Security Now Episode 879 Transcript
Please be advised this transcript is AI-generated and may not be word for word. Time codes refer to the approximate times in the ad-supported version of the show.
Leo Laporte (00:00:00):
It's time for security. Now, Steve Gibson is here. We're gonna talk about N they have finally settled on some algorithms. The first four of their post quantum crypto algorithms. Steve will talk about 'em including one called crystals, di lithium, and Apple's extreme lockdown mode. Will Steve start using it? Plus why you may not wanna own a Honda automobile? Woo. It's all coming up next on security now, podcasts you love from people you trust. This is TWI TWI. This is security. Now with Steve Gibson episode 879 recorded Tuesday, July 12th, 2022. The rolling poem, this episode of security now is brought to you by ExpressVPN. Make sure your online activity and data is protected with the best VPN money can buy. Visit expressvPN.com/securitynow right now, and get three extra months free through our special link. And buy Tanium, Tanium, unites operations and security teams with a single platform that identifies where all your it data is patches.
Leo Laporte / Steve Gibson (00:01:19):
Every device you own in seconds and implements critical security controls all from a single pain of class. Are you ready to protect your organization from cyber threats? Learn more at tanium.com/twit. And by Thinks Canary. Detect attackers on your network while avoiding irritating, false alarms. Get the alerts that matter 10% off and a 60 day money back guarantee. Go to canary.tools/twit and enter the code TWI in the, how did you hear about us box at it's time for security? Now, here he is ladies and gentlemen, the star of our show. Bob Barker. No, no, that's wrong. Show Steve Gibson. Hello, Steve. I got my lighting proper this week. Oh yeah. Yesterday because you had the skylight open. I have like 1, 2, 3, 4, 5, 6, 7, 8, 9. I, I have many high watage LEDs that they, they, they pointed the ceiling, which is white. Oh, I get this really nice diffuse, but it, it like lit the room so much that my face was dark in, like in the camera.
Leo Laporte / Steve Gibson (00:02:27):
Right. So I thought and look at this. It's just amazing. It looks perfect now. So yeah. Well, good lighting makes a big difference, even with a bad camera. Makes a difference, right? That's right. Well, of course we all have that Logitech HD 7 27, 22 or whatever it is. Yep. So we are at security now episode 879 for the 12th of July. And I was a little ambivalent about the title, the rolling pwn. It's funny. It's funny that, yeah, that's the official name of the hack slash attack, but I wanted to do, I was toying with rolling your phone. And I thought, well, no. Okay. Or the rolling pin, but phone is what it's supposed to be. So anyway, I just left it alone this week, but first we're gonna look at a recently made and corrected mistake in the super important open SSL crypto library. What you missed last week or no week before last I forgot to mention when I was on with Jason, somebody, it was really pretty funny.
Leo Laporte / Steve Gibson (00:03:33):
Somebody took the open SSL command line and ran, remember the O open SSL is like the Swiss army knife times a thousand, took the open SSL command line and said, what if it was a gooey? And so our picture of the week was that, and it took up four pages of, of our show notes. Wow. And that was for one tab of one subset of the open SSL commands. Those were the options for, I think it was like making a cert and anyway, so it was just a, it was, that's a gooey for you. Yeah, it was a fun picture of the week, but yeah. Anyway, we're gonna talk about a, a problem that was found and corrected in open SSL. The N I S T of many of our listeners tweeted me to make sure I knew about this and wanted to hear about it has settled upon the first four of the total of eight post quantum crypto algorithms, which will become the next standard much as you know, rein do was the was, was de decided as the AEs standard.
Leo Laporte / Steve Gibson (00:04:42):
And we, and like, like the SHA 2 56 hashes, I mean, we, we need standards otherwise, you know, it's bad enough that our USB plugs won't go in the right way. Fortunately, they're all the proper shape. And, you know, at least we have that, you know, some are not triangular and some are not hexagon also anyway also Yubico stepped up to help Ukraine in a little blurb that passed by and I thought, oh, I just gotta, you know, give them a shout out. And a thank you. Good. apple of course has added the extreme lockdown mode that we'll talk about or it's forthcoming Microsoft unbelievably. And the, the whole security industry is just gone in meltdown over their announcement that they're Reen, enabling offices, VBA, macros, which are received over the internet after telling us in February to everyone's great relief and many size that they were gonna finally disabled them.
Leo Laporte / Steve Gibson (00:05:44):
By default. Now they're saying, oh, you're out a date. They've decided not to enable them. Oh, you're kidding. No, <laugh> this just in wow. Yeah. Mac. So they put out a press release yesterday, cuz there was a lot of upset over this. And macros from the internet will be blocked by default in office, according to Microsoft as of still B yesterday by default still. Okay. Yes. And I think, yeah, it it's, there's some nuance into the whole thing, but well we'll have, we'll have some fun at their expense anyway, because you know, they're, <laugh>, they're Microsoft. I will show the flow chart that decides whether macros are to run. You've showed it before <laugh> oh, you mean there's still a way for it to, for, to happen? Oh yeah. Oh boy. The FBI has created a successful encrypted messaging app, which participated in a major sting operation that we're gonna talk about.
Leo Laporte / Steve Gibson (00:06:46):
We're also gonna close the loop of some of our listeners. Then we're gonna examine an even more egregious case of remote automotive, wireless unlocking and engine starting, thus the rolling phone because ah, cars roll, get it after they've been PED and we have a really clever, wonderful picture of the week. So I think, or it's a little bit of a logic lesson. It's exciting. Yes. Good, good show. As always coming up, I look forward to Tuesday all week long to hear the LA in fact, and I'm sure I'm not alone in this. I see articles. And I go, I can't wait to hear what Steve has to say about that. Can't wait to you do what says you without you? I wouldn't know what to think about any of this stuff. Our show today brought to you by I'm happy to say those good folks, that ExpressVPN I don't have to explain what a VPN is to your audience.
Leo Laporte / Steve Gibson (00:07:43):
Steve. They are of course experts in this. And I don't probably don't have to remind you that there are, this has been a real point of contention of late data brokers out there, middlemen who buy all the information about you from Google and Facebook and everybody, and then sell 'em off to anybody who wants. And this is a big deal because these data brokers, because they're getting so information from so many sources can really stitch together a very detailed profile of you. Again, I think, you know, this, our audience knows this, but let's, let's kind of remind them, you know, it's not just your browsing history or your online searches or even your location data, it's everything you do online. They sell it off to a company for advertising, you know? Okay. Maybe that's okay, but of late, they've also been selling it to the government, the department of Homeland security, the IRS and it has really become a significant cause for concern in this you know, post row world.
Leo Laporte / Steve Gibson (00:08:53):
So maybe you need to protect your privacy from these data brokers. You don't want the tax man showing up the, on the door because you searched for something on your phone. What is the Dutch sandwich after all mask your digital footprints use the VPN. I recommend the only one I use express VP N one of the easiest ways for brokers to aggregate gate data and tie it back to you is through your IP address, right? Which also by the way, reveals something about your location using ExpressVPN. Your IP address is hidden ExpressVPN only displays its IP address, right? You are coming into the Google search or whatever you're doing with your, not your IP address, but, but ExpressVPNs. And by the way, so important ExpressVPN invests in their services. So one of the things a lot of VPNs fail with is they don't rotate their IP addresses enough.
Leo Laporte / Steve Gibson (00:09:50):
It's one of the reasons you can't use a lot of VPNs for, for, you know watching eye player in the BBC or Netflix in another country. You can't get around these geographic restrictions cuz they say, oh yeah, it's a VPN IP address. That's really the only way they know if you're on a VPN. So you wanna VPN provider ExpressVPN that, that rotates, those addresses, that invests in bandwidth that makes it possible to use the VPN without feeling like you're hobbling yourself. And of course, and this is a given ExpressVPN encrypts, a hundred percent of your network traffic. So when you're on a public wifi or anywhere when we're on the cruise ship, you better believe be using ExpressVPN. You're visible to everybody else on that cruise ship. You can put it on everything, your phone, your laptop, your your smart TV.
Leo Laporte / Steve Gibson (00:10:36):
You can even put it on many routers, which means the whole house can be protected by ExpressVPN. And it's so simple to turn on you. It, you know, you press the big button on the ExpressVPN app and it will automatically go to the fastest nearest server. But if you want to be in the UK to watch, you know, Dr who on Netflix, you could say, no, no, no. I wanna be in the UK. They'll, you'll go down to the London docs. You'll be there. And you know, BBC I player works with ExpressVPN. It's kind of an amazing thing. Netflix works with ExpressVPN. I should also mention ExpressVPN goes the extra mile and this is something Steve's always talking about to prevent logging. They do not log, of course it says that in the privacy statement, but you'll be glad to know if you look at the technical details, they go to the extra mile, they have this open source trusted server that they use that is sandbox runs in Ram.
Leo Laporte / Steve Gibson (00:11:22):
It it gets created when you go there. As soon as you close the VPN connection, it's only for you. It goes away, no traces left. They also use a, a custom Debbie and distro and, and it's refreshed and rebooted the whole hard drive wiped on a daily basis. I mean, they just, they do all the things you would want somebody to do. Who's trying to protect your privacy ExpressVPN. So protect your online activity. TYY data brokers watch doctor who do all the things you like best ExpressVPN.com/security. Now you get three months free with a one year plan, but you've gotta go to ExpressVPN.com/security. Now E X P R EESS vpn.com/security. Now find out more, read up all about it. And there's also, I should put a link in the show notes, a very good bleeping computer writeup on ExpressVPN and the technologies they use to protect you.
Leo Laporte / Steve Gibson (00:12:18):
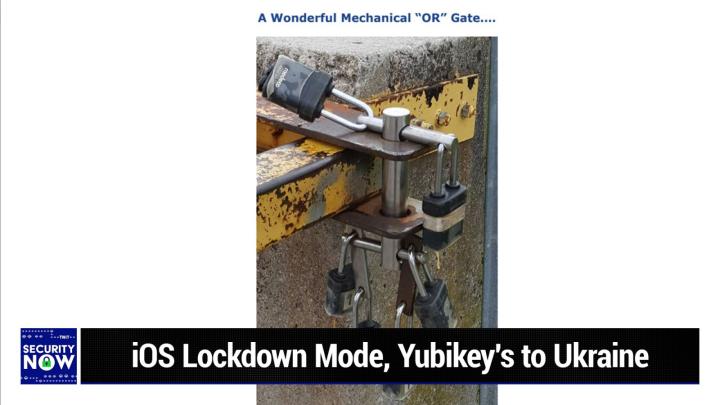
And it's, it's really impressive that they really go the extra mile. Thank you. Expressvpn for supporting Steve picture the week times Steve Reno. So this is a visual feast. Unfortunately it's, it would be difficult for me to explain it in words. Well, that's why there's a picture that <laugh> for the, that's very good point for those who, who do have the the show notes in front of them. There's a, the, as I described at the beginning and I gave it a title, a wonderful mechanical or gate <laugh> if you, if you, oh, Leo, it's just so good. If, if you imagine that you, that six different people had six different keys to six different padlocks. Now, if you wanted to, if you wanted to allow any one of them to unlock, for example, a gate that was secured with a chain, well, you could enter lace you, you could interlock six padlocks, you know, the HEPs of six padlocks through each other, right.
