Security Now 950 Transcript
Please be advised this transcript is AI-generated and may not be word for word. Time codes refer to the approximate times in the ad-supported version of the show.
Ant Pruitt (00:00:00):
Hey, it is time for security. Now I am Matt Pru. I'm not Leo Laport. He is out and about having some interesting birthday celebrations. We'll leave it at that and I'm joined this week by Mr. Security, Steve Gibson himself, and today we're going to talk about what's going on with Crush FTP, the Enterprise FTP package. There's also some interesting stuff going on with the fingerprint scanners and biometrics on your laptops and devices that are out there. Are they really secure? Some think that they are, maybe they're not. But also there's some big news happening again with all of these credit agencies out there. TransUnion and Experian hack yet again. Good grief. All of that more is coming up here on security. Now y'all stay tuned.
TWiT (00:00:53):
Podcasts you love from people you trust, this is twit twi.
Ant Pruitt (00:01:04):
This is Security Now episode 950. Recorded Tuesday, November 28th, 2023. LEO turns 67.
(00:01:15):
It is episode of Security Now is brought to you by Palo Alto Networks. Their zero trust for OT Security Solutions can help your business achieve 351% ROI over five years. To learn more, find the link in the show description or visit palo alto networks.com and by Melissa, the global leader in contact data quality. Bad data is bad business. Make sure your customer contact data is up to date. It started today with 1000 records clean for free at melissa.com/twit and by our friends at IT pro tv now called aci. Learning acis new cyber skills is training. That's for everyone, not just the pros. Visit go dot ACI learning.com/twit twit listeners can receive up to 65% off an IT Pro enterprise solution plan after completing their form. Based on your team size, you'll receive a properly quoted discount tailored to your needs. Hey, what's going on everybody?
(00:02:16):
I am Matt Pruitt and this is Security Now here on twit tv. Yes, I said I am Aunt Pruitt. No, I am not Leo Laport. That man is somewhere way off in the distance with no telephones, no computers, no tech at all. So he's probably pretty frustrated right now. I'm kidding. No, it's all for his own good, having himself a nice little retreat this week, so I'm sitting in for him and going to sit down with Mr. Steve Gibson as we get into a great episode of Security now and get into all of the ins and outs and questionable things happening in the world of cybersecurity. How are you doing Mr. Gibson? Hey, aunt, it's great to be with
Steve Gibson (00:02:58):
You this week. There's one other thing that Leo may be without and that would be a birthday party since last week's podcast was titled Ethernet Turned 50, and since no other major topic grabbed the headline for today, I thought it only seemed right to title this one. Leo turns 67, I dig
(00:03:25):
It. Since that will be his age tomorrow now wherever it is, whatever cave he's in somewhere, maybe they'll have a little birthday party for him there, but apparently if he really is off sequestered somewhere, it won't be happening with his normal family. They'll have to defer, I presume, until he gets back. But you and I are going to examine the various answers to some interesting questions, including how many of us still have Adobe Flash player lurking in our machines? What can you do if you lose your Vera Crypt password? Firefox is now a release one 20. What did it just add? What just happened to give? Do not track new hope. Why might you need to rename your own cloud to Pone Cloud? How might using the crush FTP Enterprise Suite crush your spirits? Just how safe is biometric fingerprint authentication. How's that going with Apache's MQ vulnerability? And have you locked your credit bureau access yet? Should pass keys be stored alongside regular passwords or kept somewhere else? What's the best way to prevent ticky youngsters from accessing the internet and is that even possible? What could possibly go wrong with a camera that digitally authenticates and signs its photos? Could we just remove the eus unwanted country certificates? If that happens? What's the best domain registrar and what was Apple's true motivation for announcing RCS messaging for their eye products? We're going to cover a lot of ground today.
Ant Pruitt (00:05:16):
Oh, I mean, you have a lot of questions there,
Steve Gibson (00:05:19):
Sir. I am so full of questions. I don't know what's going on.
Ant Pruitt (00:05:23):
You got a lot of questions. I hope you have a lot of answers because that's some pretty interesting topics there and some, it's probably going to provoke some people and anger some people because I'm looking at one of those issues, especially regarding youngsters, and I want
Steve Gibson (00:05:39):
To talk to you about, because you're a dad.
