Security Now Episode 853 Transcript
Please be advised this transcript is AI-generated and may not be word for word. Time codes refer to the approximate times in the ad-supported version of the show.
Leo Laporte (00:00:00):
It's time for Security Now, Steve Gibson is here. He's gonna explain answer Paul Thurrott's question. What exactly is a Pluton? We'll talk about success for the brave browser, more log for J vulnerabilities, and then a very interesting deep dive into the problems with URL parsing and why so many programs get it wrong. It's all coming up next on security. Now,
Steve Gibson (00:00:27):
Podcasts you love from people you trust. This is TWiT.
Leo Laporte (00:00:31):
This is Security Now with Steve Gibson episode 853 recorded Tuesday G January 11th, 2022 URL parsing vulnerabilities. Security Now is brought to you by Arons. Arons has collected tools, advice and practical guides from their global community of MSP partners and their network of it. Channel gurus to help you make your MSP business dream a reality. Check out the Arons MSP jumpstart program. Go to go.arons.com/twit-one for tools and resources to help you evolve or start your it business. And by Barracuda every 11 seconds, there's a new ransomware attack cost and is millions of dollars. Barracuda says don't pay the ransom, build your ransomware protection plan. Now go to barracuda.com/securitynow, and by express VPN express VPN is ridiculously fast. You can stream everything in HD quality with zero buffering for three extra months free with a one year package, go to express vpn.com/security. Now it's time for security. Now the show we cover the latest news from the world of security. Thanks to our professional security analyst, Steve Gibson of grc.com. He's ready. I, I like the eyebrows.
Steve Gibson (00:02:03):
If I were to nod and synchronize my eyebrows, they could stay motionless while, while my head moved up, I have to work on that.
Leo Laporte (00:02:12):
And there you see on display. Steve's amazing analytic abilities. It's just how he thinks ladies and gentlemen. Well , hi Steve.
Steve Gibson (00:02:20):
Yo.
Leo Laporte (00:02:22):
Yo, let's get going here.
Steve Gibson (00:02:24):
Yes. Well, so it's 01 11 22. Yes. Security Now 853 a, a team of four researchers, security researchers in the Northeast Massachusetts and New York, I think took it upon themselves to, to look at another aspect of our libraries that we're all using and discovered some really, really interesting problems, which are right now affecting everyone. And anyway, so really interesting topic. I think one of our deep dives, those who do not have the advantage of show notes in front of them are gonna have to, I was gonna say close your eyes, but not if you're commuting. But if you're being commuted, then that would be good. <Laugh> and, and
Leo Laporte (00:03:22):
The governor will call any minute now, I'm sure.
Steve Gibson (00:03:25):
Then, then you'll have to picture some of these, but I'll, I'll, I'll be gentle anyway. I think a really interesting topic of URL parsing vulnerabilities, ah but this week we're gonna begin with another, in our series of Log4J updates, which includes among a few other bits of news, an instance of a real world vulnerability that has has popped up and the FTCs, the us federal trade commission, somewhat surprising and aggressive message relative to Log4J will Chronicle the Chrome browsers first largest update of 2022. And also note the gratifying 2021 growth of the privacy centric, brave browser, WordPress needs updating, but this time, not one of those pesky add-ons WordPress itself. We're gonna then answer the age old question posed during last Wednesday's Windows Weekly podcast, what exactly is a Pluton and how many can dance on the head of a pin <laugh> and find Lee after a quick sci-fi reading recommendation and a very brief touch on my ongoing spin, right work we're gonna take, as I said, a gratifying, deep dive into the unfortunate vagaries of our industries, URL, parsing libraries to see just how much trouble we're in as a result of no.
Steve Gibson (00:04:59):
Two of them are seeing URLs in exactly the same way.
Leo Laporte (00:05:04):
Hmm. Interesting. Fascinating. Might I say engaging content ha as always coming up on security now, and I will for those of you watching video, I'll I'll display the images, but you'll just for the rest of you use your imaginations and then where do people get the show notes? Actually, I should cuz people may wanna, after the fact see them, you have months on, on your website.
Steve Gibson (00:05:30):
Yes. Oh yeah. Yeah. grc.com/security now, and they're, they're already posted good. I did that this morning. So the link is that. Yeah.
Leo Laporte (00:05:38):
So that's, I think perhaps everybody should know that so that they can follow along the transcripts, the show notes, all of that stuff live at Steve's website, new sponsor. Wanna welcome, not a new name. I think everybody who's been around for a while knows a Cronus. Yep. When Lisa said, you know, Cronus, I said, are you kidding? I'd love to do ads for a Cronus. They have some of the best tools out there for managing your PC. I wanna talk about their MSP jumpstart program for managed service providers right now, whether you're working in freelance, it consulting, maybe you're a break fix shop or a small reseller you're in a great position to come invert your it expertise into an established, managed service provider business. That's what we use as an MSP Russell. I've talked about him all the time from expon that's his company, he's our it guy, but he's a managed service provider.
Leo Laporte (00:06:32):
And it's worked out for us as a company very well. Economically, we get rates service from him. He loves it because he has a, we've tried to hire Russell a hundred times, but he loves his Ms. Being an MSP, cuz he has multiple clients in a lot of different areas. And he likes the variety likes moving around. We see him on Wednesdays, but he goes to different places. As you start to build your MSP business, you're gonna develop plans and processes and systems. That's what Russell has done. And it's really, it's kind of amazing because it basically comes equipped, fully equipped. It's a turnkey thing. You'll be doing things that maybe you didn't even know, you needed systems you're gonna set up. The good news is as an it professional, you already have the technical expertise and connections that you need to start supporting your to clients.
Leo Laporte (00:07:19):
And as for the rest, I wanna point you to Acronis. A C R O N I S and particularly Acronis' MSP jumpstart program. It helps people who are experts in it start their own MSP business. They're gonna give you support and advice for every step of your journey. Lots of resources, not just the software that we're all familiar with from Aros, some of the best in the business, but also eBooks on demand webinars with experts in the field, just as a sample kind of, of, of what you're gonna get. This is, this is how Aros is gonna help. Cuz there are four major steps ahead of you. As you build your MSP business from this, this notion of maybe I'd like to do this to a thriving profitable organization. Russell just got back from a, a week long trip to Budapest <laugh> which gives you an idea and a couple of things.
Leo Laporte (00:08:13):
First of all, he's making some good money. But second, he can also run his business from anywhere. So he did not leave his clients in the lurch as he's traveling the world. These are some of the areas you're gonna wanna look at the four major steps. Number one, planning. If you're gonna establish this business as an MSP at a, a business that'll last, you need a clear and well-organized plan understanding of where you can fit into the it channel, what you know, what the Eeds are out there in. When it comes to launching, you're gonna launch your MSP business. It's gonna allow you to flex new strategic business muscles. That's a nice way of saying you're gonna have to start thinking like a business person especially when it comes to marketing, offering your service packages. And again, a Cronus can really help there.
Leo Laporte (00:08:58):
Now of course, now that you've got it off the ground, you wanna keep it running and keep it running successfully. Maybe even keep an eye to expanding and optimizing it again. A Cronus can help there. And then finally scaling, you know, you've got your first client now you're second. Now your third now you're, you've taken your MSP business from an idea to a reality. How do you give it the boost? It needs to keep profits and success growing for years to come. This sounds exciting. Doesn't it? Maybe it's something you wanna do as you approach these steps, you're gonna learn techniques and strategies. That'll help you get your it managed services. Business started with a strong foundation optimized for future growth. Maybe you're in fact already going down this path, Aros can help you wherever you are. Go to the next level, a Kronos, a C R O N I S has collected tools, advice, practical guides, because they work with MSPs.
Leo Laporte (00:09:49):
They there's a global community of MSP partners that works with a Kronos already. They've combined that knowledge. They have a quite a network of it. Channel gurus, all of which can help you make your MSP business dreams a reality. I think this is a great idea. Check out the Arons MSP jumpstart program. It's go.arons.com/twi-one, go.arons.com/dash one to get the tools and resources to help you evolve or even get started in your it business. This is perfect. You know, we've had ITProTV for a while. Give you the skills you need to get into it. Maybe now it's ready. You're ready to go to the next level, become an MSP go dorono.com/twit-one. Wanna welcome Aros to the show cause we're big fans believe in them and I've used their products for years as, as Russell. I know. And I love it that they're offering this kind of advice and expertise to budding MSPs go doro.com/twi-one. Right? Oh,
Steve Gibson (00:10:52):
I love it. Go ahead. So now we know how to pronounce their name. Oh yeah. Is, oh yeah. Arons. It is Arons. Is it Aron? What
Leo Laporte (00:11:01):
Is it? You know, one of the reasons I like doing a radio show is cuz I'm often pronouncing words that everybody's been reading for years for the first time. Yes <laugh> so I get to decide, but I did. I asked Arons and they said, that's how you say, let's get that picture the week you ready? I,
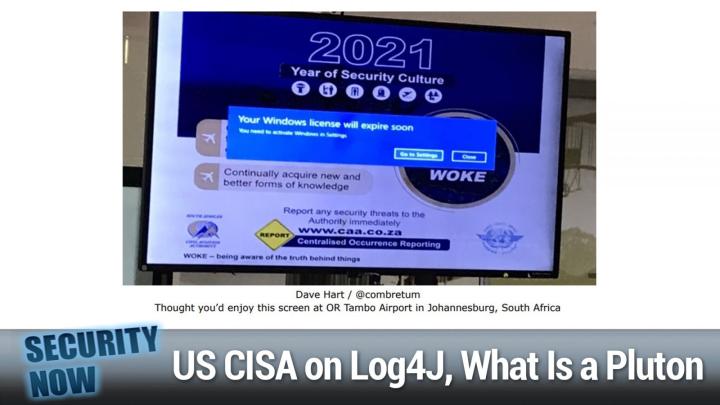
Steve Gibson (00:11:18):
Well, this is another one of those <laugh> oldies, but goodies or I, well, not really old cuz it's 2021, but they never get <laugh>. They never get tired. Someone tweeted this to me, Dave Hart he said, thought you'd enjoy this screen at or Tambo airport in Johannesburg. Oh, South Africa. Wow. And of course this is, and I, I love it cuz it says 20, 21 year of security culture it's boasting about. And you know, it's got, you know, all kinds of extra logos and, and bureaucratic mumbo jumbo and right in the middle of the whole thing. Otherwise very impressive presentation is a blue box, says your windows license will expire soon. It's like, whoops. Okay. What? So this they're running, they're running an unlicensed version of windows or totally that's secure for sure. <Laugh> I, I wasn't aware that windows licenses expired. I mean I've never had a license expired.