Leo Laporte / Steve Gibson (00:13:26):
To sort of create one long pad Locky thing, such that if any, one of the keys could unlock its one padlock. And because it was a chain of padlocks that would unlock the whole chain. The problem we have here though, is that this thing that's being secured, there's a, there's a big steel arm coming in from the left it's like gaps or something. Yeah. Yeah. And, and it wants to come, it wants to slide outwards. So there, there, isn't really a way you could do that with inter with, with interlinking, HEPs of padlocks. So some mechanical engineer, I mean, this is just so cool to I, the more I looked at it for a while, the better I, this is brilliant. So, and unlocking any one of these padlocks opens the gate. Yes. It, it is an, it is that, well, I guess it would be an, and wouldn't it because you, they all have to be closed for it to be work for it to work any one of them being opened, or it just depends whether the true value is unlocked or locked, right?
Leo Laporte / Steve Gibson (00:14:30):
Yes, exactly. <Laugh> exactly. So it's a war if it's unlocked. It's an and if it's locked right. And, but what's so cool. Is that, I mean, again, I, there's no way to describe it except to say that it's this wonderful mechanism where any one of these locks, like one of 1, 1, 1 at the bottom, you would unlock one at the bottom 18 or 15. Yes, no, exactly. That would allow the, the, the, the, the shim to be removed from a pin, which then allows the pin to slide out which the little pin at the bottom, which then allows the big pin at that the big vertical pin to be lifted out of the way of the lever that wants to come out. So it's, this multi-stage lock, right. Lever is really good. I'm not sure I understand how 15 S so if I take 15 or 18 out, then that means, oh, I can, I can slide this bigger bar out and then slide this little pin out, right?
Leo Laporte / Steve Gibson (00:15:34):
Yeah, yeah. You kind of have to be there to, and certainly describe. And then, and then the big one comes, as I said, there's really no way to describe it, except to, you know, it, it's analogous to a chain of, of six locks that are, you know, interlinked, but in a way that works with this particular mechanism anyway, it's just wonderful. Wonderful, wonderful. So whoever that was a listener of ours, who said, what do you think about this for a picture of the week? It's like, wow. Right on. Wow. Wow. Wow. That is, that is dead on the money. That's our kind of, that's our kind of picture. Okay. So open SSL version 3.0 0.4, introduced a serious vulnerability, which version 3.0 0.5 just repaired. It is a potential remote code execution flaw, which was recently discovered in an update that is this 3 0 4 to the V3 branch of open SSL.
Leo Laporte / Steve Gibson (00:16:35):
The issue was found, as I said, in 3.0 0.4, the good news is it was just released late last month on June 21st. It impacts X 64. So 64 bit Intel architecture systems having the AVX five, 12 instructions set extension. The good news is open SSL version 1.1 0.1, as well as the, the two forks boring SSL and Libre SSL they're not affected. So only the three branch, the trouble stems from a remote memory, corruption, vulnerability. These, this AVX are the advanced vector extensions, which add instructions to the X 86 instructions that architecture from arch, from processors, both from Intel and AMD. There was some interesting back and forth about this in the GitHub issue thread where I think that the open SSL foundations guy Thomas Marra, he, he said, I do not think this is a security vulnerability.
Leo Laporte / Steve Gibson (00:17:52):
Of course, you know, he didn't want it to be, he said it is just a serious bug making the version 3.0 0.4 release unusable on AVX five, 12 capable machines. Okay. So I guess he's saying that it will crash, but so like the certificates, it involved RSA certificates, so they won't work. But so that's a problem. A security researcher Guido Rinkin. He said that said it can be triggered trivially by an attacker, another person participating in the thread, Alex gainer wrote. I'm not sure I understand how it's not a security vulnerability. It's a heat buffer overflow. That's triggerable by things like RSA signatures, which can easily happen in remote contexts. Like he says a TLS handshake and the post-grad PhD student who originally discovered and reported the bug chimed into the thread stating he said that quote. He says, although I think we shouldn't, as in, should not mark a bug as security vulnerability in quotes, unless we have some evidence showing it can, or at least may be exploited.
Leo Laporte / Steve Gibson (00:19:17):
He says it's necessary to release version 3.0 0.5 as soon as possible. Given the severity of the issue, which is what did in fact soon happen. The issue has been assigned CVE 20 22, 22 74 described in that CVE as a case of a heap memory corruption within RSA private key operations, the advisory notes, the quote SSL slash TLS servers or other servers using 20, 48 bit RSA private keys running on machines, supporting AVX five 12. I FMA instructions of the X 86, 64 architecture are affected by the issue and calling it a serious bug in the RSA implementation, but still apparently not wishing to call it a vulnerability. The maintainers of open SSL said that the flaw could lead to memory corruption during computation. That could be weaponized sounds like a vulnerability to me by an attacker to trigger remote code execution on the machine, performing the computation.
Leo Laporte / Steve Gibson (00:20:31):
So anyway, it, as I said, <laugh> smacks of a security vulnerability. Well, anyway the flaw has been patched and all users of open SSL V three should move to 3.0 0.5. Especially if you had diligently moved the 3.0 0.4, which is the buggy release. On the other hand, the window was a couple weeks. So the chances are nobody even had a chance to get the buggy one before you got the good one. So anyway, just FYI. Okay. Last Tuesday, the us N right, our national Institute of standards and technology announced that the results of a six year, these things do take a while. And I'm glad this is not something you wanna rush, because we're gonna be living with this for a long time. The six year competition among a set of post quantum algorithms had resulted in the selection of four initial algorithms.
Leo Laporte / Steve Gibson (00:21:38):
That is because there are gonna be a total of eight. So the first half have now been chosen after editing out the various self-congratulatory statements from various bureaucrats who have no clue what this is all about and who certainly didn't even write what they are quoted as saying in N's official announcement. I read through this as like, oh, come on. <Laugh> you have no idea what you're talking about anyway. <Laugh> what are you talking about? I've always been a fan of elliptic, curb cryptography, and <laugh> that's right. You know, I use it to clean my sheets every, every week. So here's what the the, the people who actually wrote something about this and were involved in the choosing had to say, they said the us department of Commerce's national Institute of standards and technology N has chosen the first group of encryption tools that are designed to withstand the assault of a future quantum computer, which could potentially crack the security used to protect privacy in the digital systems.
Leo Laporte / Steve Gibson (00:22:48):
We rely on every day, as in today, such as online banking and email software, the four selected encryption algorithms will become part of N's post quantum cryptographic standard expected to be finalized in about two years. The announcement follows a six year effort managed by NIST, but like not in any way, poisoned by them. This has all been done open on GitHub in full public view, managed by N which in 2016, called upon the world's cryptographers to devise, and then vet encryption methods that could resist an attack from a future quantum computer. That is, you know, one with more than four qubits that is more powerful than the comparatively limited machines available today. Today's selection constitutes the beginning of the finale of the agency's post quantum cryptography standardization project. And this is clearly a good thing. You know, they, I don't remember Leah, whether they were able to do the factorization of what was it, 33 or something.
Leo Laporte / Steve Gibson (00:24:07):
It's some ridiculous number. Yeah. It's like, okay, how hard is, is that? Huh? We don't have to, we don't have to worry about it right now. I have to say we are making progress. So I, this was a story a couple of days ago that scientists in Germany have showed spooky action at a distance of 20 miles, two atoms. So that's when the that's when, you know, called quantum entanglement. Yeah. Quantum entanglement and the, and the two atoms somehow are communicating instantaneously across 20 miles. Light speed. Not at light speed, much faster instantaneously. Yeah. Yeah. Which tells, tells you, you know, definitely a simulation <laugh> okay. Or, or there's some dimension we don't know about in which those two atoms are right next to each other, or are the same thing or the same thing, or idea of space could be just an illusion right.
Leo Laporte / Steve Gibson (00:24:56):
There isn't actually any, it's just it's mind boggling that they're, that they're doing it. It does. I mean, it does. It hurts. It hurts. Yes. It hurts. Yes. okay. Four additional algorithms are under consideration, still for inclusion in the standard and missed plans to announce the finalists from that round at a future date, NIST is announcing its choices. They wrote in two stages because of the need for a robust variety of defense tools, as cryptographers have recognized from the beginning of N's effort, there are different systems and tasks that use encryption and a useful standard would offer solutions designed for different situations. And that's yes. You know, how many times have we, we talk about the toolbox that we have today and how cool it is that you could just put these things, these little components together in all different ways. So use varied approaches for encryption and offer more than one incre one algorithm for each use case in the event.
Leo Laporte / Steve Gibson (00:26:02):
One proves vulnerable, and that's what they've done here. You know, this is like, we're, it feels like we're beginning to understand collectively, you know, as a planet, how to do these sorts of things correctly. So explaining this for the masses, N added encryption uses math to protect sensitive electronic information, including the secure websites we serve and the emails we send widely used public key encryption systems, which rely on math problems that even the fastest conventional computers find intractable ensure these websites and messages are inaccessible to unwelcome third parties, however, a sufficiently capable quantum computer, which would be based on different technology than the conventional computers we have today could solve these math problems quickly to defeat today's encryption systems to counter this threat. The four quantum resistant algorithms rely on math problems that both conventional and quantum computers should have difficulty solving their thereby defending privacy both now and down the road.
Leo Laporte / Steve Gibson (00:27:25):
Okay. I got a tough question for you. Do we now trust N cause remember they intentionally recommended a weak algorithm at the behest of the national security agencies. Yeah. And I would say those were days gone by. Yeah. I, I there's no cryptographer who doesn't know that this, this, you know, this random bit generator that the RSA, that RSA corporation was sort of defaulting to had some, had some sketchy background, you know, there, there was, there was no reason for the NSA not to describe where the magic numbers came from, that that, that digital random bit generator used, but, and, and that would've made everyone feel good. If somebody had said, this is how we chose these numbers, then everyone would've gone. Okay. That makes sense. Instead, it was thou shall use these numbers. Yeah. And it was like that's not the way we do things here.
Leo Laporte / Steve Gibson (00:28:34):
So, and you know, and the point is it wasn't the way it sort of was the way we did things then, because nobody was that focused on those things. Now we really are. So I don't think that could ever happen again. I mean, and so, so this is a, this was done very much, like the way Rhind was chosen, where a number of like really good candidates were examined and, and sample implementations code was created and things like, how fast can we make this work on a 64 bit X, you know, 64 architecture? And can we, can we design algorithms, which will not be subject to, to side channel attacks? I mean, just think about everything we've learned in the last 20 years, all of that is now rolled into this and, you know, lots of debates. That's why it took six years you know, to, to decide this.
Leo Laporte / Steve Gibson (00:29:33):
So in this case, these first four of the eight total algorithms, the first four are designed for two main tasks, for which, as we know, encryption of, or crypto is typically used general encryption, which is used to protect information exchanged across a public network. And digital signatures used for identity authentication. All four of the algorithms were created by academic experts, collaborating openly from multiple countries and institutions to provide for general encryption N and it's, it's not N as much as it's the, the collective. And that's just, it N is sort of just sort of saying, yeah, you know, we're gonna do the press release, but it was this, it wasn't N that chose. It is, I guess, by is the point. It was everybody coming to a final agreement that okay, to do encryption, we're gonna use the crystals KR algorithm, which is what was chosen for encryption.
Leo Laporte / Steve Gibson (00:30:40):
And and it was chosen because it uses comparatively small encryption keys, which two parties will be able to exchange easily as well as very good speed of operation on the digital signatures side, N and the collective selected three algorithms. I like this first one I do too. Leo <laugh>, it's the dial lithium crystals algorithm. Yes, we've got, and then we also have Falcon and we have FIS it's actually FIS plus because there was some tweaking that was done later. So it's S P H I N C S plus sign, which we're supposed to read as FIS plus reviewers noted the high efficiency of the first two and N recommends crystals, di lithium to be used as the primary algorithm with Falcon, for applications that need smaller signatures than di lithium is able to provide the third. And this is again, why the thinking was so good on this FIS plus is somewhat larger and slower than the other two, but it's valuable to have as a backup for the reason that it is based on entirely different math than all of the other three N selections.
