five years ago. But wifi six and W p a three capable devices are here now. So we'll get around soon to doing a podcast. Here's what the NSA wrote, they said to keep your wireless communications confidential, ensure your personal or I s P provided W A P is capable of wifi protected access. Three. If you have devices on your network that do not support WPA three, you can select WPA two slash three instead. This allows newer devices to use the more secure method while still allowing older devices to connect to the network over WPA A two.
(01:28:24):
When configuring w WPA A three or WPA two slash three, use a strong passphrase with a minimum length of 20 characters when available. Protected management frames should also be enabled for added security. Most computers and mobile devices now support W A W P A three or do if you're planning to purchase a new device, ensure that it is W p A three personal certified change the default service set identifier, you know, the S S I D to something unique. Do not hide the S S I D as this adds no additional security to the wireless network and may cause compatibility issues. All of that is true. I'm, I was very impressed as I was reading through this that you know, the degree to which the NSA got it. So as I said, we'll do a wifi six podcast soon. Seeing this next one, raise an eyebrow.
(01:29:28):
Since everyone knows that I worry about the day. A widely used i t device goes rogue. The NSA wrote implement wireless network segmentation. They said leverage network segmentation on your home network to keep your wireless communication secure. At a minimum, your wireless network should be segregated between your primary wifi guest wifi and I o T network. Holy, you've been saying this for years, but it's interesting to hear them recommend this to normal people. Cuz I don't think normal people know how to do this. I know. You know, and, and, and they finish saying this segmentation keeps less secure devices from directly communicating with your more secure devices. You know, as we know you know, I've been promoting multi nick routers, which were able to do that. And some of the more recent wifi routers are beginning to offer stronger segmentation options as well.
(01:30:35):
So I would say that's something to look for when you're shopping for a new wifi router is check out and see if it offers built-in segmentation that will make it a lot more accessible to you know, average user. What do what they call it? What do they what? Is there a name that they give it or that's a good question. I think, I think that the Aus router I'm using it definitely has a guest wifi, but I think it has multiple guest wifis. And so you could, and, and you are able to ke to keep them from talking to each other. So that would mean you could give your second guest wifi, use that for your I o T stuff. Okay. Yeah. The problem I think a lot of people will have is that they can't then, I know, use devices on their main network to control the IOT devices.
(01:31:26):
And you and I and our audience probably knows how to do sophisticated firewall rules to allow that, but you have to know it. That's really, you know, black diamond stuff, right? That's pretty advanced. Yeah. But again it was, it was amazing to see the NSA saying this and, you know, our and our users, you know, get a little additional impetus behind that too. Well, and everything, it looks like everything in this NSA document you would agree with a hundred percent, right? Yes, absolutely. In fact, there's something I've never recommended that I agree with it. We'll get to in a second. Oh, so what about the presence of personal assistant technologies and worries over eavesdropping? Well, not surprisingly, the NSA is not a big fan of things with microphones, <laugh>, unless it's theirs <laugh>. Unless it is less, unless they're on the other end. Exactly. So they wrote beware that home assistance and smart devices have microphones and are listening to conversations even when you are not actively engaging with the device.
(01:32:33):
If compromised, the adversary can eavesdrop on conversations, limit sensitive conversations when you're near baby monitors, audio recording toys, home assistance, and smart devices consider muting their microphones when not in use. Wow. For devices with cameras, you know, laptops monitoring devices and toys, cover cameras when you're not using them. Disconnect internet access if a device is not commonly used, but be sure to update it when you do use it. So I got a kick outta that one. And all that security advice falls nicely under the umbrella of generally sound if maybe a little paranoid security advice following that under the topic of general security hygiene, they add to minimize ransomware risks, backup data on external drives or portable media disconnect and securely store external storage when not in use, you know, take it offline. Minimize charging mobile devices with computers. Use the power adapter instead. Avoid connecting devices to public charging stations.