Steve Gibson (00:12:24):
No, yeah, yeah, yeah. This is what you get. If you first install windows without giving in an authentication code. Ah right, right. You can run it for 30, 60 or 90 day, but eventually it says, oh no, you gotta, now you gotta enter your, you gotta activate year of security culture. Not so much. Whoops. Anyway, well we got it on the internet. We thought it would work forever. It must. And if only there was a, it says go to settings. If only you could press the settings button, but no, no I that's gonna happen. So anyway, anyway, just another fun little <laugh> bit of Flo. Okay. Our log for J update the us CSA has stated that the log for J the log for shell exploit of the log for J vulnerability has not result in significant government intrusions yet. CSA said, quote, we're not seeing confirmed compromises of federal agencies, including critical infrastructure.
Steve Gibson (00:13:28):
We are seeing widespread scanning by malicious actors. We're seeing some prevalence of what we would call low level activities like installation of crypto mining malware, but we're not seeing destructive attacks or attacks attributed to advanced persistent threats. So it's like, okay, don't relax everybody. But so far, you know, it's not the end of the world. Eric Goldstein, who's the CS A's executive director for cybersecurity said that there would be a quote long tail remediation because of how widespread the issue is. Of course that's what we've predicted too, because of this problem of the Java library, you know, inheritance tree he said CSA estimates that hundreds of mill of devices are impacted. Easterly said, oh, easterly that's somebody else. Anyway, the that CSA is aware of reports of attacks affecting foreign government agencies, including the Belgian defense ministry. And I did pass over a story about that as well as reports from cybersecurity that nation state adversaries are developing attacks using log for shell, but said, CSA cannot independently confirm those reports at this time.
Steve Gibson (00:14:48):
So <laugh> stay tuned. You know, the, the overall security group posture is that that there's scanning being done and implanting occurring to like, like, and there's a race to get, to get systems networks, pen. The exploitation of those penetrations is on a back burner because everyone knows sooner or later, those vulnerabilities that are creating the openings are gonna close. So, you know, it's frightening because it means the bad guys are like <laugh> acting in a, in a smart fashion. And it means to optimize their long term benefit for short term, you know, for stalling the, the glory for just getting into systems. So anyway, I think we're gonna have an interesting 2022, meanwhile, Matt Keller, the vice president of federal services at Guidepoint security told threat post that many agencies are unable to patch the problems arising for log for log log for J due to network connected end of life and end of service systems.
Steve Gibson (00:16:06):
In other words, mission critical systems that are still in service, but which cannot be updated because they've passed out of their maintenance life. You know, there aren't gonna be updates coming from them like, oh yes, you got windows seven, eh, too bad. Anyway, Matt said that federal agencies are relying upon command line scripts to locate affected systems. They're also constructing tiger team as a means of tearing into the massive workload that has resulted tiger teams being specialized cross-functional teams brought together specifically to solve or investigate one particular problem or critical issue between technology issues, which may prove to be in transient restrictions and shipping delays involved in replacing these systems. Keller predicts that agencies are months away from being able to address log for Jay, despite the fact that, you know, the SISA said no Christmas for you until we got this fixed where you're not gonna go home, you're just gonna stay here.
Steve Gibson (00:17:15):
Well, everybody left. And <laugh> so it's gonna still be a few months before things calm down. An example of a specific and unfortunately, typical log for J based vulnerabilities has been found in a popular open source Java based of course, database engine library that Maven Java repository, which Google had plumbed. And we talked about before indicates that this popular it's called the H two database engine is being used <laugh> by 6,807 individual. What they describe as artifacts, meaning, you know up, up tree dependencies or dependence rather we've talked about the tree of depend that one gets when libraries are built from libraries, which are built from libraries. And so on in this case, the, this a HS database appears somewhere underneath <laugh> those 6,807 different high level Java things. And since the, this is an embedded database engine, you know, where you don't even, you typically don't even see it, right?
Steve Gibson (00:18:34):
It's just like your thing, like has a database that comes from somewhere, well, this is where it comes from, but you never really see the H the H two embed. So it might not even be clear to those using it. That access log for J vulnerabilities are buried underneath there. This particular issue being tracked is CVE 20 21 42, 3 92, and has been described as the first critical issue published since log for shell on a component other than log for J that exploits the same root cause of the log for shell vulnerability, namely that J N D I remote class loading Shaar Menina the senior director of JFR security reer re re research said, quote, similar to the log for shell vulnerability uncovered in early December attacker controlled URLs that propagate into J N di lookups can allow unauthenticated remote code execution, giving soul control over the operation of another person or organizations systems.
Steve Gibson (00:19:56):
So basically that's, you know, what we know of is the log for Jay problem. In a nutshell, he added that the H two database is used by many third party frameworks, including spring boot play framework and Jay hipster, while this vulnerability is not as widespread as log for shell, it can still have a dramatic impact on developers and production systems if not addressed. So, yeah, 6,807 of them. The flaw affects H two database versions, 1, 1, 100. So that sounds like almost at the start two up through 2 0, 2 0 4, and it's been addressed in 2 0 6, which was first made available last Wednesday, January 5th. And I should note that the Jay frog folks who I was unaware had their eye on this. I, I, we we'd run across them a couple times before relative to Java stuff. They've got a terrific page of log for Jay and log for shell resources, including a remediation cookbook, free tools to see if you've got the problem and what they call a survival guide.
Steve Gibson (00:21:12):
I have a link to their page and the show notes, but you can just put JRO J F R O G into any search engine and click after you go to their page, click the banner link that they've got at the top of the homepage, and that'll take you to their very comprehensive log for Jay log for shell resources. Yeah, it's right there at the top. Leo. I, yeah, yeah. Is it that little black bar? Yeah, there it is. Yep. And there you are at the, at the resource page, so, so definitely a useful research, a resource for any of our listeners or their friends who part of that month long remediation battle for getting this thing under control. Okay. Now this sort of surprised me a week ago on the 4th of January while we were doing this podcast, the us federal trade commission posted a blow log warning, essentially warning companies to remediate log for J remediate the log for J security vulnerability, the blog's title, their own, the FTCs own blog title is FTC Warrens companies to remediate log for J security vulnerability.
Steve Gibson (00:22:31):
And in its posting, it, it directly threatens companies with legal action, likening it to that Equifax negligence. So here's what the FTC posted. They said, log for J is a ubiquitous piece of software used to record activities in a wide range of systems found in consumer facing products and services. You know, thus the, you know, FTCs charter, they said recently, a serious vulnerability in the popular Java logging package log for J and then they cite the CVE 44. Two was disclosed, posing a severe risk to millions of consumer products to enterprise software and web applications. This vulnerability is being widely exploited by a growing set of attackers. They said when vulnerabilities are discovered and exploited, it risks a loss or breach of personal information, financial loss, and other irreversible harms the duty to take reasonable steps to mitigate known software vulnerabilities, implicates laws, including among others, the federal trade commission act and the Graham leach Bliley act.
Steve Gibson (00:23:54):
It is crucial that companies and their vendors relying on log for Jay act now in order to reduce the likelihood of harm consumers and to avoid FTC legal action. And they said, according to the complaint in Equifax, a failure to patch, a known vulnerability irreversibly expose the personal information of 147 million consumers. Equifax agreed to pay 700 million to settle actions by the federal trade commission, the consumer financial protection bureau, and all 50 states. The FTC intends to use it's full legal authority to pursue companies that fail to take reasonable steps, to protect consumer data from exposure as a result of log for J or similar known vulnerabilities in the future. Huh. So, yikes. That's a newly aggressive tone from the government side that sort of feels like is getting a little tired of, of having companies say, well, it's not our fault. We you know <laugh> we had to go home for Christmas.