Leo Laporte / Steve Gibson (00:32:05):
The other ones are based on Latice math and SX isn't. So, again, we've learned that where crypto is concerned, there's nothing wrong with using a belt and some suspenders. The, as I said, the first three of the four selected algorithms are based on a family of math problems known as structured lats, which is why the word crystal appears as part of the names of the first two, while Spinx plus uses hash functions. Now the next four algorithms to be chosen, which are still under consideration, are designed for general encryption and do not use structured Latice or hash functions in their approaches. So again, we're gonna do, like, we're looking at a variety of different solutions to like in advance. And, and once we deploy these, all of them will be selectable in the various algorithms, so that if something is found to be wrong, it'll be like, whoops, and it'll be easy to just, you know, switch over or remember how the early versions of true cryp allowed you to use like multiple different algorithms, like at once under the theory that, well, if one of them was broken, then you know, the other ones would, would still be good.
Leo Laporte / Steve Gibson (00:33:27):
So anyway, we, we we'd sort of have a little bit of that too. So mistro, while the standard is in development, N encourages security experts to explore the new algorithms, all, all the sources public, by the way, and, and, and post it online. And that's why we shouldn't worry about NT being involved in this, obviously. Yeah, yeah. Yeah. I mean, they really weren't. They were just, again, based on the Leo, that text that I excluded from the announcement, you would know that whoever it was who wrote that Senator the fog horn leg horn believes that crystal lettuces is, are the finest way to protect yourself. Yeah. That's exactly it. Yeah, yeah, yeah. Boy, so they said, while the standard is in development, just encourages security experts to explore the new algorithms, to consider how their applications will use them, but not bake them into their systems quite yet, as the algorithms could change slightly before the standard is finalized.
Leo Laporte / Steve Gibson (00:34:25):
Can we use these if they're not baked? I mean, can we use them now or yeah, yeah, yeah, yeah. Oh, I mean, they've been pound, they've had the crap pounded out of 'em already. Yeah. They're pretty well based. Yeah. I think it's, it's, it's likely that they're pretty much. Yeah. But they're just, you know, again, they're hedging their bets. They don't wanna be like, have fingers pointed at them saying, Hey, you said these were funnel. Right. And we burned it into our firmware. Yes. And sent it up into outer space. So it's like, no. Okay. You don't, you don't don't do that quite yet. Don't do that. So, but what tools, like my PG welcome to use them right now use 'em all you want Elon PGP or, I mean, what kind of tools TLS, I guess. Yes. Would it be, yeah.
Leo Laporte / Steve Gibson (00:35:09):
Yeah. basically, you know, our crypto uses signatures all over the place and uses encryption all over the place. Yeah. So I PGP for that, which of course is an ancient and kind of ulous bundle of algorithms. None of which are these. Yeah. We could hope that PGP does not incorporate <laugh> these well, so that once quantum computing comes along, eh, sorry, PGP. Yeah. It's your time has been SSH though. Would probably implement it. I would imagine. Oh, oh, I there, well, yeah. You mean yeah, TLS definitely would. Yeah. and, and, and it'll be used for hashing and I mean like a next generation set of functions, the idea being that these assuming that big quantum machines actually do happen. And again, it's like, these are fast enough that there's no reason not to switch over to them. And that's the point, right?
Leo Laporte / Steve Gibson (00:36:09):
At some point, because remember the other danger that we've talked about is that things that are encrypted today cannot be decrypted today, but they could be decrypted tomorrow. So, so this is why the NSA has that massive facility in Nevada, where, which is why Vegas' lights are dimer now than they used to be. Is that the NSA is just storing everything. They're like, well, we can't encrypt it yet, but we'd think that once quantum comes along, we'll be able to retroactively decrypt all this crap that we've been storing. So let's just keep it because storage doesn't cost anything. So the point is we wanna switch over to post quantum crypto, as soon as we know that we can trust it, assuming that it's not gonna be a lot slower. And these algorithms are not slower than the ones we have, they're just bigger and different.
Leo Laporte / Steve Gibson (00:37:06):
We wanna switch over so that we, so that we start giving the NSA stuff that, ah, sorry about that. But this is the di lithium crystal, quantum. I love it, crypto and near your Sol mm-hmm <affirmative> so, yeah. So and by the way, you can't crack these di lithium crystals <laugh>. So I, I obviously have no problem with the idea that adopting advanced post quantum cryptography under the name di lithium crystals will is like what we ended up with. Mm-Hmm <affirmative> mm-hmm <affirmative> but I have to say Leo, that in scanning through all of the candidate entries, from which these four winners were selected, I did breathe a sigh of relief. When I saw that the quantum algorithm named photo <laugh> had not won. I, I would have a hard time. Yeah. Choosing photo, you know, as my post quantum solution, I refuse to use an algorithm with Harry toes. I'm sorry. It's just not gonna happen. Thank you. On that note, I'm gonna take a sip of water <laugh> and then we're gonna talk about Yubico Adrian in the chat room says, you mean da Lithium's a real thing. I thought it was just some fictional star. Trek's real now, baby. It is now real. Now. Congratulations. You have entered the di lithium zone. Our show today brought to you by let me find out who it's brought to you by. That's what I need to do. Oh, I know what I did wrong.
Leo Laporte / Steve Gibson (00:38:41):
I should never use Bing for a browser. Oh, it, Lori keeps telling, saying me, how can I get rid of this thing? It keeps coming back. I hate, I hate it. I hate it. Hate Bing. Ah, are so today brought to you by Tanium. Now, you know why we need Tanium, right? The industry's approach to cyber security has, you know, kind of a fundamental flaw. It management and security point tools are only offer small piece of the solution that you need to protect your environment. And many of them say, oh, we can stop all breaches. They, when they, they absolutely can't. They absolutely can't. You need to be making decisions on up to date data, not stale data. You, you, you, you can't, you can't defend your critical assets from cyber attacks, but tools that just don't talk to each other. That's just no way for it teams.
Leo Laporte / Steve Gibson (00:39:33):
These days to navigate the modern attack surface it's time for a better approach, a different approach. And Tanium is one of those young disruptors that is changing the way we think about security. They say it's time for a convergence of tools, endpoints, and it ops and security. They've got solutions for every sector, government, entities, education, financial services, retail, healthcare. You could trust their solutions for every workflow that relies on end point data and all in one, you get asset discovery and inventory. So, you know, instantly exactly what assets, what it assets you have. They've got risk and compliance management, which means you could find and fix vulnerability at scale. And instantly, I mean really literally seconds. They've got very powerful threat hunting, which lets you hunt for a sophisticated adversaries. In real time. Client management, automates operations from discovery to management, sensitive data monitoring cuz after all the data is what's important, right?
Leo Laporte / Steve Gibson (00:40:36):
You can index and monitor sensitive data globally in seconds. And know when it's been changed when it's been modified, when it's not all their attaining protects organizations where other endpoint management security providers have failed. One platform, tan Tanium identifies where all your data is across your entire it. Estate can patch every device you own in seconds can implement critical security controls all from a single pane of glass. Just ask team users like Kevin Bush, vice president of it at ring power Corp. He says, quote, Tanium brings visibility to one screen for our whole team. If you don't have that kind of visibility, you're not gonna be able to sleep at night. With realtime data comes realtime impact. If you're ready to unite operations and security teams with a single source of truth confidently protects your organization from cyber threats, its time you met Tanium T a N I U M to learn more, visit tanium.com/twi tanium.com/twi, cuz there's no way to be secure with silos, right?
Leo Laporte / Steve Gibson (00:41:40):
Break those silos down between operations and security with Tanium tanium.com/twit. Please use that URL. So they know you heard it here. And we thank Tanium so much for supporting security. Now back to you, Steve. So to help Ukraine hold off Russia's cyber attacks, Yubico donated 30,000 Fido UBI keys. Bravo. I know, I thought that was so neat. I just, I just, I just happened to see it in passing so far more than half of those 30,000 around 16,000 UBI keys have been deployed to Ukrainian government executives, workers and employees of private companies in Ukraine's critical sectors. The initiative is been coordinated by a company named Heidi's H I D E E Z, which I, you know, I guess ID as an identity. Heidi's they're a Ukrainian security firm specializing in identity services and Fido consultancy. So they know their way around Fido earlier this spring, Heidi secured a donation of 30,000 UBI keys from Yubico and the way to go St.
Leo Laporte / Steve Gibson (00:43:01):
Since then Heidi's staff has been working with Ukrainian government agencies like the ministry of digital transformation, the national security and defense council and the, the state service of special communications and information protection. That's the SSS C I P <laugh> of Ukraine to ensure the devices can be. And it's one thing to have UBI keys, right? But you gotta know what to do with them. So they're ensuring that devices can be imported into the country. That government infrastructure is prepared for the UBI keys rollout and that reci and that the recipients receive the necessary training to know how to use 'em. So the idea is that once government and critical sector workers have a security key as an extra layer of protection, their accounts would finally be safe from what it amounts to an onslaught of nonstop spearing attacks, which have been constantly hitting their inboxes every day.
Leo Laporte / Steve Gibson (00:44:03):
URI Ackerman VP of war efforts at Heidi Heidi's told the the publication risky business. He said we got UBI key certified. So they're allowed to be deployed into Ukraine instances. He said, we have quite a few ins of quite a few ministries that have moved a lot of their stuff to G suite and Azure with them. It's quite easy. We just give them a key. We made instructions in Ukrainian video instructions and so on. So it's really fast. We had a department that pretty much moved to using Fido like 500 people in less than a week because they just needed to understand their policies, read our documentation and that's it. They just give the keys and roll them and voila. So meanwhile efforts are underway to roll out the keys to individuals in other departments. You know, they still have what 17,000 of them available or 14,000 rather, including those without the proper server side infrastructure in these cases, Ackerman says Heidis has been providing the government with the company's solutions at minimal costs.
Leo Laporte / Steve Gibson (00:45:18):
Anyway, as I said, I just happened upon this nice bit of news and wanted to acknowledge what Yubico had done to help U Ukraine and their war effort is Fido related to Pasky Fido two. Yes. Fido was the original and that was the one which didn't get off the ground because it absolutely is tied to a hardware token, whereas Fido two we are allowed to use you know, devices that odd that have some sort of biometrics in order to the same concept. Really? Yes. Yeah. Yes. Same concept concept. So Apple's new. Oh, I, I should, I should mention though, also that Fido two uses web off N also as its, as its protocol to the web server, whereas Fido doesn't is not a web off end user. Oh, okay. So you have to have specific specific support for, for Fido on, on the server side.
Leo Laporte / Steve Gibson (00:46:20):
Right. Which is why Heidi's is having to, to use, bring in some of its own technology where that's not available. Got it. Yeah. So Apple's new extreme lockdown mode and extreme is their word, which I thought was kind of fun in a blog post last Wednesday, apple took the wraps off of lockdown mode, which will be rolled out later this year. First seen in Mac OS Ventura iOS 16 and iPad OS 16. This is an optional mode which will in again, in their words, severely restrict some features. I mean, it's, they've gone to a great degree here. I, I guess on one hand it's selling the idea that it is so restrictive, but they're also like making it clear that yeah, we're not sure that this is for everybody. So, you know, if you were to turn this on, be prepared for a bunch of stuff, not to work.