Ant Pruitt (00:05:41):
Yep. Yeah, I have thoughts and yeah. Yeah, we'll get into that. But first we have to go ahead and get ready to thank one of our fine sponsors here for security Now and this week, the episode of Security Now is brought to you by Palo Alto Networks. The Zero Trust for OT security solution can help your business achieve 351% ROI over five years. That's amazing. Amazing. Palo Alto offers ZT for OT without the trauma. Keeping operational technology secure and running smoothly is a tall order. It's enough to make even the coolest operations director wake up in the middle of the night with sweats. Scary. Now you can have peace of mind with zero Trust, OT security, zero trust OT Security delivers comprehensive visibility and security for all OT assets, networks and remote operations. The Palo Alto Network Solutions provide exceptional OT protection with more than 1100 app IDs for OT protocols.
(00:06:51):
Over 500 profiles for critical OT assets and more than 650 OT specific threat signatures supported. That's quite a lot. It provides best in class security while simplifying OT security management. It sees and protects everything in the network and it automates threat detections while implementing zero trust across all operations. Now here's the thing. You can sleep better with the most comprehensive platform to detect, manage and secure OT assets. Learn how to Palo Alto Networks zero trust for OT security solutions can achieve 351% ROI over five years. To learn more, find the link in the show description or visit palo alto networks.com. That's palo alto networks.com and we thank them for their support of us here at TWIT and for security now. Alright, so Mr. Gibson, I love how you always start to show out here each and every week with some funny little things that we get from our awesome listeners. We have a bunch of them hanging out here in our club, twit Discord. Thank you all for being here, you members, but what's the first thing you got to share with us today, sir?
Steve Gibson (00:08:11):
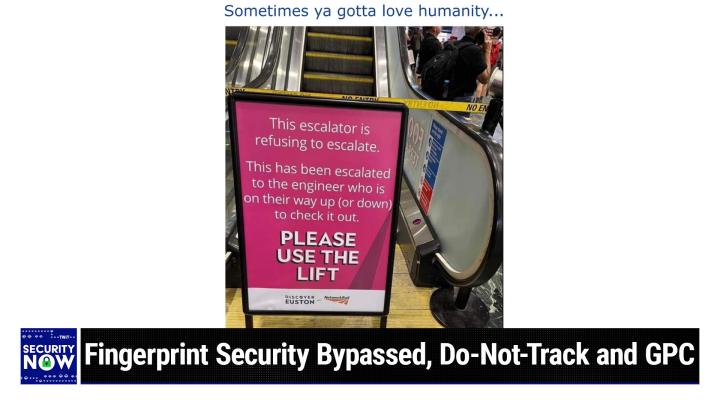
Our pictures of the week. The original concept was to do something security related, something techy, security related. What's happened however is that we've, I guess mostly because I was so fascinated by these, the idea of these gates like a locked gate out in the middle of a field somewhere. It's like, what? Why? So then we've sort of wandered far afield. Anyway, this one was a great one and I gave it the caption. Sometimes you got to love humanity. So this is at Houston, E-U-S-T-O-N Railway station in London and we have like a yellow do not enter tape stretched across an escalator which is not functioning. What's so beautiful is the sign that they put up in front of this, it reads this escalator is refusing to escalate. Okay, that's wonderful. And it says this has been escalated to the engineer who is on their way up or down to check it out.
(00:09:26):
Please use the lift. So anyway, just props to people. This escalator is refusing to escalate. Indeed. It's better than just saying out of order. Got to give. Yeah, exactly. Perfect. Okay, so speaking of out of order or maybe in order this came about because I was still stuck last week on the task of performing unattended server side, Microsoft authentic code signing. I am managing to inch forward with that challenge and I've already made one very useful breakthrough, which was to figure out how to programmatically unlock a pin protected hardware token whose key is stored in one of the new style that they call it A KSP, A key storage provider, HSM hardware dongle. And I do look forward since nobody's been able to do this, I look forward to sharing that with the open source community as soon as I come up for air. Okay, so while working on this last week, I discovered an amazing piece of free technology that I would have gladly paid hundreds of dollars for.
(00:10:47):
It's simply called API monitor. I have a link to it here at the top here in the show notes. It was once a commercial product but it went free about 10 years ago likely because incredible as this thing is, it's only going to appeal to a relatively small audience. Ant I love you, but I doubt that you need an API monitor to track down the inter module API linkage calls in Windows apps. You might be correct, sir. Okay, however, when you need one, oh boy, SO'S going to have a relatively small audience that you probably didn't sell many copies, but if this thing is what you need, there's nothing else like it. I would send the guy a donation. I've tried to write to him, I dunno what happened to him. He's like nominally around, but he hasn't replied. There's not even a donation button on his site.