Steve Gibson (00:25:25):
You know, Christmas happens the FTC added an interesting acknowledgement perhaps in response to anyone wanting to hold the log for Jay authors accountable, which you can imagine would be what some pencil neck C suite guy would say, Hey, it's not our fault. It's their software. So the FTC closed their blog posting by writing the log for J vulnerability is part of a broader set of structural issues. It is one of thousands of unheralded, but critically important open source services that are used across a near innumerable variety of internet companies. These projects are often created and maintained by volunteers who don't always have adequate resources and personnel for incident response and proactive maintenance, even as their pro are critical to the internet economy. I thought this was really interesting that this was in this. Otherwise <laugh> a very aggressive posting. They finished this overall dynamic is something the FTC will consider as we work to address the root issues that endanger user security. In other words, it sounds like they're saying, look, you know, we recognize that this is, you know, a thankless job that volunteers are doing for the benefit of all, and yeah, they make mistakes, but we're not gonna hold them respond responsible. We're gonna, you know, when, when vulnerabilities are disclosed and widely publicized, and you're told that you can't go home for Christmas if you do that anyway and consumers are harmed you know, you're not gonna be able to blame the author of the software. So, wow.
Steve Gibson (00:27:29):
In browser news, Chrome fixed 37 known problems last week. I'll note in passing that last Wednesday, Chrome received its first update of 2022 which moved Chrome to 97 0 4 6 9 2 7 1. The update did not fix refreshingly any disclosed zero day vulnerabilities, far as we know there weren't any, but it did address 37 security related. One of which is rated critical in severity and could be exploited to pass arbitrary code and gain control over a victim system. So that batty is another of the apparently ubiquitous used after free bugs. This one having resided Rome's storage component, if exploited, it could have had devastating effects ranging from corruption of valid data to the execution of malicious code on a compromised machine. So it's a good thing that Chrome auto updates everybody's as fixed. You know, I checked mine cuz mine micro Chrome as with that we know is famously sluggish in, in updating itself.
Steve Gibson (00:28:49):
But I was happy to see that I was also at dot 71, so good. 24 out of the total of 37 flaws were reported to Google by external researchers and they considered their project zero initiative to be external, I guess, to the chromium project itself. Cuz of course, as we know, project zero looks at everything does and has helped lots of other Nongo even Google competing projects. The other lucky 17 flaws were flagged as part of Google's own continuous internal security work of the 24 externally reported bugs, 10 were rated high severity, 10 were given medium rating and the rest were low.
Steve Gibson (00:29:37):
Oh and the privacy first brave browser I thought it was interesting following up on last week's discussion of duck, duck goes continuing dramatic, exponential growth. I wanted to also note that the brave browsers 2021 usage more than doubled from its previous year, brave began 2021 with 24.1 million users, those Mo monthly million users and ended the year with 50.2 million for a 220% growth during 2021 up 2.2% or 2.2 times. And this growth is also exponential since brave has been more than doubling their user base year after year now for the past five years. And for those who haven't been following the brave alternative closely it's also based upon the now quite common chromium platform and thus offers nearly all the features available in the other chromium browsers, including CHRO and edge, but brave separates itself from them by explicitly not tracking searches or sharing any personal or identifying data with third party companies like Google or Microsoft in addition to its monthly to its monthly active users, which is what I just quoted jumping from. Well now to above 50 million brave is also seeing 15 and a half million active users daily and its mobile browser has received more than 10 million downloads. So anyway, it's doing great. And I know Leo, I've heard you talking about brave. I don't know.
Leo Laporte (00:31:34):
They were an advertiser for a while. Yeah, yeah. The only, the only thing I don't like about brave is their their, this kind of tenuous attach meant to crypto its own crypto currency. And I always worry about that these days, you know, you saw probably Norton 360 now installs a crypto, oh my crypto minor. You have an option not to, I guess, but still it's weird. And then a Vera which they bought, which is a free antivirus that was very popular. Also is now doing that. So I get nervous people get in the crypto sphere. Like
Steve Gibson (00:32:06):
I don't,
Leo Laporte (00:32:06):
You know, I don't know I don't know, but I like brave a lot if you want to use the, the, the reason unless bullish on brave is everybody now makes a a chromium variant, you know, that besides edge duck, duck goes will be chromium. When they do their browser, that's gonna be one of interest. I think brave is great cuz it's very privacy forward. I mean, I like brave. I just, I still use Firefox weirdly enough.
Steve Gibson (00:32:31):
I do too. It's where all my tabs are that I open when I'm, when I'm pulling the show together. Yeah. Wordpress, as I mentioned, had a, you know, we ought take a break here. We're at half an hour in and we're at about the right place in the show notes and I have a big bunch at the end. So we'll sort of, you
Leo Laporte (00:32:48):
Know load up here in the beginning, lo let's load up with the commercial goodness of Barracuda, ladies and gentlemen, our fine sponsor for this. You don't ha if you listen to this show, I don't have to tell you this statistic every 11 seconds, there is a new ransomware attack. I don't know if it's going up or down. I mean, we've had, we've started to make a little progress in arresting these people, but I don't think it's going away. And it does take such a toll on, on any organization that gets hit by it, especially if it's an infrastructure company like the the colonial oil pipeline. In fact, that's, I think one of the reasons the us government now classifies ransomware as terrorism. I mean, it can really devastate a country according to Verizon's 20, 21 data breach investigations report. Oh, here's the answer to that question.
Leo Laporte (00:33:40):
Ransomware is more than doubled year over year. Okay. and it's most if you don't read this, by the way you should, B Barco has a blog. The threat spotlight research blog is fantastic in their most recent, they identified and analyzed 121 incidents from August, 2020 through July, 2021, seeing a 64% increase in tax year over year. I bet you the 2022 report which of course will be at a few months is gonna show at even greater increase oil pipelines. Not yet universities, city, governments, corporations costing millions of dollars. Barracuda wants to put out the word, you see it right here. Don't pay the ransom. <Laugh> don't pay the ransom. That's easy to say. Once you get bit, you may be very well tempted. So the, the key is protect yourself in your company before a ransomware attack occurs. Part ones, attacks start with an innocent looking email, trying to trick people into revealing critical information, usernames, passwords, maybe click on a link, train your teams to recognize and attack.
Leo Laporte (00:34:50):
And, and you should be deploying anti phishing technology. Step two, secure your web applications. Those are often a back door into your system file sharing services, web forms, eCommerce sites often have weak points, maybe even exploits that hackers can find and take advantage of once they're in your applications. They go after your business data, protect your applications. So they can't get into your network. Step three, we say this over and over, back up your data today's backup. So eSolutions make it simple and fast to protect archives and backup or restore an entire server or just an individual file. There's lots of benefits. Honestly, I think as much data loss occurs from human error. As from ransomware, you, you will wanna be able to recover that data and not pay the ransom. Don't pay the ransom. <Laugh> Barracuda says don't pay the ransom, build your ransomware protection plan. Now, before they strike, help is out there. Go to barracuda.com/security now for more. And of course they make some great stuff that will help you. Barracuda.Com/Security. Now build your ransomware protection plan now with help from Barracuda. Okay, Steve, back to you. So,
Steve Gibson (00:36:09):
As I was saying of WordPress, excuse me since so much of the web is action, just styled, WordPress PHP. I thought it was worth noting that the WordPress core code itself has just received an update that might be important well is depending upon your configuration, as we all know by far WordPress's biggest security headaches arise, because WordPress is by design a user extensible platform, and those who are extending it don't necessarily need to be highly skilled in PHP, coding or security before offering well-intentioned though horribly insecure addons, many of which go on to become I'm highly popular before someone who is highly skilled in PHP and security finally gets around to taking a look at what everyone is using. And then immediately sounds the alarm. Consequently, this podcast is routinely passing along the news that this or that highly used WordPress add on needs to be up updated with the result with the result of professional oversight, which it finally received, but not today.
Steve Gibson (00:37:28):
Today, WordPress itself is in need of some tender, loving care. Yesterday's just released version 5.8 0.3 is not ultra critical, but it's probably worth getting around to, for anyone who's not using. Wordpress's automatic updating mechanisms, which for the couple years that I was using WordPress, I certainly had turned on being a believer in the need for that. And it saved me a couple times the update to this 5.8 0.3 eliminates four vulnerabilities, three rated as highly important there's CVE 2022 21 66 1, which is a high severity SQL injection via w P query it's exploitable via plugin and themes that use WP query. It can and should be applied to versions all the way back to 3.7 point 37. So that problem's been around for quite a while. We've got the CVE ending in 21, 662, also high severity also with a CVSs of 8.0.
Steve Gibson (00:38:45):
So not to be taken lightly that one's across site scripting vulnerability, allowing authors, which is to say lower privileged users to at a malicious back door. <Laugh> this is not good, or take over a site by abusing post slugs. The fix also covers WordPress versions all the way back to 3.7 point 37. The next one is CVE 21, 6 64. That's the third high severity flaw. Although that CVSs is down to 7.4, still ought to get your attention. It's the second SQL injection this time via WP meta query core class, and doesn't go back quite as far. So it was introduced in 4.1 0.34. And then lastly, the 21 6 63 is a medium severity down with a CVSs of 6.6, an object injection issue that can only be exploited if an attacker has compromised the admin account, so not bad, but you know, the, you get to fix that one when you're fixing all three high severity problems.