Leo Laporte / Steve Gibson (00:47:19):
The aim is to protect specifically highly targeted individuals, such as human rights workers and researchers by reducing their devices available attack surface. So, you know, and, and they provided in their announcement, a screenshot where like, this is the screen where you would go to turn this on. And it says lockdown mode is an extreme, optional protection that should only be used. If you believe you may be personally targeted by a highly sophisticated cyber attack. Most people are never targeted by attacks of this nature. Then they said the second paragraph, when iPhone is in lockdown mode, it will not function as it typically does apps, websites and features will be strictly limited for security and some experiences will be completely unavailable. And then they've got a button to learn more or <laugh> this big scary one at the bottom turn on lockdown mode. So the way apple put this in their announcement and they, they used a term I hadn't seen before I thought was interesting.
Leo Laporte / Steve Gibson (00:48:38):
They said apple expands industry, leading commitment to protect users from highly targeted mercenary spyware. Mm <laugh>. They said apple is previewing a groundbreaking security capability that offers specialized additional protection to users who may be at risk of highly targeted cyber attacks from private companies, developing state sponsored mercenary spyware. Wow. Yeah. Apple. They said apple today detailed to initiatives to help protect users who may be personally targeted by some of the most sophisticated digital threats, such as those from private companies, developing state sponsored mercenary spyware. Okay. We get the message. Apple lockdown mode, the first major capability of its kind coming this fall with iOS 16, iPad OS 16. And Macko S Ventura is an extreme optional protection for the very small number of users who face grave <laugh> targeted threats to their digital security. Apple also shared details of about, about the 10 million cybersecurity grant.
Leo Laporte / Steve Gibson (00:50:04):
It announced last November to support civil society organizations that conduct mercenary, spyware, threat research and advocacy. In other words, you know, researchers who were like gonna dig into what this is all about. They said Apple's head of security engineering and architecture was quoted. Apple makes the most secure yeah. Blah, blah, blah, mobile devices on the market. You can always tell when you're reading from an apple press release <laugh> yeah. Blah, blah. Right. Okay. Lockdown mode, he said is a groundbreaking capability that reflects our unwavering commitment to protect the users from even the rarest, most sophisticated attacks Peren which we're unable to block. Oh, okay. He didn't really say that while the vast majority of users will never be the victims of such highly targeted cyber attacks. We will work tirelessly to protect the small number of users who are, that includes continuing to design defenses specifically for these users, as well as supporting researchers and organizations around the world, doing critically important work in exposing mercenary companies that create these digital attacks, lockdown mode.
Leo Laporte / Steve Gibson (00:51:24):
He said offers an extreme optional level of security for the very few users. You know, and they're like, they really don't want you to turn this on, but they want you to feel very special if you do, because of who they are or what they do may be personally targeted by some of the most sophisticated digital threats, cuz after all, otherwise it wouldn't get through the regular iOS security such as those from oh, and we're we're naming names, the NSO group and other private companies developing state sponsored mercenary spyware, turning on lockdown mode in iOS 16 and iPad OS 16 and Mac OS Ventura. You might as well just turn off your device. No, it doesn't say that. Further hardens device defenses and strictly limits certain functionalities sharply reducing. And I actually believe in this a lot, the attack surface that potentially could be exploited by highly targeted mercenary ware.
Leo Laporte / Steve Gibson (00:52:29):
Okay. So at launch lockdown mode includes the following protections. We have five messages, most message attachment types. Other than images are blocked. Some features like link previews are disabled because yes, those could be abused. Web browsing, certain complex web technologies, Bravo, apple, like just in time JavaScript compilation. Remember we saw Microsoft experimenting with disabling that an edge because it just seems to be where all the problems are just in time. Javascript compilation are disabled unless the user excludes a trusted site from lockdown mode, third apple services, incoming invitations and service requests, including FaceTime calls are blocked. If the user has not previously sent the initiator a call or a request, wired connections with a computer or accessory or blocked when iPhone is locked. And maybe you guys expl talked about this over on Mac break, I'll ask you about that in a second later. Sure.
Leo Laporte / Steve Gibson (00:53:46):
And finally configuration profiles cannot be installed and the device cannot enroll into mobile device management while lockdown mode is turned on. So to my eye, these all sound like very useful and sane restrictions. You bet they would not hugely impact even most users. I think while they would very clearly and significantly restrict the devices attack surface. So I say, Bravo, apple, nice going. I'm sure that they've closely looked at the history of the way their devices have been compromised and then took steps to address future threats in a way that will keep their devices useful and usable while being far less easily compromised. So again, Bravo, so Leo, that fourth thing, wired connections with a computer or accessory are blocked when iPhone is locked. This is how I interpreted it. And I, and the panel seem to agree. That's so that you can charge, but not have a data connection with a USB port.
Leo Laporte / Steve Gibson (00:54:57):
Right? So it's to prevent you from plugging your iPhone into okay. Some strange port, it actually allows you to do so. It's like you're a USB condom. I think so. Cause what happens normally with an iPhone, when you plug in a USB cable to a device, it says, you trust this device, you say yes. And now you can exchange data this, which is obviously risky. That's very, very smart. I think it it's a built in a built in condom. Yeah. For your, a built for your condom. That's how apple should sell it. I think yeah. A rubber for your phone, most of you will not need a built in condom. Well, didn't caught, but I had a question about the just in time stuff. Didn't we talk about that at one point that Google's research showed that just in time JavaScript was problematic.
Leo Laporte / Steve Gibson (00:55:47):
Yeah. It was Microsoft M doing this because now they have Bing and, and as we know, Bing is now is now based on the chromium engine. And so it was, it was their analysis that showed, I think it was 80%, eight, 0% of the, of the problems that they were seeing in JavaScript resulted from tiny flaws in the, in, in this like squeezing the last, every last bit of performance out of JavaScript. And what they were saying was, you know, maybe five years ago, 10 years ago, computers were still slow. I mean, remember back then we didn't wanna use encryption. Right. Because it slowed down things. Yeah. Yeah. It was too. It was too slow. Now it's like, bring on, we're gonna go quantum baby. We're gonna do di lithium encryption. So, you know, so anyway, so Microsoft said, Hey, just turn this off.
Leo Laporte / Steve Gibson (00:56:43):
And you're gonna be automatically protected from 80% of the problems that we're having. So apple is saying the same thing and it's not like turning off JavaScript. It's just turning off the JIT compiler or JIT playback. So you frankly maybe would run a little slower, probably not on a modern machine. And it eliminates a lot of those security flaws. So I think that's, yeah, I agree with you. This didn't seem too onerous. It, it, no, you know, Google has, has their, you know, superior security where you have to have two Titan keys and all of that. I tried that for a while and you lose so many, so much functionality from Google that wasn't, wasn't worth doing it, but I, I could see turning this on for a normal person. I'm gonna turn it on, see how it feels because like why not?
Leo Laporte / Steve Gibson (00:57:29):
And, and you know, I'll bet that would be, you know, they're gonna have some telemetry I'll bet it'll be some interesting metrics that they're gonna get back about how many people go. Yeah. You know, I don't need all, I forgot. I turned it on, you know? Yeah, yeah, exactly. Yeah. It's all the things that people do that are dangerous, like links and messages and the message rendering engines. I also use my security. Now knowledge are Mac Breakly about that because we talked about, you know, this is where you see a lot of flaws on windows as well as on on apple products with this interpreter that has to somehow render this, this content in in messages and it's often a security issue. Yep.
Leo Laporte / Steve Gibson (00:58:10):
Okay. So as you said, it's already the case that Mike, that Microsoft is not going to do what they said they were gonna do last week, which he really confuses the hell outta people. <Laugh> caused such a hubub. Although the Paul duckin, who was, who, who writes for sofas I, I loved what he said about this. And I'm, I'll, I'll share it just because it's a great blast from the past. So so, so, so that everyone understands this macro abuse that we've suffered for so long. And I, I remember when they announced it at the beginning of the year, Leo, you and I back in February were, were, were looking at the notice bars that used to be, and that would be where it was so easy for you to like, click on, allow macros.
Leo Laporte / Steve Gibson (00:59:13):
And so like, you know, edit, you you'd get some piece of email and it would say, oh, this is not gonna display properly. Unless you allow macros click here. It's like, who would not click that? Of course you would, because, you know, it's like telling you to click it. And so Microsoft was said, oh no, okay. We realize this has been causing lots of problems. We're gonna, or we're gonna turn this off. So what shocked everybody was when they said we're not gonna tell you why. And they actually refused to, to tell people why exactly they changed their mind, but they announced last week, they were gonna do that. Anyway. So, so, and, and, and sofas, Paul said, remember, 1999. Well, he's he said the Melissa virus called, oh yeah. And it's finding, it's finding life tough in 2022, he said, it's demanding a return to the freewheeling days of the last millennium.
Leo Laporte / Steve Gibson (01:00:10):
When office macro viruses didn't face the trials and tribulations they do today. He said in the 1990s, you could insert VBA. And he said, you know, visual basic for applications, macro code into documents at will email them to people and, or ask them to download them from a website somewhere. And then you could just totally take over their computer. In fact, it was even better or worse than that. If you created a macro subroutine with a name that mirrored, one of the common menu items such as file save or file print, then your code would magically and invisibly be invoked. Whenever the user activated that option were still, if you gave your macro a name like auto open, then it would run every time the document was opened. Yuck. I know <laugh>, it's just like, how did we survive Leo? Yeah. And he says, even if the user only wanted to look at it, and if you installed your macros into a central repository known as the global template, your macros would automatically apply all the time.
Leo Laporte / Steve Gibson (01:01:32):
Worst of all, perhaps an infected document would implant macros into the global template, thus infecting the computer and the same macros when they detected they were running from the global template. But the document where you just opened was uninfected could copy themselves back out again to that document. He, he said that led to regular perfect storms of fast spreading and long running macro virus outbreaks. Simply put, once you'd opened one infected document on your computer, every document you opened or created thereafter would, or at least could get infected as well until you had nothing but infected office files everywhere, everywhere. Nice. As you can imagine, he said at that point in the game, any file you sent or shared with a colleague customer pro prospector investor, supplier friend, enemy journalist, random member of the public would contain a fully functional copy of the virus, ready to do its best to infect them when they opened it, assuming they weren't infected already.
Leo Laporte / Steve Gibson (01:02:51):
And if that wasn't enough on its own office, macro malware could deliberately distribute itself. Instead of waiting for you to send a copy to someone by reading your email address book and sending itself to some many, or all of the names it found there, the first macro malware, which spread by means of infected word files appeared in late 1995 and was dubbed concept. Remember that, because at that time it was little more than a proof of concept. And we, you know, the concept virus was a thing. That's what it was, but it quickly became obvious that malicious macros were going to be more than just a passing headache. Microsoft was slow to come to the cybersecurity party, carefully avoiding terms, such as virus, worm, Trojan, horse, and malware resolutely, referring to the concept virus as nothing more than a prank macro over the years. However, Microsoft gradually implemented a series of functional changes in office by incrementally, for example, variously first, making it easier and quicker to detect whether a file was a pure document.
Leo Laporte / Steve Gibson (01:04:21):
Thus swiftly differentiating, pure document files and template files with macro code inside in the early days of macro viruses. Back when computers were much slower than today, significant and time consuming malware like scanning was needed on every document file, just to figure out if it needed scanning for malware. He says Microsoft also made it harder for template macros to copy themselves out into uninfected files. Unfortunately, although this helped to kill off self spreading macro viruses, it didn't prevent macro malware in general. Criminals could still create their own booby trapped files upfront and send them individually to each potential victim just as they do today, without relying on self replication to spread further. He also noted that they, the Microsoft popped up a dangerous content warning, so that macros couldn't easily run by mistake. As useful as this feature is he wrote because macros don't run until you choose to allow them crooks have learned how to defeat it.