(01:33:46):
Leave computers in sleep mode to enable downloading and installing updates automatically, regularly reboot computers to apply the updates, turn off devices or disconnect their internet connections where they're not, when, when they will not be used for an extended time, such as when going on vacation. In other words, think security at all times and try to never take it for granted. You know, it's sort of the broader equivalent of what has happened to email where it's no longer ever safe, unfortunately, to assume that all email is legitimate and that links can be clicked on without careful scrutiny. It's a sad state, but it's the state we're in and everyone knows that I love this one. Limit administration to the internal network only. They said disable the ability to perform remote administration on the routing device only. Make network configuration changes from within your internal network. Disable they, this is them disable universal and play these measures.
(01:34:59):
Help close holes that may enable an actor or an actor to compromise your network. And Leo, I do kind of wonder maybe if they listen to the podcast and there was one piece of advice that makes sense, but I have never recommended, they said schedule frequent device reboots. They wrote to minimize the threat of non-persistent malicious code on your personally owned device. Reboot the device. Periodically malicious implants have been reported to infect home routers without persistence. At a minimum you should schedule weekly reboots of your routing device. Well, that seems a little often, but okay. Smartphones and computers, regular reboots help to remove implants and ensure security. I mean, it's true, they do. What's interesting about this advice is that as we know, many forms of malware are ram resident only. They never write anything to Nonvolatile media. Some routers are ever nev, almost never rebooted.
(01:36:08):
So malware authors probably figure that there's no reason to bother writing it to nonvolatile memory and arranging to get it to start where it's a little more visible, you know, in, in the startup script. And we know that in well-protected environments, riding to disk can trip all sorts of monitoring alarms, you know, and some malware might want to disappear after a reboot so that it's larger network of devices can remain hidden. So if it's not necessary for something to survive a reboot, malware might well choose not to. Consequently, indeed, a reboot will permanently flush RAM based malware from the system. Okay. Now, if the way such malware originally got into the system in the first place, you know, and, and then obtained its foothold in ram if that's not closed off and resolved, then it might come back before long. But yeah, re reboots are inherently cleansing.
(01:37:15):
I think that was a great point and it's one I've never talked about before. So, okay. Those were just some of the highlights that I thought were the more interesting, a little bit surprising in some cases and insightful, but there is much more than those in the nine page document than you know, what I've just shared. And the entire document is so good that I think everyone listening would benefit from it, you know, from at least scanning and probably also by recommending it to others, it has the additional pedigree of bearing the official seal of the National Security Agency, you know, which might help e everyone's non-security now listening friends sit up a little bit and take it seriously. And as we've seen, it's far from being the typical useless piece of, you know, say nothing bureaucratic nonsense as friendly and useful as the document is.
(01:38:12):
It's line and a half wrapping around r l is not nearly as friendly. So this week's GRC shortcut is that you can find it at GRC sc slash nine 12 since this is episode 912, you know, and big props to the NSA for assembling something so useful and largely so actionable. If nothing else, the nature of the recommendations would help someone who doesn't live in the security realm to realize the way security conscious professionals think. And that would, you know, probably be surprising to many people. It's like, wow, you're really that paranoid <laugh>. I'm sorry. Yeah. Yeah. I'm gonna share this on ask the tech guys. This is really really good. It is a great, it is a great document. Yeah. Yeah. And I, yeah, I can't think of anything I would disagree with. There's some things that maybe are not easy to implement.
(01:39:13):
Yeah, I mean, like going around, you're gonna put like cover up the microphone holes Yeah. On various devices. I mean, baby monitors we know get hacked, but yes, no device from Amazon or Google to my knowledge has ever been hacked. Most people are more afraid of Amazon and Google listening in which they don't. Or Siri. I I think that the, the big three, right? You, you don't know of any hacks of them exploits with them. No, of course. If you had an exploit, you wouldn't tell anyone. That'd be a good nation state exploit. I know a lot of it's surprisingly large number of people that we work with, sophisticated users will not have these devices in their homes. I have an Echo right there, a Google assistant right there. I have Siri right here. You got it in your pocket with your phone.