Steve Gibson (00:39:58):
So there have been no reports of any of these ever being seen exploited in the wild. But WordPress being PHP means that anyone who's inquisitive will be able to quickly determine what the flaws have long been because you just do a on the pre pre-release PHP and the post-release PSP PHP, and you see what they changed. So you know, they could be used in attack by somebody so inclined. So again, while not super critical definitely worth doing and of course CVS says with an eight should not be left in place if given a choice. Okay, Leo, what exactly is a Platon <laugh> we asked this on Wednesday on the, what discussion I had. I had you guys running in the background while I was working on, on spin, right? Platon. Yeah. Is Microsoft's wonderfully named CPU, integrated TPM technology.
Steve Gibson (00:41:13):
Now the press is deeply confused and you guys had every right to be confused about what exactly Platon is. Thanks to Microsoft's own original horribly titled announcement of Platon. Back on November 17th, 2020, the announcement's title was meet the Microsoft Pluton processor, the security chip designed for the future of windows PCs. That's great, but only after making these significant that what Pluton is, is specifically not a security chip <laugh> it's got nothing to do. There's no chip security chips. Okay. Now, and that's Pluto's entire point Pluton and yes, I do love saying the word is M Silicon design for an on chip on CPU, integrated TPM equivalent technology, Microsoft designed the spec and the Silicon, and has arranged for Intel AMD and Qualcomm to integrate this core technology directly into their cores. So the problem with any external physically separate trusted platform module is specifically that it's external and physically separate.
Steve Gibson (00:42:53):
That me means that it's it's lines of communication between it and the systems processors is physically accessible on the motherboards signal traces. Now, everyone has always known that, right? I mean, the problem is TPMS were never to protect against physical attacks. The idea was that a TPM would be a much better place to store encryption keys than either in firmware, somewhere or on the disc where they could be, be retrieved by malware. The TPM was designed as a secure enclave. Subproces where the secret keys could be used without them ever being disclosed. You'd you'd give the TPM a hash of some blob that needed signing. And the TPM would use one of its internal private keys to encrypt the hash without ever exposing any of its keys to the outside world, but other applications for which the TPM was also used were less secure. And securable for example, when TPM is used to hold BitLocker keys, the unlocked BitLock key must eventually become external to the TPM in order for the system to use it to decrypt the drive while it's in use.
Steve Gibson (00:44:31):
Of course, Microsoft makes the Xbox, and they've been annoyed through the years by having their precious Xboxs security subverted over and over and over by hobbyist owner hackers, who Leo had the, to think that they actually had the right to mess with the hardware that they purchased and owned. Imagine that can't have any of that. So those days are numbered. Platon moves the TPM on chip and in doing so, it elevates the security provided by the TPM to also include total protection from physical attack. There will be nothing to attack. Basically what this means is that our next generation processors from everybody, Intel AMD Qualcomm, they will just have that TPM stuff on chip built in not exposed. And so, for example, in the case of BitLock the BitLock keys being used to decrypt the drive on the fly, they will never lose. They will never leave the Silicon.
Steve Gibson (00:45:49):
They will, they will never be exposed. So, you know, it definitely increases security. Unfortunately it definitely decreases our ability to, you know, do things that we like to do with our Xboxes. So anyway, that's Platon. It is, you know again, why <laugh>, why Microsoft could, could announce it as a security chip when that's why they did it was so that it wouldn't be one is beyond me, but then, you know, Microsoft so soft is what we thought, which is a software it's no, it's not, it is Silicon. It is fur. It is firmware that they designed that, that they've convinced Intel AMD and Qualcomm to make some room for on their Silicon dies moving forward. So it, so it's a processor it's like, it's a Microsoft designed security processor that instead of being external, thus exposed on the chip. Okay. And so you can't, you can't get to the communications between it and the other cores on the chip because, you know, they're all on the same chip, you know, you'd have to literally, you know, pop the lid and get really, you know, NSA ish, you know.
Steve Gibson (00:47:09):
Okay. But it's not something that Johnny can do, you know, in, in the garage in order to hack, is that box any longer two quick notes? I am very much enjoying. I need to tell all of the security now listeners who recommended this, the first of Dennis, Taylor's three Baba verse novels. And I'm pretty certain that I'm gonna enjoy the other two as well. It's a trilogy. And I'll probably be wishing for more. Now I do need to provide a caveat there an entirely different style of writing than either Rick brown or Peter Hamilton. Whereas both Rick and Peter are consummate and detailed world builders who spend a great deal of time, carefully crafting their characters, you know, and then placing them into a fully articulated alternate reality, Dennis, by comparison just gets right to it. You know, when you pick up a Peter F. Hamilton novel, you, you know, you have to be in the proper mood and in no hurry to reach the end because the end will not be in sight for quite some time as you and I.
Steve Gibson (00:48:20):
Leo have, I have often commented and similarly, each of Rick Brown's frontiers saga story arcs spans 15 moderate size, I guess what I would call chapter novels. So again, it's all about the journey with those guys, but Dennis Taylor's, Bob verse novels are fast and breezy. They're also a quick read. I just checked and I was surprised to see that I was already 80% through the first one that's before. I started waiting for Mac break quickly to end. Now I'm at 85%. So that's why we do long shows. There you go. <Laugh> good for you. It feels like, you know, to me, like we just got started on this book and it's almost over, you know, on the other hand, Dennis wastes, no time, you know, I love Peter F Hamilton's work. It's definitely right up there among the best science fiction I've ever found, but Peter would still be talking about the shape of the rivets on the hu and, and how the micro ablation created by the thin gases deep, inner stellar space while moving at near light speed would tend to give them more of an oval shape <laugh> and flatten them over time.
Steve Gibson (00:49:41):
Yeah, no, they don't. Bob doesn't care about that. <Laugh> interest. No. And interesting fact toy. Okay. But not crucial to the plot. So although you and I kinda like that stuff, I do love that. Yeah. And I do. And in fact, I'm gonna, I, I just told my nephew who is, who is completely loving Rick brown stuff. He's also in the middle of now I'm blanking on the, the book, the, the one that we love, the, the marsh guy. Oh, oh, oh, the new one project hail Mary. Yes. Project, a loving project. Hail Mary. So I told him about the Bob averse. Andy. We are also like ablated steroids and things like that. <Laugh>. Yes, exactly. So, but I did, I also told Evan that it was gonna be crucial for him to eventually move to Hamilton. He's never read any Peter F. Hamilton. Oh yeah. He's definitely ay,
Leo Laporte (00:50:37):
Fall dragon. We all agree. Start with fallen dragon. Yeah.
Steve Gibson (00:50:40):
I, I said to them, I said, start with fallen dragon, and then Pandora's star follow by Judas. And boy, do you have a <laugh> you know, no hurry. We're not in any hurry, but I, I don't know if, if you're, you're probably as visual as I am Leo, I have those worlds in my head
Leo Laporte (00:51:00):
Now. That's why I like, honestly, I prefer books to TV and movie sci-fi cuz you can imagine something so much rich yes. Than they could ever put on screen. Well,
Steve Gibson (00:51:10):
And, and we've, we've lamented the fact that there's just, I mean, except for the expanse, which I'm waiting for to like, for, to get done so I can cruise through the, the final the final
Leo Laporte (00:51:20):
You like to binge it. You don't watch it a week by week. You you're a binge.
Steve Gibson (00:51:24):
Well, but we used to have like back in the John Luke was flying around like for what was it? Seven years. <Laugh> there's just, there's no good sci-fi now. No, I don't. You know,
Leo Laporte (00:51:35):
Foundation was terrible in invasion was terrible. Yeah. Wheel of time, which is fantasy. Not sci-fi is worse than terrible. I'm so frustrated. Yeah. Yeah. I think I'm gonna stick with the books. In fact, honestly, I still haven't seen the expanse despite your and many other people are recommending it. But I'm, I think I'm gonna do the James essay. Corey novels.
Steve Gibson (00:52:01):
I did first. Yes. Mark Thompson turned me onto them. He told me that the expanse was in production. I read the novels first. It's always the case. Oh my God. Especially the first episode or two of the expanse. You're like a, what the, the hell heck is going on.
Leo Laporte (00:52:19):
It's Stacy says or was it Stacy? No, no. Was Amy Webb on Sunday? Said turn on the subtitles for sure. Cause that spacer lingo it's hard to fall. Yeah, yeah,
Steve Gibson (00:52:28):
Yeah, yeah, yeah. Yeah. The, the good news is I tried to get Lori into Firefly and she like, she looked at it and had the same sort of feeling like its what, except that we're now watching. She never watched castle and I'm a, I'm a Nathan, Nathan, Phil. I love him too. And he's I just think he is so good. And so Firefly
Leo Laporte (00:52:48):
Though was never a book, right? That, that, that was just a TV show. Then later movie. Correct.
Steve Gibson (00:52:53):
And Fox canceled it. Like it was barely, they ruined it. It didn't even reach adolescence and they, they killed it in its crib, but that's to
Leo Laporte (00:53:00):
Me exception, cuz I loved that show. That was a great show.
Steve Gibson (00:53:04):
Well, and it's, what's so fun is that she's now fallen in love with Nathan fill. So after we get through castle that went for like eight years and it's just, well it's good writing. Then I'm gonna be able, she, she will then walk, be able to do Firefly. And then of course serenity the movie that was made from it because fans just demanded more. Yeah. So yeah, they
Leo Laporte (00:53:25):
Wasn't that crowd. I think the movie serenity was crowdfunded at first and then they finally, they said, all right, we'll make it all right.