Leo Laporte / Steve Gibson (01:05:30):
They typically add content to the document that helpfully explains which button to press often providing a handy graphical arrow point pointing at it. Click allow here, click here. Yes. With a little and giving a believable reason that disguises the security risk involved and finally said adding group policy settings for stricter macro controls on company networks. For example, administrators can block macros all together in office files that came from outside the network so that users cannot allow, cannot click to allow macros to run in files received via email or downloaded from the web, even if they want to. So he says at last, in February of 2022, Microsoft announced to size of collective relief from the cybersecurity community that was planning to turn on the inhibit macros in documents that arrived from the internet by default for everyone all the time, the security option that used to re that once required group policy intervention was finally being adopted as a default setting.
Leo Laporte / Steve Gibson (01:06:50):
In other words, as a business, you were still free to use the power of VBA to automate your internal handling of office documents, but you would not, unless you went out of your way to permit it, be exposed to potentially unknown UN untrusted and unwanted macros that weren't from an approved internal source. And of course, yay. As this podcast celebrated at the time Microsoft described that change then by saying, VBA macros obtained from the internet will now be blocked by default for macros and files obtained from the internet. Users will no longer be able to enable content with a click of a button. A message bar will appear for users, notifying them with a button to learn more. The default is more secure and is expected to keep more users safe, including home users and information workers in managed organizations. So, you know, everybody was excited about that.
Leo Laporte / Steve Gibson (01:07:57):
Sofa was, was enthusiastic too, although a little bit less so than I was at the time back then, they said, we're delighted to see this change coming, but it's nevertheless only a small security step for office users because VBA will still be fully supported and you will still be able to save documents from email or your browser, and then open them locally. The changes won't reach older versions of office for months or perhaps years given that changes that that given that change dates for office 2021 and earlier haven't even been announced yet they wrote mobile and Mac users. Won't be getting this change and not all office components are included. Apparently only access Excel, PowerPoint, vio, and word will be getting this new setting. On the other hand, that's, you know, that's by far the majority of office things. So anyway, Leo, you have the, so the news I was reporting yesterday was that they decided well actually what Microsoft said last week was following user feedback, right?
Leo Laporte / Steve Gibson (01:09:12):
We have rolled back this change temporarily. I more temporarily than I thought while we make some additional changes to enhance usability, they said, this is a temporary change. And we are fully committed to making the default change for all users, regardless of the default setting, customers can block internet macros through the group policy settings described in the article block macros from running in office files from the internet. We will provide additional details on timeline in upcoming weeks. And oh boy, look at that flow down. So, you know what happened, which was they. So until recently it would be a popup. Let's say there's a macro in here and then away a button that said, yeah, go ahead, run it. And that was just too easy. So what they were gonna do is take that button, move it into the properties of the document. So you'd have to know to get the info on the document, go to the properties, check a box, run the macro.
Leo Laporte / Steve Gibson (01:10:10):
And I think pretty clearly what happened is a lot of businesses said but no, but it's too hard and we have to train people how to do that. So initially Microsoft said, oh, okay, we're not gonna do that. Now. Of course, everybody else has said, no, no, that's too easy. <Laugh>. And so they've kind of backed off on that. This is according to the Microsoft blog post, this is the new way to do it. And you could see that new, do you have to click your heel three times? Well, so basically if there's a macro, a VBA macro in there, yeah. These are the, this is the decision tree. And if it's from a, if, if it's from a trusted location, if it's digitally signed and trusted publisher, blah, blah, blah. It used to be that you could use group policy or cloud policy to block or unblock.
Leo Laporte / Steve Gibson (01:11:03):
But now if you haven't, if none of that's true, you get this final flow through where in fact office default macros blocked. So show trust, bar security risk with learn more. This is what we were talking about. And then, okay, there will be a process. So it looks like they're gonna kind of bring that back, but to make businesses happy, there are a lot, lot of situations yeah. Allow them to be signed. I mean, that's gonna, if it's signed, if it, if you op it was a previously trusted document, you know, so, and you'll still have group policy that can default to block or unblock. So this actually is Microsoft. They have to compromise all the time because business users, right? Yep. It is so sad though, that it is so difficult to turn up the security well, and now, you know, why now?
Leo Laporte / Steve Gibson (01:11:53):
You know why? No, you know, every business says, well, yeah, but I don't wanna retrain employees. We need those macros. We use them in our, you know, weekly spreadsheet flow. And we don't want to have to have them do all that. So, wow. I think this is, this is the process and it's a good process ultimately where all the stakeholders get to weigh in, you could, and then you just put, you push it in the direction you want to incrementally just like Google does. Right. And so you can see Microsoft's heart is in the right place. They wanna do this. And they just kind of do it in a way that it doesn't upset people as much as it did, I guess. Yeah. <Laugh> yeah. It should be, you know what, for all Microsoft home users, you should be off, but that's, they're not gonna do that either, you know? Yeah. You're right. That, that would absolutely. Yeah. Yeah. Anyway, so yeah, they, they rolled back the rollback <laugh> wow.
Leo Laporte / Steve Gibson (01:12:46):
That's what tech Crunch's headline is, is Microsoft rev reverses its reversal. <Laugh> <laugh>. Wow. Okay. So motherboard publish an interesting story under the headline. This is the code, the FBI used to wire tap the world. Oh yeah. Wasn't that interesting? Yes. Yeah. And they followed that opening up with the subheading. Motherboard is publishing parts of the code for the <inaudible> encrypted messaging app, which was secretly managed by the FBI in order to monitor organized crime at global scale. And, and you nailed it by the way. I know you figured it out. You figured out how they did it. That's very smart. Yeah. Well, I actually talk about that here, here in a second, but you're right. They, they did it the way I had keep saying this is the way you would do it. So what I thought was interesting is that the approach that motherboard says the FBI took to pull, pull this off was precisely of the solution.
Leo Laporte / Steve Gibson (01:13:56):
I've often hypothesized as being that, you know, obvious way in which an end to end multi-party messaging system would be compromised. So here here's how mother board story begins. They said the FBI operation in which the agency intercepted messages from thousands of encrypted phones around the world was powered by what motherboard described as actually they had people describing as cobbled together code. Okay. I disagree with the characterization. They used open source code for X, M P for an X MPP encrypted messaging system. So it's like, okay, you know, I guess you could describe open source is cobbled together. It all kind of is, but, okay. Anyway, they said motherboard has obtained that code and is now publishing sections of it. That show how the FBI was able to create its honey pot. The code shows that the messages were secretly duplicated and sent to a ghost contact, that it was hidden from the user's contact lists.
Leo Laporte / Steve Gibson (01:15:10):
This ghost user in a way was the FBI and its law enforcement partners reading over the shoulder of organized criminals. As they talked to each other. Now, our listeners will recall that this has been my greatest cons, my greatest criticism of any supposedly private and secure system where a user's keys are being in any way managed for them. The reason that FEMA's approach has always appealed to me is that the user is 100% responsible for their own key management. And as we've often observed, if you are not managing your own keys, someone or something is managing them for you because the one thing any secure and private instant messaging system needs is keys. The point being key management must be occurring somewhere. So if it's not something you're doing for yourself, then you don't have any direct control over what's going on. Okay? Now that's not to say that.
Leo Laporte / Steve Gibson (01:16:20):
I think people should be doing their own key management. You know, when today's podcast is finished, I'll shoot an iMessage to my wife, Lori, and let her know that I'm heading home. My point is top level, state secrets are not being exchanged in my iMessages. The fact is when you get right down to it, no consumer smartphone can really be trusted. Absolutely. But again, most people don't need that level of secrecy. Anyway, motherboard continues. They wrote last year, the FBI and its international partners announced operation Trojan shield. I love the name in which the FBI secretly ran an encrypted phone company called a no for years and used it to Hoover up tens of millions of messages from a no users, a no was marketed to criminals. It ended up in the hands of over 300 criminal syndicates. You gotta love this worldwide. The landmark operation has led to more than a thousand arrests, including alleged top tier drug traffickers and massive seizures of weapons, cash, narcotics, and luxury cars.
Leo Laporte / Steve Gibson (01:17:49):
So, wow. The FBI mounted a good old fashioned high tech sting operation, good going, but motherboard doesn't sound very impressed with the FBI's coders. They wrote motherboard has obtained the underlying code of the ANAM app and is now publishing sections of it due to the public interest in understanding how law enforcement agencies are tackling the so-called going dark problem, where criminals use encryption to keep their communications out of the hands of the authorities now. Okay. I'm unconvinced that there's any true public interest here, but okay. You know, mostly motherboard seems to want to embarrass the FBI over what they think is the, the low quality of the code they wrote. The code provides greater insight into the hurried nature of its development. The freely available online tools that a NAS developers copied for their own purposes also known as open source and how the relevant section of code copied the messages as part of one of the largest law enforcement operations ever.
Leo Laporte / Steve Gibson (01:19:08):
They said the app uses X M PPP to communicate a long established protocol for sending instant messages. You know, Jaber uses XMPP on top of that. A N wrapped messages in a layer of encryption X PP works by having each contact use a handle. They wrote that in some way, looks like an email address for a nom. These included an XMPP account for the customer support channel that a non users could contact. Another of these was bot <laugh>. Now I do think it was a little UN artful for them to name the secret account bot, but okay. Unlike the support channel bot hid itself from a NM user's contact lists and operated in the background, according to the code and to photos of active anomal devices obtained by motherboard in practice, the app, the app scrolled through the user's list of contacts. And when it came across the bot account, the app filtered that out and removed it from view.
Leo Laporte / Steve Gibson (01:20:24):
So in that sense, a little bit like having a root kit that finding is corroborated by law enforcement files, mother board obtained, which say that bot was a hidden or ghost contact that made copies of a NA users, messages authorities have previously floated the idea of using a ghost contact to penetrate encrypted communications in a November, 2018 piece published on law fair, Ian levy and Chris Robinson, two senior officials from UK intelligence agency G GCHQ wrote that quote, it's relatively easy for a service provider to silently add a law enforcement participant to a group Uhhuh. I know Leo to a group chat or call and quote, you end up with everything still being encrypted end to end, but there's an extra end on this particular communication Uhhuh. Wow. Yeah. The code also shows that in the section that handles sending messages, the app attached location information to any message that is sent to bot on top of that, the Android manifest dot XML file in the app, which shows whi which permissions an app accesses includes the permission access, fine location, as in fine grained location.
Leo Laporte / Steve Gibson (01:22:00):
This confirms what motherboard previously reported after reviewing thousands of pages of, of police files in an a non-related investigation. Many of the intercepted, a non messages in those documents included the precise GPS location of the devices at the time the message was sent. So, yeah, I mean, this is a golden honey pot operation motherboard concluded their story by noting that operation Trojan shield had been widely successful. And that on top of the wave of thousands of arrests, authorities were also able to intervene using the intercepted and cloned messages to stop multiple planned murders using a well-established open protocol and open source software allowed the application to be assembled without excessive cost. And it got the job done. Mm. And I just say, you know, well going, I thought, I thought that was, you know, a very nice piece of work. Wow. Okay. We have some closing the loop bits and our final discussion.