(01:40:02):
But they just say no. Nope, nope. Not gonna do it. Yep. Very interesting. Great show as always, Mr. Gee. Mr. G Steve Gibson is@grc.com, the Gibson Research Corporation. If you go there, you can get a copy of spin right now, get it while it's hot. You get 6.0 today, you'll be getting 6.1 now bug free. Right? <laugh> one. Well, one, one fewer class of very serious bugs. That's a weird bug. Wow. Oh my God. I mean, just it's blasting up up to a 64 K block of Ram was, was being changed. And, and you know, it's the, the, the, the, the problem is the fact that it's this 28 bit barrier. We don't know that bios that don't destroy Ram properly address sectors past that. They might be wrapping around. Oh wow. Back to Sector zero. Oh yeah. When, when you go past. So I just decided out of an abundance of caution.
(01:41:01):
Yeah. We're, we're gonna, I'm gonna allow Spin Wright to work on the first 137 gig of anything you attach by U US B, but not past that because it, we just can't prove that it's safe. Right. And what that does is that gets spin right out the door sooner. And I'm immediately switching to spin. Right. Seven. I'm gonna, and, and the Oh, good spin, right? Oh yeah, that's, I'm not taking a vacation. I'm, I'm, as soon as six one is done, I'm starting on seven. I'm very excited. This man is strong. Like Ox never stopping, constantly going forward. So good news. Get six. Oh, now get six one the minute it comes out and we'll talk about seven. That's, and I'll be working on seven, not imminent. I don't think you'll be hearing about it. Yeah. Good, good. Grc.Com. While you're there, you course can pick up a copy of the show.
(01:41:49):
Steve has two unique versions of 16 kilobit audio version for the bandwidth impaired. Beautifully written transcripts by Elaine Ferris. So you can read along as you listen or search. That's all@grc.com. We have 64 Kilobit audio and video at our site, twit tv slash sn. You can leave questions for steve@hissitegrc.com slash feedback. He's also on Twitter at sg grc and his dms are open. So comments and questions are fielded there as well. Don't expect a personal reply, but he might use it in the show. You can watch us do this show every Tuesday about one 30 to 2:00 PM Pacific. That's four 30 pm to seven 30 or 6:30 PM Eastern Time. That's 2130 UTC live. Do twit, do TVs where the feeds are live audio or video that's kind of an aggregator of our YouTube and other, and Twitch and all that. So you can pick the feed you want audio or video.
(01:42:48):
If you're watching Live Chat Live and I irc that's open to all@irc.twit.tv. You can use your browser. You don't need an IRC client. We also have of course our Discord for club members. They're chatting in there right now after the fact. We have copies of the show, as I said, twit TV slash sn. There's also a dedicated YouTube channel for security now. But the best way to get this show probably is subscribe. Steve has an S feed and I have an r s s feed. Pick one and subscribe. That way you'll get it automatically as soon as the show is ready later in the day. Thank you Steve. Okay, my friend. I will be talking to you first Tuesday of March, March in like a lion. Wow. And it is, it's raining out like a lamb. We hope I'll be actually going on a vacation at the end of March. So I'm, I'm looking forward to these days flying by. Thanks Steve. We'll see you next time on Security now. Hey buddy. Bye.
Jason Howell:
Do you wanna hear about the latest news happening in the tech world from the people who write the article sometimes from the people who are actually making the news? Well, we got a show for you here at twit.tv. It's called Tech News Weekly. Me, Jason Howell, and my co-host Micah Sergeant. We talk with some amazing people each and every Thursday on Tech News Weekly, and we share a little bit of our own insights in each of us bringing a story of the week. That's at twit tv slash tnw. Subscribe right now.