Steve Gibson (00:53:33):
I think it, and now they raised money to confusing it with the expanse because remember the, the, the, what was crowdfunded was flying a, an airplane around the Amazon headquarters and order for Bezos to finally say, okay, okay, fine. Well, green legs. And he really liked the series too. So he decided to pick it up and, and I have to say the last, the ones that Amazon did had a higher level of production. Oh,
Leo Laporte (00:53:56):
Okay. See, I haven't even gotten that far. I've only watched the first five or six episodes of the first season. It, it
Steve Gibson (00:54:01):
Really is good.
Leo Laporte (00:54:02):
It's I'm gonna do the books and then I'll come back.
Steve Gibson (00:54:05):
Yeah. For what it's worth on the Baba verse, trilogy 88% of the reviewers on Amazon gave it five stars. The other 12% gave it four. Nobody gave it fewer than four. They're available through Kindle unlimited. So if you're a reader and you're a, a Kindle unlimited person, they won't call asked you anything. And again, there it's a different kind of style, but sometimes it's just fun to get on with it. I mean, I've noticed that that television shows where there's a, when a lot happens in an hour, you, you feel like you got something for your time instead of like stretching it out for like no good real, so yeah, yeah, yeah, yeah. Anyway, I am continuing to move forward, nicely with spin. Right. As I have been, I'm focusing upon all of the outlier machines, our various testers have managed to throw at it. And since I'm always working to find a, a, like a generally applicable generic solution rather than doing any special casing so far, I have no special casing code in spin. Right. It's getting generally more robust with each success because it'll be able to like take things in stride that it's never seen before, which are also you know, weirdos. So okay. On that note, let's take our last break and then we're gonna plow into URL, parsing vulnerabilities. Oh
Leo Laporte (00:55:33):
Wow. You jam packing this show full of goodness, our show today. <Laugh> I love how he does it. Our show today brought to you by express VP. And we talk about VPNs all the time. I've talked about express VPN, my personal choice for a VPN really important. I can't underscore this enough that you pick the right VPN because otherwise you're just passing along the security and privacy issues you have here with your ISP or your coffee shop to the VPN provider. You gotta try us them. That's why I recommend and use express VPN. So we talk about security. We talk about privacy, but there's another reason a lot of you use express VPN Netflix, or, you know, pick your streaming platform of choice, geographic eliminating geographic restrictions for one of a better phrase, if you're a Netflix and by the way, this is completely legal.
Leo Laporte (00:56:31):
Netflix. I even asked them, they said, well, of course, if you have a Netflix subscription in the us, you can watch content. In other countries. We dis recommend it because most VPNs are too slow to do at HD video. And that's what I love about express VPN. It is not a free VPN. It is not a VPN based on advertising. They charge around seven bucks a month, but there's a good reason why you want that. They put that money back into the infrastructure. So you can watch HD video and express VPN. In fact, it's so fast. You won't know you're using a VPN. So you subscribe to Netflix in your country and you maybe by now you've watched everything on there. I know I have. And you're looking for more well with express VPN, you can choose, they have points of presence. They have servers in 90 different countries.
Leo Laporte (00:57:20):
You could choose any one of those countries. Normally what happens at the express VPN? They've got these great apps, very simple. They're everywhere. Ios, Android, Mac, windows, Linux, you could put 'em on your router. And normally there's a big button. You press that. And it will pick the nearest server to you for the best speed. But you can override that. You could say, no, no, I wanna be in England. And you will emerge in London onto the public internet. And then you'll be able to watch Netflix England. And because again, they put money in the infrastructure. Two benefits to that. If you wanna do geographic restrictions, eliminate 'em speed. Of course. So you can watch HD video. The other thing is they're constantly refreshing their pool of IP addresses. There's a little cat and mouse game. Some provider say, oh, I see you're coming in on a VPN address.
Leo Laporte (00:58:07):
You can't use us well, a good VPN provider. Doesn't reuse the same address over and over again. Express VPN constantly rotating them. So you, it really works with many other streaming services, including B, B, C I player, which is only available in the UK, Netflix in Japan, and in all over the world, express VPN number one, rated VPN by publishers like business insider. Of course I've been telling you about it for years, express vpn.com/security now. So be smart, protect your data, protect your privacy, stop paying full price or streaming services while only get access to a fraction of their content and get the value of streaming services by, by using them all over the world, express vpn.com/security. Now visit 'em right now, get three extra months of service for free bringing the price down below seven bucks a month, which I think is exactly right. It's not too much, but it's also not too little. It's really important. E X P R E S S vpn.com/security. Now get the best at the right price express, vpn.com/security. Now, when you sign up for a year, you get three extra months and that's a very nice discount. All right. I think it's time to talk about the subject of the day.
Steve Gibson (00:59:29):
You are URL parsing <laugh> indeed. And I just sent you a text with the link to the soda stream, refill adapter <laugh>
Leo Laporte (00:59:41):
We were talking before the show about why never, never to buy soda stream cartridges. They're overpriced. Steve has of course, a rub Goldberger venture for making it
Steve Gibson (00:59:53):
Possible for a lot less $17 for the little brass Gidget that allows you to refill your own soda stream cartridges. So it's definitely a win, okay. URL par parsing vulnerabilities. As I mentioned at the top of the show, this week's topic centers around the work of four security researchers, two from sync spelled and I guess all of the normal spellings are gone. So sync spells their name S Y N K <laugh> and, and two from clarity, spelled C L a R O T Y. Okay. What the one? Okay. They're they're both in the Northeast us, as I mentioned, they decided to take a closer look at another set of wildly popular and widely libraries naturally. I mean, URL parsing, come on. Like everything needs to do that. Which as a consequence of that would inherently have broad exposure to external attack. The title of this week's podcast, URL, parsing vulnerabilities, discloses their wisely, chosen in retrospect research, target, and suggests what they did indeed find.
Steve Gibson (01:01:10):
I have a, a link in the show notes to their 15 page PDF or anyone who wants to dig in deeper than I do, although we're gonna be digging in play deep. What they said was to like set the, a stage, the uniform resource locator, the URL is integral to our lives online because we use it for surfing the web accessing files and joining video chats. If you click on a URL or type it into a browser, you're requesting a resource hosted somewhere online as a result, some devices such as our browsers applications and servers must receive our URL, parse it into its uniform resource identifier components. For example, the host name, the path, and so forth and fetch the requested resource. The syntax of URL is complex and although different libraries can parse them accurately, it is plausible for the same URL to be parsed differently by different libraries.
Steve Gibson (01:02:18):
The confusion in URL parsing can cause unexpected behavior in the software like a web application, and could be exploited by threat actors to cause denial of service conditions, information leaks, or possibly conduct remote code execution attacks in TA in team 80 two's joint research with sync, we examined, they wrote 16 URL, parsing libraries written in a variety of programming languages and noticed some inconsistencies, which is putting it mildly as we'll see, they said with how each chooses to parse a given URL into its basic components. We categorize the types of inconsistencies into five categories and searched for problematic code flows in web applications and open source libraries that exposed indeed a number of vulnerabilities. We, we learned that most of the eight vulnerabilities we found, and by the way, they all have CVEs assigned. I mean, these are real problems. Largely occurred for two reasons.
Steve Gibson (01:03:32):
First, multiple parsers in use. They said whether by design or an oversight developers sometimes use more than one URL parsing library in projects because some libraries may parse the same URL differently. Vulnerabilities can be introduced into code. The second specification incompatibility, they said different paring libraries are written according to different RFCs or URL specifications, which creates inconsistencies by design. This also leads to vulnerabilities because developers may not be familiar with the differences between URL specifications and their, or implications. For example, what should be checked or sanitized. I thought that the first case the probably inadvertent use of different parsers was really interesting where developers might make the reasonable, but ultimately incorrect assumption that different areas of their code would decompose input URLs the same way. And I just, I invented a typical instance of how that could go wrong. It's not one that we'll be talking about in a second, but for example, imagine that upon decomposing a URL into it, areas pieces, those pieces were sized and storage was allocated to fit, but the code wasn't yet ready to fill those buffers.
Steve Gibson (01:05:11):
Then later, when the code was ready, the same URL was again, parsed with the URL's component data. Finally being copied into the previously allocated storage. The programmer could assume that since the same URL was being PO pared, both initially and later, the component pieces would naturally be the same size. But if different URL parser libraries were used and they interpreted the URL's format in slightly different ways, the allocation might not fit its data and a buffer overrun might occur. So for example, their second issue, you, which they turned specification in compatibility is a variation of a fundamental programming challenge that I've spoken of from time to time. And also recently my term for it is weak definitions. I, if a coder is not absolutely certain what something is, for example, a variable represented by a name that coder or God help us some future other coder might come along and use that variable differently because its purpose wasn't made Absolut clear and obvious by its name.