Leo Laporte / Steve Gibson (01:23:14):
Let's take our last break, Leo. Okay. I'm gonna, I'm a little parched and then we'll do that Delio. Yeah. I mean, I guess, you know, now that it's known how to do this law enforcement can do it all sorts of places. Our show today brought to you by those good folks at Canary. We, I have my Canary right here. Let me just show you, it's just a little thing you might say, well, what good is that? What is that a hard drive? Leo looks like a little external hard drive. Doesn't it? Well, what good is that? You say, how does that help your security? Well, the light, I see the lights on the light is on and someone's home. <Laugh> the thinks Canary that's that's whose home thinks as a, a company has been helping governments and companies break into systems.
Leo Laporte / Steve Gibson (01:24:03):
They're they're experts. I guess you'd call that kinda like pen testing, right? And they've taken what they've learned over two decades of teaching companies and militaries and governments, how to break into networks and built the Canary, a honey pot that's trivially, easy to deploy, and yet is gonna give you the information you absolutely need, because after all, it's one thing to keep people out. But if somebody gets in and, and, and they're gonna get in eventually, how do you know they're there? On average, it takes a company 191 days to realize there's been a breach that's more than six months in some cases. I remember the, the Starwood hack was years Sony. It was almost eight months. And in the meanwhile, hackers are roaming your network, exfiltrating documents, information they can use to blackmail. You looking for weak points, places you back up data, for instance.
Leo Laporte / Steve Gibson (01:25:02):
So they can encrypt that too, where they're ransomware. They don't trigger the ransomware right away. They wait, they, they, they sneak around. They time it perfectly, unless you've got something like this, the thinkt Canary security is a layered thing. I'm, I'm acknowledging that, but this is one of the most important layers, the device that lets you know, somebody's in your network and what's great about the Canary. You don't get a lot of false, like know it ain't false alarms. You just get the alerts that matter. And you get 'em in a way that you want, whether it's email or text message, you get a Canary consult with your canaries. You can, they can notify you through slack. It supports web hooks, which that means you can notify you in a lot of ways. It supports syslog. A lot of people like to do it that way you can, there's an API.
Leo Laporte / Steve Gibson (01:25:48):
You could write your own little alerter. And when you get an alert, it's gonna tell you somebody tried to get into your Canary. Here's the login and password. They use this Canary, you know, and I mentioned this before. You can, you can make, 'em look like anything, a skated device, a windows server, a Lennox server. You can have 'em lit up like a Christmas tree or just one or two carefully chosen services. This is a network attached storage. It's not really, but that's what it looks like to an attacker. Looks like a Sonology it's got a Sonology Mac address. Sonology log on page a attacker has no way of not knowing that's that it's something else. No way of knowing that it's something else. And in the minute they log in, I get the alert saying, Hey, or, and by the way, it will also alert you that somebody's probing the network and you can create something.
Leo Laporte / Steve Gibson (01:26:36):
They call Canary tokens, little documents, PDFs, document files, word documents, spreadsheets, that kind of thing. That scatter around your network. You can make as many as you want. I have for instance somewhere an XLS file that says payroll info. You wanna make it look like something. A bad guy might whoa, a payroll info. I bet you there's some good stuff in there, but the minute he tries to open it, it turns out not an Excel spreadsheet. Nope. It's gonna ping my Canary, which is gonna ping me. This is incredible. This is a great way to feel safe. That there's nobody in your network or to know when there is, it's the Canary in your coal mine, you can deploy 'em anywhere you want. They can look like a router, a switch, a NA server, a Linux box. You can put fake files on them.
Leo Laporte / Steve Gibson (01:27:22):
Name them in ways that get hackers attentions, you can enroll them, enroll them in active directory. I love this. It's a brilliant, brilliant idea. And I, I think it's also something you need. Now, let me give you an example of pricing, Canary. You, you know, some banks might have hundreds of them spread out all over. Some smaller businesses might only have a handful of them. Let's say you decide you want five, five canaries, $7,500 a year. You get five, you get your own hosted console, all the upgrades that support the maintenance free for that year. In fact, if you sit on your Canary and you break it, they'll send you a new one right away. No questions asked all you have to do. By the way, when you're buying your Canary, use the offer code TWI in the, how did you hear about us box?
Leo Laporte / Steve Gibson (01:28:06):
That'll take 10% off the top right away. And for the rest of your usage, as long as you want to use it for life. Now, if you're saying well, okay, but I'd like to try before I buy. No problem. Canary has a two month money back guarantee, full refund. So 60 days to see, but I gotta warn you. Don't be disappointed if you don't hear from your Canary. That's a good thing. That means there's nobody in your network. In fact, I've only heard from my Canary once. And it was because somebody put a network attached storage device on our network that went out and was probing every port. And the Canary said, I've just been probed by a device at 10.1 0.3 point 72. What? That's inside the network. We went and we looked and yeah, one of one of our hosts, Megan had connected.
Leo Laporte / Steve Gibson (01:28:56):
Well she was reviewing I don't know if it's a Western digital, one of those, you know, my drive type devices. And it went out and looked at every port on the network, needless to say we disconnected that device. But that's how I know my Canary works. Don't be surprised if you don't hear anything. That's the good news, right? Just go to canary.tools/twitt. Again, the offer code twit gets you 10% off for life. Put that in. How did you hear about us box? These are a must have a big, big part of your overall security status. Just having some canaries, waiting for a bad guy to get in, knock on wood. They never will get in, but you don't want to be that company that finds out six months later, they've been roaming the network this whole time. If you wanna see what others say about Canary canary.tools/love, bunch of tweets from some big names in security, love Canary, you will to canary.tools/twit offer code TWI.
Leo Laporte / Steve Gibson (01:29:51):
Don't forget that. Okay. Back to Steve. Some feedback. Yeah, we got some great listeners who tweet this is SG GRC, mark Toms. He said, how should I vet client side third party exes. I use as part of my web application. How could I verify it's not malicious? He says example neurodynamic.com, JS print manager, utility to allow silent printing from a website. And you know, my go to is virus total. If I it's, it is, we've talked about it before. It is a something like 70 plus different virus engines look at something and I've I use it all the time. You know, if I'm downloading something like, for example, when I'm working on spin, right? And I'm, I'm needing to, to do debugging on a, an ancient motherboard that has some strange land adapter. I need to get the motherboard on the net.
Leo Laporte / Steve Gibson (01:31:03):
I've gotta find the a device driver for the land adapter. You know, I go on the internet and I'll like, find it at like, it looks like it's the right thing, but it's like, eh, kind of a sketchy site. So I I'll take it and, you know, drop the files on, on virus total and have them, you know, give it a scan. Oftentimes virus total has seen the exact file that I'm dropping already, because what it does is the first thing it does is it makes a hash of the file to create a signature. And then it just looks up the signature. And so it'll say, yep, already seen this one, but you can ask it to, re-scan it just for your own piece of mind, if you want to anyway, virus, total.com at, you know, it's a free service. They're getting the benefit of lots of input from people who are wondering what this is.
Leo Laporte / Steve Gibson (01:31:54):
Yeah. And I'm, I know anybody who's listening to the podcast has heard me talk about it often because that's what security researchers use. The, the, and they'll in fact, if they find something they're, they're able to go back and look at the first time VI that somebody else submitted it to virus total in order to get some sense for how long a piece of malware has been roaming around the internet. So anyway a great solution for just checking out stuff that you're not sure about and, you know, free the price is right. Isaiah tweeting from boosted 37, he said at SG GRC, you often recommend a separate O network from the main one. However, devices like Chromecasts require your phone or tablet to be on the same network as the streaming stick, to manage a show. How would you recommend separating those from your main network?
Leo Laporte / Steve Gibson (01:32:51):
That's a good question. I've had the problem myself. I do have stuff, as I've said on a separate private guest network I'll just switch my wifi from one or the other. I don't normally it now, the Chromecast would be more difficult cuz you're wanting to be using it probably all the time. And I guess I would say that it's a less sketchy device than some $5 plug that you got, you know, in a you know, a flea market or a, you know, garage sale somewhere or, or <laugh> or freshly off of Amazon for that matter. So I, I, I, the, the, the solution I've used is that, you know, my various devices, my iPhone, my iPads, they've got, they know the passwords for both networks and I'm able to switch back and forth between them with relative ease. So in the case of a Chromecast, you may want that to, you may trust it enough for it to run on your main wifi, but not your, you know, less trust, trustworthy devices, which you probably also don't need to access on a daily basis.
Leo Laporte / Steve Gibson (01:33:58):
You know, you, you set the schedule for a an outlet or a, a light switch, and then you let it go. And, you know, until daylight savings, time changes, Tom. Terrific. He said, you mentioned that you used an Asus router that you really like, which model is it? It's time for me to buy a new router and I always take your advice. Thanks, Tom. Okay. So I, I haven't researched routers recently. It happens at the one I'm using, I still like, and that's anus RT AC 68 U which is now at version three. So it looks like, you know, it wasn't something that lived for just a short time. I looked it up at Amazon tells me that I purchased it from them on a, in October of 2017. So I know exactly when that's, when I was setting up my life with the woman who became my wife back in October of 2017, almost five years ago.
Leo Laporte / Steve Gibson (01:35:03):
So it it's an AC 1900 wifi gaming router you know, again, model RT AC 68 U looks like it's highly rated on Amazon. So anyway, that's what I'm using. I don't know that it's the best. There are cheaper routers. I think it's like $119 at the moment for a prime subscriber. And in fact, I think today's prime day. Maybe it's even cheaper if you're a, a, a prime person. I don't know. Anyway, that's that one and Michael Horowitz who knows his way around routers. He was for years the columnist. I don't know if he still is at computer world. He did his defensive computing column. He tweeted, he said about your Asus router. <Laugh> he said, are you sure the networks are isolated? Now, remember I mentioned that this thing I discovered had either three or four, I don't remember which three or four guest SSIDs.
Leo Laporte / Steve Gibson (01:36:03):
He said, you might find all the guest SSIDs share the same subnet. He said, I no longer have an a Jesus router. So can't verify. And actually, if they, if he's thinking them, they might share the same subnet. Then I guess I could test that. I was thinking that I'd have to actually try to send data across guests, subnets to see if they're individually isolated from each other. But I should mention also when I went over to Michael's defensive computing site, that pointed me to his fencing computing checklist, Leo, this is the kind of thing I bet you would like. It's defensive computing, checklist.com, but I also made it this week's shortcut of the week. So you can get to it more easily, or at least by typing fewer characters, GRC, SC slash 8 79. Look how tiny the scroll thumb is. This looks like your, I think I know why you like this.
Leo Laporte / Steve Gibson (01:37:02):
This is, this is pure HTML, baby. It is just the facts. Amen. Java frontier. No. Sure. Yes, the facts. But if you scroll, you'll notice that the thumb is not moving down on the right, because there, the, this page is long page, so long, long page. What it is is, is a page of advice and it is really good advice. It's like, you know, like just all kinds of stuff. So I, I just think our listeners often know about it for their own purposes. And also if they wanna recommend it to people, there's just lots of information there on this massive page, grc.sc/ 8 79, or defensive computing checklist.com. It ain't a checklist. It's just a list. <Laugh> it is you're right. It's not a checklist long list. It is a long list. Just like, like, like Michael's collected ideas and thoughts about security over time.
Leo Laporte / Steve Gibson (01:38:10):
It should be a book. This would actually, and I I'll probably mention it on the radio show cuz there is so much good stuff in here. This is really, it is really, really, really good stuff. Yeah. also when I went there and at the top of that page, but also his main page, there's a note that he'll be giving a presentation on defensive computing at the hope conference in New York city, about 11 days from today. It's actually called a, a new hope. I'm sure. Probably hope is hackers on planet earth just in case ex exactly. You didn't know that. Yeah. Ha hackers on planet earth. And wasn't a new hope what, yeah, yeah. The original star wars. Yeah. Their original star wars episode three and new hope, new hope. Yeah. And I'm sure that's what that, that's what they're, you know, they they're they're well, I think they suspended for a while, so that's probably why it's the new hope I, I think they did because they also talk about, I, I went there in order to, to see what was up and they talk about this will be their first in person gathering.