Steve Gibson (01:06:40):
You misname something you're gonna, you're gonna come back later and forget that you like at while you were coding, you ended up re you know, like using it differently than you originally thought you were going to because of the name you gave it, which is no longer correct. So, and I, I find myself often going back and like fixing names of things when I go, Ooh, right? That's not, that's not really what it's doing any longer. I better fix that now. So you know, and in fact, we have another example of the URL parsing duality dilemma, right? In our own backyard with log for J during our final podcast of 2021, we talked about how the log for J trouble was that a URL of the form, J N D I colon, and then using L D as the scheme. So L D P colon slash slash, and then for example, evil host.com/a was being parsed from within a log message log for J upon seeing that URL would dutifully run out onto the internet to fetch whatever from wherever, so easy to solve this problem.
Steve Gibson (01:07:58):
Right just create an, an access white list of allowable hosts for that J N D I URL lookup and default the white list to only containing a single entry for local host, which was probably the only valid source for J N D I material to come from anyway. Right? Problem solved. Nope, no, not, Nope, Nope. Not, not long. And that was the first, that was the first fix that was offered to this problem. Not after that first X was added, a bypass was found and it was even awarded a CVE number, right? 45,046, which once again, allowed remote J N D I lookup and allowed the vulnerability to be exploited in order to achieve remote code execution. So how was the clean and valid host targets? Whitelist bypass. Yeah. Oh, the new hack to bypass the whitelist used a URL of the following form and this actually worked, it used LDA colon slash slash 1 27 0 0 1 local host.
Steve Gibson (01:09:14):
Yeah. Local host pound sign. Oh, evil host.com. Colon 1, 3 89 slash a, believe it or not tucked inside the log four J code are two different URL. Parsers. I kid you not one. Parser is only used for validating the URL. Whereas another is used for fetching it in order to validate that the URL's host was allowed. Java is built. Inri class is used. The R Java is built in class parsed the URL extracted the URL's host 1 27 0 1 and checked it. The host is inside the whitelisted set of allowed hosts. And indeed, if you parse the URL, yeah, fine. Yeah, no, no problem. You take it from here. Right? However, it was discovered that when the J N D I lookup process actually goes to fetch this URL, it does not fetch it from 1 27 0 1. Instead it parses URLs differently. It makes a request to 1 27 0 1 sign dot evil host.com.
Steve Gibson (01:10:41):
In other words, the sub domain of evil host.com again, 1 27, 0 0 1 pound sign dot evil host.com, which is exactly what they bad guys figured out they could do. So after being initially shut down by the update, which added the white list, because after all, we wouldn't wanna simply remove some dangerous and completely unneed functionality from log for J oh, heavens no. Yeah. Uhhuh the bad guys, simply tweaked their evil host.com server to reply to sub domain queries. And they were back and hacking. And as we know that dangerous and completely unneed functionality was finally disabled by default after, or what the fifth try at fixing the log for J vulnerability. Okay. So what's relevant for us today is that this just actually happened in the very real world. That is this log for J thing that when we just saw a URL, pulsing, a parsing being on differently in two different places actually causing a real world problem.
Steve Gibson (01:11:59):
Okay. So what did the, this new team turn up when they really dug into this? They said throughout our research, we examined 16 URL, parsing libraries, including URL, a Python library, URL library three also Python RFC, 39 86, which is the name of a Python RFC par a URL parsing library, HTTP tools in Python curl li in C URL w get the Chrome browser itself, I, which is a.net library URL in caps, which is a Java library. I, a Java library, parse underscore URL, which is a PHP library, lowercase U URL, which is a no JS library URL, hyphen parse also no JS net slash URL, which is written in go, I lowercase in Ruby and I uppercase for Pearl. So yeah, <laugh>, as I said, URLs are everyone air, and there are 60 different parsing libraries. No two of them do the same thing.
Steve Gibson (01:13:22):
Despite the fact that they're all trying to do the same thing. They said, we found five categories of inconsistencies, scheme, confusion, slashes confusion, back slash confus, which is different from Slash's confusion, URL, encoded data, confusion, and scheme mix up. They said we were able to translate these inconsistencies into five classes of vulnerabilities, server side request, forgery, cross site scripting, open redirect filter, bypass, and denial of service. In some cases, these vulnerabilities could be exploited further to achieve a greater impact, including remote code execution. And they finished eventually based on our research and the code patterns we searched, we discovered eight vulnerabilities in existing web applications. And third party libraries written in different languages used by many popular web applications. Okay. All eight of those have been assigned as, as I said, CVEs because as we'll see, they're really not good after digging through all of those libraries and the applications that use them.
Steve Gibson (01:14:40):
They found, as I mentioned earlier, five different situations where most as they put it of the URL, parsers behave unexpectedly, and that's the confusion slash confusion back slash confusion URL and coded data confusion and scheme mix up when we're not sure what we want or where we're going. It's often difficult to create a specification for that mission, which is fuzzy beforehand. And probably nowhere has this proven to be more true than for the exacting definition of the format of the URL, the trail <laugh> of obste and abandoned and URL. Rfcs, you know, the formal specifications of things speaks volumes. The original URL RFC was 1738, and it was updated by 18 0 6 23 68, 23, 96, 39, 86, 61 96, 62, 70 and 80, 89. And along the way, it was obsolete by 42 48 and 42 66. Then you have the RFC for the more generic, I, it also updates the original 38 obsoletes 27 32, 23 96 and 1808. And is then itself updated by 68, 74, 73, 20 and 88 20.
Steve Gibson (01:16:27):
So imagine being a coder <laugh> who's, who's trying to decide how to handle every possible curve that somebody might either accidentally or maliciously toss down the throat of your URL interpreter. And as if that all weren't enough, there's also the, what w G which is w H a T w G and there TWA <laugh>, which is T w S what WG that is w H a T w G is the web hypertext application technology working group. What WG a community founded by well-meaning individuals. I'm sure from leading and technology companies who have tried to create an updated true to form URL, specification and URL parsing primitive, because you know, the final RFC, eh, we're not, we dunno this resulted in the TWA. <Laugh> the what? The, the, what w G URL specification, T w S while it's not very different from the most up to date URL RFC, which we, we left off at 39, 86 minor differences do exist.
Steve Gibson (01:17:58):
For example, while the RFC differentiates between back slashes and forward slashes, where forward slashes are treated as a dilemma inside a path component, and back slashes are a character with no reserved purpose. What WGS specification states that back slashes should be converted to slashes, and then be treated the same as what WG these rationale is that this is what most popular web browsers do. Browsers. It turns out treat forward and back slashes identically. And we'll see later that the, that they do this on purpose. So what WG feels that what they regard as their so-called living URL standard should correspond on with common practice, rather than being some stodgy old numbered document that, you know, isn't what people are doing anyway. But this living URL standard broke compatibility with some existing standards. As we know, and with the contemporary URL, parsing libraries that followed, it turns out these operability issues remain.
Steve Gibson (01:19:12):
One of the primary reasons why many maintainers of some parsing libraries have just said, okay, wait, we're sticking with the RFC. That being 39, 86, even though they don't do that correctly, either at least their intention was in the right place. So this brings us to scheme confusion, a confusion involving URLs with missing or malformed schemes of this. The team wrote, we noticed how almost any URL parser is confused when the scheme component is omitted that's because RFC 39, 86 clearly determines that the only mandatory part of the URL is the scheme, but you have to have that. Whereas previous RFC releases that is to say RFC 2396 and earlier don't specify it. Therefore, when it's not present, most parsers get confused. And the real world behavior they show, this is me talking is unsurprising and worrisome. The, they ask these guys, the researchers asked five different popular Python libraries to parse the schemeless input, just google.com/abc.
Steve Gibson (01:20:48):
Where most, oh, I'm sorry. Sorry. I lost my place. Most of the parsers when given the input, google.com/abc state, that the host is empty, like right. The host being.com the most of the parsers say you've got no host while the path they have as google.com/abc, which is wrong. Obviously, however, URL live three correctly states that the host is Google and the path is slash ABC while HTTP tools complains that the supplied URL is invalid. Okay. Because it's really adhering to the spec, right? And if you don't have a scheme, RFC 39, 86 says you're not good anywhere when supplied with a schemeless URL, almost no URL parses the URL correctly because the URL does not follow the RFC specs, but most don't complain. They just guess <laugh>. And most of them guess differently. C URL's parser dealt with a missing scheme by providing its own guessing and what was not provided it got the right result, but should it have guessed?
Steve Gibson (01:22:14):
Could there be, you know, an abusable downside to such guessing one might ask in their report, they then provide a sample bit of Python code to show a real world example of how a security bypass might occur as a direct result of these parsing differences. And, and when I, when I first encountered that, I thought, okay, they've constructed an example, synthetic of like how this would happen. And they use URL split it, which is a function imported from the URL dot parse library in order to do the splitting. And then later they use where is it? Net lo in, in the, the parsed URL library in order to perform the fetch and exactly the problem that we were talking about occurs because in this block of code, different URL, pars are being used. I learned later that this is actual Python code in a highly used library, which is it, it is handling these malformed URLs exactly in this wrong way.
Steve Gibson (01:23:45):
And it is used everywhere. It's unbelievable. Pool manager is the function in URL lab three, which is invoked. And that's, that's like what everybody uses to, to, to put, pull queries across the web. Okay. So there's that another audit they found was in the handling irregular number of slashes. Oh, you're gonna love this one, Leo. They called it slash confusion. Now this is different than which way the slash is leaning. Oh, okay. They, but we get to that next <laugh> that's the back slash confusion slash confusion. I know it's unbeliev, but how is this? Does this, any of this actually work the controlling RFC 39, 86 states that a URL authority. Okay. Now the, the, the authority is the technical term for the domain or the host. What we all call the domain name or the host in the URL, the actual RFC calls it, the authority.