Leo Laporte / Steve Gibson (01:39:15):
Yeah. No doubt since the COVID lockdown mess. So anyway, there is a, it's a three day conference. It's not free $200 for in person, all three or streaming live for 99. This to be a great about it. A great hacker conference. Yeah. Turn, remember the 2,600 sponsored it or not. I, I feel like it was related to 2,600 at the time, but yeah. And of course that's the famous frequency that right. That and hacker was, it was used with used in order to, to disconnect the, the normal communications during a long business call and drop you down to the billing layer right. Where you could do a so-called phone freaking back in the days. Yeah. Anyway, finally, Simon Durham, episode four, he said, sorry, not three, four. What was it? Four? I thought, yeah, it's four. Because remember he started in the middle, he did four, five and six.
Leo Laporte / Steve Gibson (01:40:07):
That's always bugged the crap outta me. It was like, what was, where, what happened the first he, I think he was being clever because I mean, you don't do that and say, oh yeah, I'll be definitely making nine of these. I think he was just being clever, but then it turned out <laugh> oh my God. And then we had to put up with the first three. Yes. Which were the prequels are not good. Yeah. No. So anyway, Simon, during tweeted, there are obviously good reasons for a company to use a VPN for allowing staff to connect remotely. But what are your thoughts on domestic use? Do you use a VPN yourself? And the answer Simon is I don't, but that's only because during my daily current life, I'm never needing to get online using ops op PNS is a handy abbreviation. Everyone should keep in mind, stands for other people's networks.
Leo Laporte / Steve Gibson (01:41:06):
And Leo, I, I, I grin at the beginning of the show, cuz you were talking about being on shipboard and how you would definitely be using a VPN if my life involved travel so that I was wanting to be online in airports, in coffee houses and hotels. There's no question that a VPN would be the only way I would feel comfortable getting online when I was not at home. You know, this is, this is much less of a problem today where everything is encrypted over TLS with server authenticating certificates. Back at the start of this podcast, everything was being done over HTTP with a brief switch to TLS only when logging in, when, you know, for login forms and credentials were being exchanged. You know, remember when we used to explain that it was important to verify that the URL of a forms submit button right.
Leo Laporte / Steve Gibson (01:42:01):
Was HTT PS and not just HTTP. Fortunately we survived that and you know, who knows that fire sheep and all sorts of other, oh my God. Yes. All things. Yeah. Yep. But it's still true that without universal certificate pinning, which I really don't see ever happening or DNS sec, being used to publish certificates, which we're still a long way from, there's a vulnerability when a malicious man in the middle could have control over our traffic, it's uncommon. I'm sure, but it's probably still possible for state level actors to min their own certificates that our browsers and operating systems will trust. Without question, it's true that the bad guys could be operating at the other end of a VPN end point. Although Leo, your comment about ExpressVPN, changing IPS all the time, that's also gonna tend to make, make the end, the VPN endpoint more diffuse mm-hmm <affirmative> mm-hmm <affirmative> but something about hotel, wifi networking in particular gives me the creeps.
Leo Laporte / Steve Gibson (01:43:11):
I, I, you know, for a long time it was that it was unencrypted and you there's just no way to use a hotel UN unencrypted hotel, wifi, you know, safely. And, and I suppose if I was downloading lots of torrent content, I might wanna hide that fact from my internet provider, but I've always found Torrance to be more troubled than their worth. So I don't care whether Cox knows what I do on the internet. You know, and if anyone was watching my internet use, mostly, it would just put them to sleep. So not a problem for me, but again, I don't use a VPN during my normal daily life because I'm not traveling if I were a traveler then. Yeah. VPN, no question. I'm thinking you watching a lot of manga and anime stuff on Netflix, Japan. That kinda, I'm not thing. Yeah.
Leo Laporte / Steve Gibson (01:44:02):
<Laugh>, I'm not, I'm not needing to appear to be other than in Southern California. Good point. Okay. So the rolling poem and that begs the question. Do you own a Honda and are you sure it's still parked out in front enterprise security researchers at star V lab, maybe it's star five lab one using the handle Kevin 2,600, of course we know where he got 2,600 and the other named Wesley Lee have revealed as Larry David might say a pretty, pretty serious vulnerability in Honda's automobile, keyless entry systems. It rather trivially allows attackers to remotely unlock and start potentially all Honda vehicles currently existing on the market. It's it's, it's really like sobering. Okay. So it works in a way that's similar to, but much easier to pull off than that recently discovered Bluetooth replay attack, which we talked about, not that long ago, affecting some Tesla cars both use readily available off the shelf, SDR software defined radio equipment and which allowed the researchers to eaves drop and to capture codes, then broadcast them back to the car in order to gain access, recall that we talked about this related attack to what I mentioned that, that affected Teslas.
Leo Laporte / Steve Gibson (01:45:54):
And it was very clever. The key fob produced a high quality cryptographically, unpredictable pseudo random sequence of codes, which are derived from a monotonically increasing counter, which is that encrypted by an unknown shared secret key. So the vehicle knows the key. So it's able to decrypt the received code to determine whether it's the next code in sequence or at least forward of the key fob counters, last known position. But the primary security feature is that the vehicle will never accept any code that it has seen previously, or that is, that represents a count behind the most recently seen count that the key fob is known to have.
Leo Laporte / Steve Gibson (01:47:03):
In other words, it will only allow its knowledge of the key F's counter to be moved forward, never backward. Okay. So this would seem to robustly present, prevent any possibility of a replay attack, but not. So in the case we talked about before, what the clever hackers did before was to receive the fobs code while simultaneously arranging to jam its receipt by the car. The user would, would think now after pressing the button and nothing happened because the, the code, the car's reception was jammed, they would think, well, okay, whatever, I guess I was too far away or who knows. So they would press the key fob a second time generate causing it to generate the next success of code in sequence. Now the hacker would capture the second code while replay the first code, which the car had never received and the door would unlock.
Leo Laporte / Steve Gibson (01:48:11):
So the car or the car would start or whatever. And that's, that's the cool part. That's so clever. The attacker would've obtained and retained that second code, which had never yet been seen by the car and would still be available as the next unlocking code in that otherwise unpredictable sequence. Okay. So that was the clever, you know, very active, gotta get involved. I, you know, very much man in the middle, you're an active man in the middle, able to jam, you know, on the fly in real time jam the, the re the receipt of the code by the car today. Honda is the target and their problem is significantly worse. Since the attack on Hondas is almost completely passive and much easier to conduct. The Honda attacking researchers have been able to remotely unlock and start the engines of Hondas dating from as far back as 2012.
Leo Laporte / Steve Gibson (01:49:17):
So a decade ago up to, and including this year. So nothing's been fixed in the last 10 years. The good news is according to the drive, which independently tested and verified the vulnerability on a last year's 20, 21 Honda accord. The key fob attack does work, allows the car door to be unlocked and the engine to be started. But the attacker is unable to drive off with the vehicle, though it, as I said, can start the engine. Presumably the car contains some dynamic, continuous key fob presence technology. That's able to sense the presence of the key inside the vehicle, which at least prevents it from, you know, being drivable. Okay. So the more active attack against Teslas worked, the way I just described what Kevin and Wesley discovered was, as I said, significantly worse, because it is so much easier. They found that the counter in Honda's cars would be resynchronize when the car receives lock and unlock commands in a consecutive sequence.
Leo Laporte / Steve Gibson (01:50:37):
Even when that sequence is from long ago, this means that Honda's counter can be reset to an earlier state. So by being inter, by being induced into moving backwards, this will cause the car to accept codes from previous sessions that should, that should have been forever invalidated after they were used in their writeup. Kevin and Wesley said, quote, by sending the commands in a, in a consecutive sequence to the Honda vehicles, it will be synchronizing the counter. Once the counter is Reed commands from previous cycles of the counter will work again. Therefore those commands can be used later to unlock the car at will. They wrote we've successfully tested the 10 most popular models of Honda vehicles from the year 2012, up to the year 2022, from the attackers perspective, therefore we strongly believe the ver the vulnerability affects all Honda vehicles currently existing on the market, tested and known vulner vulnerable vehicles include the Honda civic, 2012, the Honda X RV 2018, the Honda CRV, 2020, the Honda accord, 2020, the Odyssey 2020, the inspire 2021, the fit 2022, the civic 2022, the V 1 20 22, and the Honda breeze, 2022.
Leo Laporte / Steve Gibson (01:52:20):
So bad. Then we had the always entertaining FAQ from which I will excerpt a couple questions. They asked, why is it called the rolling poem, not a Honda poem. And they answered because this bug may exist in other brands of vehicles too. Am I affected by the bug? As long as a vulnerable Honda vehicle is in use, it could be abused. Is there an assigned CVE for rolling poem? Yep. 20, 21 46, 1 45 is the official reference to this bug. Can I detect if someone has exploited this against me and they wrote probably not, the exploitation does not leave any traces in traditional log files, but considering the ease of exploitation and attacks leaving no trace, this threat should be taken seriously. Is this a Honda vehicle only bug? No. Although the main targets for the research is Honda automobiles. We have leads to show the impact of this vulnerability also applies to other car manufacturers.
Leo Laporte / Steve Gibson (01:53:29):
They said we will release more details in the future is the risk real we've successfully tested the latest models of Honda vehicles, and we strongly believe the vulnerability affects all Honda vehicles currently existing on the market. What makes this bug unique or what's the difference between CVE 20 22, 27, 254 and 20 19 26, 26. In other words, vehicle hacking has a rich history. They wrote during the research, we noted the other researchers have found similar vulnerabilities in Honda vehicles based on the description of quote, the remote keyless system on Honda VR Honda, HR V 2017 vehicles send the same RF signal to each door open request, which might allow a replay attack. Uhhuh. What they found is a simpler, fixed code vulnerability, where an attacker can simply record the transmission in advance and replay it later to cause the door to lock or unlock. However, most modern vehicles, including Honda automobiles implemented a proprietary rolling code mechanism to prevent fixed code replay attacks.
Leo Laporte / Steve Gibson (01:54:55):
The bug we discovered they wrote is in regard to the design flaw in the rolling codes mechanism implemented by Honda motors, which needs to be taken very seriously. Question. Is there more technical information about rolling porn? They said, you can follow the author on Twitter at Kevin 2,600. However, we will not be releasing any tools required to go out and steal the affected vehicles. At a later stage, we will release technical information in order to encourage more researchers to get involved in car security research, which void really does seem to be lacking how to patch the modern automobile for rolling phone bug like this. The common solution requires us to bring the vehicle back to a local dealership as a recall, but the recommended mitigation strategy is to upgrade the vulnerable BCM firmware through over the air updates. If possible, however, some older vehicles may not support over the air and I should mention Honda offers no patching for this and, and indicates they have no plans too.