Steve Gibson (01:24:48):
It states that the authority should start after the scheme separated by a colon and two forward slashes. Yeah. Right? Yeah. HTD P colon slash slash. Yeah. How many times have I said that on the podcast? Yeah, it should persist. That is the parsing of the authority should persist until either the parser reaches the end of a line or a dilemma is red. These limiters being either a slash signaling the start of a path component, a question mark signaling the start of a query or hashtag signaling the start of a fragment. So they played around with URLs, beginning with a scheme, a colon and three or more slashes follow bio domain name and path. Apparently the pattern matching that were being used, found the colon and thought, aha, here comes the domain name. And when they immediately hit the third slash they thought, ah, and there's the end of the domain name? Oh my God. <Laugh> yes. Oh yeah.
Leo Laporte (01:26:10):
So, so is it always, do they use, are they using regular expressions to do this? Yeah.
Steve Gibson (01:26:16):
Yeah. And in fact if you scroll down in the show notes at the top of page 13, you'll see the, you'll see the, the Redex, which is that doing this cause
Leo Laporte (01:26:28):
Redex is notoriously. I know difficult. You easy to screw up
Steve Gibson (01:26:32):
And this is, it is yes, it is super powerful. Yeah. And so easy to have side effects that you don't. I anticipate
Leo Laporte (01:26:40):
Because the advent of code uses Redex a lot. I've been writing a lot of REDX lady. I love Redex. And there's a, there's a Jeffrey Frito's book on mastering. Regular expressions is one of my favorite coding books of all time
Steve Gibson (01:26:54):
And Boyle. Can you get yourself some, some re I mean it, it like fourth is a right only language. Yeah. Yeah.
Leo Laporte (01:27:03):
Sometimes they call it the problem with the toothpicks or yeah, it was just CRA it gets crazy with all the escaping in the back. Cuz that's part of the problem is back slash is often used to escape. And so sometimes you'll have back slash back slash back
Steve Gibson (01:27:19):
Slash <laugh>
Leo Laporte (01:27:19):
To escape a back slash it gets kind of nutty. Yeah.
Steve Gibson (01:27:23):
In fact, you, there
Leo Laporte (01:27:24):
Are more modern parsing libraries than Redex.
Steve Gibson (01:27:30):
Oh Leo. Nobody should be using it. Yeah. You ought to use a careful algorithmic parser in order to take, because I mean, it is a parsec for something. Yeah. It is a forward moving flow w with a, you know, a well defined, struck. Yeah. You know, follow the, the proper, it, it, yeah. Yes, exactly. And, and, and treat it that way. Yeah. And well, you know, nobody does, and you, you know, 60 16 URL parsers, let's write another one. It's the
Leo Laporte (01:27:58):
Age of the, we have, we have, I mean, oh God. And it's also, I know, I think this is in some ways an open source problem because yeah,
Steve Gibson (01:28:07):
Because you don't have to be an expert. Yeah. In order to throw out another URL parser and say here Jimmy's URL. Parser. Yeah.
Leo Laporte (01:28:15):
Yeah. And people, this is also a big problem is people just use libraries and assume they're correct. You should definitely not mix libraries. That's really funny. That's really strange.
Steve Gibson (01:28:28):
Okay. So we have the problem that three slashes in a row causes a null host and the authority then to be moved to the beginning of the path that actually happens, then we have the back slash confusion, a confusion involving URLs containing a back slash RFC 39, 86, the controlling document clearly specifies that a back slash is an entirely different character from a forward slash and should not be interpreted as one. No, this means the URL HT DPS colon slash slash google.com and H E DPS colon slash slash google.com are different. Yes. And should be parsed differently. Yes. And being true to the RFC, most URL parsers do not treat a slash and back slash interchangeably. Well, that's a relax, but our, but our web browsers do, oh, no. Yes. Every web browser, when a URL having back slashes, or even a mixture of backward and forward slashes is used in a URL Chrome and its brethren are completely happy treating either as forward slashes. So
Leo Laporte (01:29:45):
They're assuming maybe that users don't know the difference.
Steve Gibson (01:29:49):
I think that's it. We might think that this wacky behavior occurs because most browsers follow that what WG URL specification, which states that back slashes should be treated the same as forward slashes. But it may be more accurate to say that the TWA spec follows the browsers. Yeah. Rather than the other way around. Yeah. Cuz people
Leo Laporte (01:30:11):
That, for years, in fact, I just saw that TV had the other day where they said instead of slash, they said black slash and just, and nobody caught it. They just read it that way. And I think it's because well, back slashing was created by, I mean, people got used to it cuz of windows horrific
Steve Gibson (01:30:30):
Use of it. Oh my God. And it hasn't that been a, a sin isn't that a sin that is heard. I, you know, whenever I'm like spending a lot of time in, in Unix and then I come back to windows, I'm like, wait a minute. That's it's like, <laugh> what do I use? Oh God. Anyway, the, this, this code at the top of page 13 shows what the guy did on the second line where he's parse, he's using a, a, a Redex to parse out the authority. He's matching on the, after finding the colon forward slash forward slash he then sets up a group in order to grab the authority and he's, he's pulling together and you can see it in marked in red, the top of page 13. I think it's a, it's a little lower than where you are. Okay. Or maybe it's above where you are above. Yeah. Yeah.
Leo Laporte (01:31:22):
All this back slashing is making me
Steve Gibson (01:31:24):
Nuts. You can see two it's. Yeah. Top of page 13. That's this two really? Oh, maybe. Oh, no, I'm sorry. You're you're on their PDF. I'm on my show notes. Oh, that's why. There you go. <Laugh>
Leo Laporte (01:31:36):
Sorry. Okay. I'll find it.
Steve Gibson (01:31:39):
Go ahead. Yeah. Anyway two they, they marked them in red two back slashes in a row, which of course is an escape for a back. Meaning I actually mean one back slash, but it's grouped in there along with a forward slash as, as being a valid Terminator for the authority that is for the domain name. Here we go. Okay. So this means that if an authority contains a back slash URL lab three would split it out at that point and use only what appears before the back slash as the authority then continuating what follows the back slash to the front of the URL's path. Anyway, the bottom line is it's, it's exactly what we were talking about. This problem that occurred in in log for J. So for example, and here's where our listers need to visualize. If you had HTD P colon slash slash evil.com/at sign, google.com/if the latest RFC is Abey as most parsers, do, which specifies that back slash has no special meaning inside a URL authority, the malformed evil.com URL would be parsed as evil.com/at sign.
Steve Gibson (01:33:08):
Now re remember the old and now deprecated URL, embedded username and password syntax. Remember you used to actually be able to put a username and password in the URL. Another bad idea. <Laugh> oh my God. Really bad idea. Oh my God. Oh, what were they thinking? Anyway? They, they, they first, they, they, they, they first, you know, started saying, we really don't think that's a good idea. Then they formally now said, no, that's no longer gonna be considered legal. It should never be, be done, but it's still tolerated because of old URLs out there. Right. But, so that means that everything in front of the side is considered user info as it's termed. So that means that something that doesn't treat back slash specially inside the authority, as the RFC says, you shouldn't will end up parsing that with evil.com/outside as par as user info.
Steve Gibson (01:34:10):
And so the actual domain will start and be seen as google.com. Okay. The researchers tested this and found that yes, indeed. This is what most the RFC compliant parsers do. So this is harmless because it's ignoring evil.com. Correct. They do not treat the ABT slash as the end of the authority, since it precedes the at sign, they treat it as part of the user info, but not URL live three <laugh>, which is heavily used URL live three, as we saw in that regular expression, it it's a it's right. It's right above it's at the top of that, of page 13. Yeah. If you scroll up, you'll see it. The second line in that chart, there are two red back slashes there that that's in there as the Terminator for the authority that is that it and a forward slash either of those. So they did it on purpose.
Steve Gibson (01:35:14):
Oh, wow. Yep. You could see how easy this would be though. If you look at this regular expression to make a mistake. Yeah. I mean, yeah. And, and so, okay. It's in there, its result will not be the same. And here it is Leo, since the requests PI on module, that's where that earlier snippet of code came from Uhhuh, a heavily used Python module requests uses URL live three as its primary parser while still using URL lives. Don't URL, parse, and URL split for other purposes. Yes. It mixes them. So we can easily run a foul of the differential parsing scenario we described earlier. And as I said, I thought when I first thought it was a synthetic example, no, it's right out of the Python code, where it comes up with different answers. Okay. So we've established that a collection of five, what we might call exploitation primitives exists. It should be clear that when parsing the same data, all URL parsers should be deterministic and should return identical results. When that is not done, the parsers introduce a dangerous uncertainty into the process to create a wide, a potentially exploitable vulnerabilities.