Leo Laporte / Steve Gibson (01:56:10):
What does Honda think about this rolling phone bug? They said we have searched through the Honda official website, but we can find no contact info to report the vulnerability. It appears that Honda motor does not have a department to deal with security related issues for their products. And the person who works at Honda has told us quote, the best way to report the Honda vulnerability is to contact customer service. Yeah. Right? Sure. That'll that'll work. That'll work. Yeah. Does your seat is your seatbelt tight? You know, are the, are the brake lights working unbelievable. Therefore they said we filed a report to Honda customer service and we have not had any reply <laugh> oh, apply. Yeah, no kidding. It's earlier, earlier in March of this year, the following similar remote keyless entry attacks on a Honda civics follow following, similar remote keyless entry attacks on a hav Honda civics bleeping computer reached out to Honda and learned that Honda had no plans to update any of their older model cars.
Leo Laporte / Steve Gibson (01:57:23):
Bleeping computer wrote Honda told us multiple auto makers that in other words, it's not just us. It's not just us use legacy technology for implementing remote lock, unlock functionality. And as such may be vulnerable to quote determined and very technologically sophisticated thieves. Of course that's until, you know, Amazon starts selling the Honda unlocker for 1995 from China. They said at this time it appears that devices only appear to work with close proximity or while physically attached to the target vehicle. Not so in this case requiring local reception of radio signals from the vehicle owner's key fob when the vehicle is opened and started nearby. Oh, okay. That's true. A Honda spokesperson told bleeping computer in their statement, Honda explicitly mentions. It is not verified. The information reported by the researchers, although others have and cannot confirm if Honda vehicles are actually vulnerable to this type of attack.
Leo Laporte / Steve Gibson (01:58:40):
And one must imagine that Honda doesn't want to know since knowing might make them culpable. And Honda did add that. Should the vehicles be vulnerable? Quote Honda has no plan to update older vehicles at this time. And it's important to note while Honda regularly improves security features, as new models are introduced determined, and technologically sophisticated thieves are also working to O overcome those features. In other words, we give up <laugh>. So, so all this begs the question, why does this appear to be such a difficult problem to solve both the Tesla style forward only counter advance and Hondas? Bidirectional settable counter solutions are transparent to their users. In other words, you know, the keys just work, right? But Tesla's forward only system is clearly superior from a security perspective on a Honda, the ability to passively record a series of unlocking codes, which can then be replayed at any time later, seems like a significant oversight that any engineer who has designing this system would've understood, of course they would.
Leo Laporte / Steve Gibson (02:00:09):
One thought is that there are likely some intellectual property issues here. There's no question that the first implementers of such rolling codes would've sought patents. That thought led me to ask the Google where I immediately found us patent 6 2 25, 8, 8, 9 titled method of producing rolling code and keyless entry apparatus. Using the same. The abstract of the patent starts off reading a rolling code. Producing method is provided, which may be employed in a keyless entry system for automotive vehicles designed to compare a rolling code derived in a receiver installed in the vehicle and a rolling code derived in a portable transmitter to allow authorized access to the vehicle. If both rolling codes match the rolling code producing method includes producing different rolling codes, thus rolling in sequence using an initial code variable, according to a given algorithm and changing the initial code variable in response to insertion of an initial code variable memory card carried by a vehicle operator into the receiver.
Leo Laporte / Steve Gibson (02:01:36):
Okay. Now the good news is this patent was issued in 1995 and it expired in 2016 around the same time. Also in 1995 garage door openers were suffering from the same lack of security. So Brad Ferris and James Fitz given invented, and I have that in quotes, a similar system for their garage door opener employer, the Chamberlin group, and obtained us patent us 4, 4, 6, 8, 8 69 5. There's been a lot of litigation over these patents through the years. Then there's a long trail of bodies, but that's what the patent system does, right? It mostly amounts to a significant source of revenue for intellectual property attorneys, but all of these various patents appeared to have finally expired back in 2016. So it's unclear why Honda would still be using their broken system today. They apparently were back in 2012 maybe to avoid any litigation or having to, you know, license somebody else's patent.
Leo Laporte / Steve Gibson (02:02:52):
It was Nipon that got the auto patent back in 1995. But it appears that for at least the past six years, there's been no reason not to move to a much stronger forward only counter scheme, such as what Tesla and presumably others have implemented. You know, overall, this truly is I, if not a difficult, at least a little more expensive problem to solve it, it is difficult to robustly solve it in a one way only system. The ultimate way to solve the problem is for there to be a full handshake. The user presses the button on the key fob, which sends a fixed code, ping out into the world, identifying itself to any car within range. The car that key is registered to receives the hello. It's me ping and replies with a non challenge. The key fob receives the non challenge and either reversibly encrypts it under its shared secret key, or hashes it with an H Mac keyed with a shared secret, either way.
Leo Laporte / Steve Gibson (02:04:23):
It returns the result of that cryptographic operation to the car, which verifies that the key fob must know the secret they share. So the car performs the requested action, that system while ultimately secure and internet proven is significantly more expensive since now both the key fob and the car must support by directional communications. The key fob must also be able to receive, and the car must also be able to transmit given the cost and the complexity of this full solution and the comparatively small, additional security margin provided above the forward only counter advancement used by Tesla and presumably other forward thinking auto makers. I would say that the small added security is probably not worth the cost, but given that forward only counter technology has been freely available in the public domain unencumbered by any patent licensing requirements, since at least 2016, Honda's continued use of reset counter protection since then can only be ascribed as them just not caring, given the popularity of Hondas.
Leo Laporte / Steve Gibson (02:05:50):
And who knows what other car makers may also have been similarly lazy, the relative ease of collecting key fob codes and the ability to later replay them in an entirely passive attack, likely opens Honda to some future consumer litigation. I would think so. We'll see what more we hear of this in the future. <Laugh> fun stuff. What so does that mean if you have a Honda, you should keep your fob in a bag. One of them mesh bags? No, no. That won't solve the problem. Why? It, it really means that, you know, there ISNT solution, you need a padlock on your contour. It does, it does mean you're screwed. It means. I mean, essentially it means that that, I mean, this completely defeats the replay. The fact is this is in that's inexpensive hardware to do this. Now it just, you know, a, a, a little SDR that you can buy on, on, on Amazon, a software defined radio and, and if, you know, borrow a friend's Honda fob, you know, see how it works, capture the codes, and then you could capture the codes from anybody else.
Leo Laporte / Steve Gibson (02:07:03):
Wow. And now we, and now we know that basically this renders the, the forward only protection completely vulnerable for a long time. Honda Accords were the most stolen cars in America. I, I think they're gonna reclaim their crown Honda anythings, apparently <laugh> oh, wow. So it may well be that you can't drive off with a car, but you certainly don't wanna put any, you don't wanna leave anything, you know, important. You don't wanna trust your car door locks essentially. Right. Is what it means. Right? The number one car in America stolen Honda civic, number two Honda accord. Wow. And I, I don't know if that's related to this. Probably not just to their desirability in the stolen car market, but still, and the, their, yeah. Their generic nature. Their genericness. Yeah, yeah. Cuz the camera's third, the Nissan Altima's fourth, man. I, if I'm gonna steal a car, I must steal a Hummer.
Leo Laporte / Steve Gibson (02:08:02):
I gonna steal a Jaguar. You are a portion. I have some fun that gets some good. Yeah. And, and arrested. Taken away. Yeah. Actually, maybe that's old because now I'm looking now this is May 13th. Yeah. I'm saying number one is a Ford pickup. <Laugh> also popular. You know, I have on my Ford, I, I hope it's a good technique, but I have on my Ford, a many Fords do have a keypad on the thing. And it, unfortunately it's only four digits. No, I guess it's more than that. And the ones I've seen, they use all 10 digits, but they double them up on five keys. That's the problem. There's only five keys. So it's like, what the hell? And I think this is related to what Honda is doing, cuz it's basically cheapness right. Use the cheapest possible components. Yeah. Right. Five keys is half the price of 10.
Leo Laporte / Steve Gibson (02:08:53):
It would be nice to know. I mean, cuz everybody now has key fob unlock. Right. I mean like, you know, I mean even, and car and car start Leo, even I what have key, I do have to still, I have to stick it. So turn the key slot and, and twist it. Yeah. I gotta do that's fashioned. Yeah. But at least it at least I've got the FBA watching. Wow. Interesting. What a world. All right, Steve. Great show is always we're gonna miss you next week. I won't be here. Jason. Hell take over for the day. I will be back the following Tuesday. I'm going on that twit cruise with 120 devoted fans who I am sure to a person will say tell Steve high. That's I, no matter where I go, that's what I get. Tell Steve. Hi. So hi <laugh> Steve Gibson is@grc.com.
Leo Laporte / Steve Gibson (02:09:50):
You can tell him, hi yourself. Just go to grc.com/feedback. While you're there, pick up a copy of spin, right? The world's best hard drive, sorry, mass storage, maintenance and recovery utility. Soon to be 6.1, version six, the current version you'll get a free upgrade of six one. If you buy six today, you also get to participate in the development of 6.1, which is imminent. While you're there, you can also get a copy of the show. Steve has two unique versions of security. Now a 16 kilobit version for the bandwidth impaired and really nicely done human written transcripts. So you can read along as you listen, but you could also use it to search and find a part of the show that you're looking for. Grc.Com, the place to go he's on the Twitter at SG GRC. You can DM him there as well.
Leo Laporte / Steve Gibson (02:10:41):
At SG GRC. We've got copies of the show at our website, twitter.tv/sn. We also have a YouTube channel devoted to security now makes it easy to share. You can send people clips and of course you can subscribe on your favorite podcast client and get it the minute it's available of a Tuesday afternoon club. TWI members don't get any quicker, but they do get a shorter version. The ad free version club, Twitter is seven bucks a month ad free versions of all the shows. Plus you get the discord, the fabulous twit discord, which is really a wonderful community and growing and the twit plus feed go to twit.tv/club TWI. If you'd like to join, thanks in advance. It really helps us. It's gonna, we're gonna launch new shows, thanks to club twit, lots of them. We also have shows inside the club that we don't have outside the club like the Stacy's book club and the space this weekend space is now public.
Leo Laporte / Steve Gibson (02:11:36):
That's one of the things the club does, which it gives us a chance to launch a show, brand new, no advertisers. So the club members support it and then once it kind of gets on its feet, we can put it out incubate. It's an incubator. Exactly. so we really appreciate that there's yearly subscriptions as well. And I should mention we are gonna add, we've been doing it through iTunes, but we are gonna now add individual show subscriptions. So if you say, well, I don't wanna pay seven bucks. You can just get security now add free for 2 99 a month. Those, if they're not up yet will be up soon. Thanks to mefor. We're able to do that as well. So again for more information, twit.tv/club TWI, we do the show every Tuesday, right after Mac break weekly that's one 30 Pacific, four 30 Eastern, 2030 UTC live audio and video streams are, are at live, do twi.tv chat rooms@ircdottwi.tv. That's open to all. And after the fact Steve's got forums@grc.com, we've got forums@twi.community. Those are free and open to all twi.community. There's also twit do social, which is a Mato on instance. If you've had enough of the Twitter nonsense, Mato on is a great distributed federated micro blogging service. We really love that's twi.social. And I am in both TWI community and twi.social on a regular basis. So we will see in there. Thank you Steve have a great week. We'll see you next time on security now day, buddy. Bye.
Rod Pyle (02:13:08):
Hey, I'm rod Pyle, editor of ad Astra magazine, and each week I'm joined by Tark. Mallek the editor in chief over@space.com in our new this week in space podcast, every Friday, Tark and I take a deep dive into the stories that define the new space age what's NASA up to when will Americans, once again set foot on the moon. And how about those samples from the perseverance Rover? When do those coming home? What the heck has Elon must have done now, in addition to all the latest and greatest and space exploration will take an occasional look at bits of space flight history that you've probably never heard of and all with an eye towards having a good time along the way. Check us out on your favorite podcaster.