Steve Gibson (01:36:43):
They gave us a bunch. I'll just describe one. It's a very popular product called or package called clearance for Ruby as a direct consequence of these parsing mistakes. The researchers discovered a ju and exploitable open redirect vulnerability in the Ruby gem package known as clearance. And it was assigned to CVE 23,435, actually 20 21, 20 3004 35 open direct, open redirect vulnerabilities, enabled powerful fishing. And man in the middle attacks by secretly redirecting a user's browser to fraudulent sites. The vulnerabilities occur when a web application accepts a user controlled input that specifies a URL that the user will be redirected to after a certain action such as a successful login or logout occurs in order to protect users from an open redirect attack, web servers carefully validate the given URL and allow only URLs that belong to the same site or to a list of trusted redirection targets to be used.
Steve Gibson (01:38:03):
So you can probably see where this is going, right? If you can't trust the thing, that's parsing your, your verification, we just saw where a white list, what could be broken. Then you are in trouble to make a long story short. What this thing allows is a bad guy to use these PO these parsing vulnerabilities that are, that are present in the clearance Ruby gem package to perform man in the middle successful man in the middle attacks to, to hijack people's sessions and bring them back after logging in to the bad site. Even though that the, the victim site where the user logged in has explicit code to prevent that from happening because the danger is well understood. So th this just ends up being a, a huge problem. In the case, in the case of this clearance package, as I said, it will redirect a user to a logged on page in, in the show notes at the top of page 16, I show their example, which is www dot actually, it's my example, insight.com/slash/slash/ evil.com.
Steve Gibson (01:39:24):
When that ends up getting parsed by the broken parser, which clear which, which the clearance package is using, it ends up giving the browser slash slash evil.com. So what's a bit surprising is that if the user were using Chrome, Chrome would receive the URL slash slash slash evil.com, which hardly seems valid in which we might expect Chrome to B at, but web browsers, as we were getting to talking about, have evolved to be hyper lenient with what they will accept after all users are entering cryptic looking URLs. And aren't perfect. So Chrome's lenient behavior is they consider it a feature, not a bug. And in fact, in the chromium source in a big comment block, it says the syntax rules of the two slashes that proceed the host in a URL are surprisingly complex. They are not required, even if a scheme is included. And then they say, HTTP, colon example, old.com, no slashes is treated as valid, which I never knew.
Steve Gibson (01:40:44):
I'm not gonna bother putting slashes anymore. They're, you know, Chrome ignores 'em and it says, and are valid. Even if a scheme is not included, then they say slash slash example.com is treated as a file as file colon slash slash slash example.com. He says they can even be back slashes what? Yes, HTP colon slash slash example.com and HTTP. Okay. I'm no colon HTTP slash slash example.com. This is Chrome's own notes. This is in a comment block are both valid and there can be any number of them. It actually says that HTTP, colon slash example dot and HTTP colon slash slash slash example.com are all valid. And this is cuz users are gonna type that. And so we just wanna, yes. Yeah. And you can't really blame them for the log for Jay problem. No. That's log for Jay's problem in parsing it's input, correct? Correct.
Steve Gibson (01:41:55):
Cause Chrome's a browser and it's, you know, it's, it's just trying to, it's try to make you want yes, it's exactly. It's gonna try to make sense of what gibberish you have just typed into the URL and go, okay. Let's guess here where they want to go. Yeah. So suffice to say that with all, all this, we have another example of longstanding, deeply embedded, critically broken code, which despite now being identified will remain in use until all references to it are eventually if ever weeded out. We also have another example, which I do did appreciate the fact that the the researchers were able to see what was going on of the power of open source software. The researchers were able to peer into the code to see and understand how it operated and what it does, the fact that they didn't like what they found well, they can fix it or find the guy who can fix it.
Steve Gibson (01:42:59):
The flip side of course, is that malicious actors who have access also, but overall open seems clearly better since when well-meaning researchers are able to offer feedback to bad code, better. That happens, whereas bad guys need to operate with whatever they can find, eh, unless they worm their way into being trusted on a project. You know, that's the one case, otherwise they don't have the ability to make good code bad in the same way that researchers can help to make bad code. Good. So, you know, thus the argument for letting lots of people look at it, and it's just gonna kind of float to the surface and, and be good on all, all on its own. But anyway, URL, pulse parsing vulnerabilities exist, and they're
Leo Laporte (01:43:52):
All around. It's amazing. Just amazing. Yeah. Wow. And is, is this, this is the root cause of the log for Jay problem is just this inability to recognize malformed.
Steve Gibson (01:44:03):
No, actually this, this was this intersected log, the root cause of log for Jay is that you insane Lee processed a URL right. In a, in a log output. It's
Leo Laporte (01:44:15):
Like what? That you're right. That's a mistake by itself. <Laugh> yeah, yeah, yeah,
Steve Gibson (01:44:19):
Yeah. And, and so what happened was the first fix was to do a white list on the, on the domain and that didn't work. Yeah. And that didn't because of the parsing, the URL parsing vulnerability.
Leo Laporte (01:44:30):
Wow. I bet it's turtles all the way down. I mean, I bet I honestly, you solve that and then you're gonna find another one, another one, another one, another one. Yep.
Steve Gibson (01:44:38):
Yep. As we've said, security is porous, the harder you look, the more you find.
Leo Laporte (01:44:43):
Yeah. That's amazing. What an interesting topic. I hope everybody subscribes to this show so they can hear this. Obviously you're listening. Thank you. Grc.Com is the place to go for Steve's website. That's where spin, right? The world's best mass storage, recovery and maintenance utility lives. 6.0 is the current version 6.1 is imminent. If you buy six, oh, now you'll get six one for free. You can also participate in the development of 6.1. Steve also has the show there, the 16 kilo audio versions, as well as the 64 kilobit audio. He's got the show notes, as we mentioned he also has transcripts a couple of days after the show. We'll have transcripts, so you can written by an actual human, so you can actually follow along or search for the topic you're interested in, et cetera, et cetera. This is a show I think people will share with one another just cuz just that last part alone is really, really interesting.
Leo Laporte (01:45:43):
We have 64 kilo audio and video at our site, twi.tv/sn. You can always download any show. There, there are 853 to choose from. This is the 853rd. There's a YouTube channel with all the shows dedicated to security now. And of course subscribing is probably the best thing to do. Get it automatically the minute it's available. And if your podcast player supports reviews, please tell the world how great security now is. Leave us a five star review so everybody can discover this show cuz they don't wanna miss this. This is good stuff, Steve, if you wanna watch us do it live, it's a little tricky because Mac break weekly is, is an accordion and can expand or contract completely at random. But nominally, we do this show 1:30 PM Pacific four 30 Eastern of a afternoon. That's 2130 UTC and the live streams, audio and video@livedottwi.tv.
Leo Laporte (01:46:40):
My suggestion is just have it on all day. Tuesday, start in the morning at 9:00 AM with Pacific iOS today, then Mac break weekly 11 security. Now whenever we get around to it and all about Android after this. So, you know, it's a big, Tuesday's our biggest day. I think lots of good content all day long. So just have TWI on live all the time. That's my advice to you. There's a way you can support us. Of course, we're ad supported everything. You know, all our podcasts are supported by ads and the IRC and so forth, but we have a paid tier as well. If you'd like to contribute, it really helps us a lot. Financially with the vicissitudes, the ups and downs of advertising seven bucks a month, what do you get? Well, I think it's a fair price for free versions of this show and all the other shows, including video or audio, your choice you also get the great discord channel, which is so much fun.
Leo Laporte (01:47:37):
Our server runs all the time as all sorts of topics from coding to motor sports. And of course every show has its own channel in there. Again and everybody in there's a club member. There's also the TWI plus feed with shows that we don't put out as podcasts stuff that comes before and after each show. But we also are doing more and more special shows for instance Stacy Higginbotham's book club, she'll be doing autonomous by NLA Newtz that's coming up this week, Annie Ann ACOs gonna do an ask me anything, Steve. I hope you'll get a, we'll get a vitamin D thing out of you. You did. You did the first ask me anything some time ago. Yeah. There's the untitled Linux show every Saturday there's GIZ fizz before that. There's just lots of stuff. And we're looking at a new show that we're gonna add.
Leo Laporte (01:48:25):
I think this is gonna be our method for adding new shows in the future is put 'em on club TWI for first cuz no new show gets advertising. So if it's supported by TWI club, TWI members, we can do that. So we'll put it on club TWI first and then if it builds an audience and we can sell advertising, then we'll put it on the main feed. And I think we've got a show coming pretty soon. That's gonna follow that model. So if you wanna know more twi.tv/club TWI, twi.tv/club to it, there's individual memberships, corporate memberships too. A lot, a number of companies are doing that now for their employees. That's a nice benefit. Thank you. Appreciate you doing that. All right, Steve I am off to read the expanse <laugh> and to recharge your soda stream and oh yeah, yeah. I got some questions about that. Well, we'll talk about that off the air. Thank you, Steve. Have a great week. Okay buddy, Jo
Speaker 3 (01:49:16):
Android is constantly evolving and if you are part of the Android faithful, then you'll be just as excited about it as I am. I'm Jason Howell host of all about Android, along with my co-hosts Florence ion and Ron Richards, where every week we cover the news, we the hardware and we cover the apps that are driving the Android ecosystem. Plus we invite people who are writing about Android, talking about Android and making Android onto the show every tuesday@twi.tv. Look for all about Android
Speaker 4 (01:49:48):
Security. Now
Speaker 3 (01:49:53):
<Silence>.