(00:11:47):
Due to the incredible lack of documentation on Microsoft's next generation cryptography APIs, they literally call it CNG for cryptography. Next generation. I've been reduced to doing a bit of reverse engineering. This API monitor facilitates the creation and exploration of a detailed interactive log of all Windows Module API calls. Now being an OCD perfectionist myself, I'll admit it, I'm not really impressed. I'm sorry, I'm meant to say I'm not readily impressed with other things that I see, but this thing is truly incredible. I won't spend any more of everyone's time raving about it. This is the sort of thing that if you might find it useful, you already know enough to go grab it. It is one of the most utterly stunning pieces of work I've encountered in years. Okay, here's why I'm talking about it other than just to give as gifted author more. Well-deserved public praise. One of its process capture modes allows it to be triggered upon any new Windows process that starts up in the background or in the foreground for that matter. But in this case, it was the background while I was coming up to speed on how this thing works because it's covered with buttons and options and stuff.
(00:13:24):
It also has tutorials I had not disabled because it's enabled by default the trace starting processes option, which I did not need. So I kept seeing popups, which I would dismiss, and it's not unusual for Windows, which is very busy in the background to be just sort of autonomously doing stuff for you. But one in particular caught my eye, it kept popping up. Adobe's flash player, and so while this thing was running this API monitor, it would pop up a dialogue saying, Adobe's flash player updater has launched. Would you like to trace it? And it's like, well first of all, no, but why is Adobe's flash player updater trying to launch? So the first few times I was busy doing what I was doing, I just dismissed it. I said, no, I don't want that. But finally I thought, okay, wait a minute, what is going on?
(00:14:34):
Okay, so I in my machine, Adobe Flash player Updater was still alive. The problem with leaving something like this attempting to run in the background is I don't know what URL this thing was constantly querying. Hopefully it was a subdomain of Adobe and not some separate domain from flash players Legacy Macromedia days that might not be renewed, but if whatever domain the updater was querying were ever to become available for any reason, a bazillion PCs around the world, apparently like mine would be querying it for an update. Now hopefully Adobe also did the right thing and had any updates digitally signed with a pinned certificate so that the updater would only accept updated code that had been signed with an absolutely specific Adobe certificate that would on its face prevent a malicious actor from injecting their code into these bazillion systems around the world that are all still apparently attempting to update their long since retired copy of Adobe Flash.
(00:16:03):
Okay, so here's what Adobe had to say about their retirement. A flash player, they said since Adobe no longer supports Flash player after December 31st, 2020 and blocked flash content from running in Flash Player beginning January 12th, 2021, Adobe strongly recommends all users immediately uninstall Flash player to help protect their systems. Okay, well, as we all know, flash Player was nothing short of a catastrophic security disaster from the moment it appeared. And of course, how many episodes in this podcast's past were we saying, well once again exploits of a flash player, blah, blah, blah. So now Adobe was never seen to be using language like Adobe. Strongly recommends all users immediately uninstall Flash player to help protect their systems, help protect the systems. While it was a going concern, right? It was only after they've decided to finally give up that they said, okay, now get rid of it because it's a disaster on their Flash player end of life FAQ page.
(00:17:26):
They ask themselves, why should I uninstall Flash player from my system? Then they provide the answer. Flash player they said may remain on your system unless you uninstall it. Uninstalling Flash Player will help secure your system since Adobe will not issue flash player updates or security patches after the end of life date. Adobe blocked flash content from running in Flash player beginning January 12th, 2021, and the major browser vendors have disabled and will continue to disable flash player from running after the EOL date. Okay, so first of all, I have no idea why my computer still had it installed. As we know, at one time millions of websites and many standalone enterprise applications were dependent upon Flash player for their operation. I had it installed for research purposes and I had been blocking its operation through browsers since early in this podcast. It was clearly a disaster, but had I received any proactive Adobe reminder or suggestion that Flash player had gone EOL, I mean we talked about it at the time on the podcast, I would've clicked there, remove a flash player option.
(00:18:54):
I doubt that ever happened. I certainly would've clicked it if it had. This suggests to me that Adobe may not have been as proactive in promoting flash player's removal as they might've been, and even now when for the past several years their flash player updater code has been running every hour in my system probing to see if there's been an update, why could they not have provided one final update at any time, which would've caused Flash updater to remove itself either immediately or the next time my system restarted. This could have been done anytime in the last three years.
Ant Pruitt (00:19:45):
Sounds like with the call back to home, if you will, is just another way for Adobe to do some data extraction, potentially say, Hey, who is calling the home?
Steve Gibson (00:19:56):
It certainly has that ability, right? They have a server somewhere presumably still answering these calls, maybe not. Maybe there's nothing there any longer or they're answering the calls and they've got this massive library of all the ips of all the systems and who knows what else, whether information is sending back. I don't want to disparage them anymore, but still, I guess my point is why haven't they shut this down themselves because they could. Okay, so anyway, I first examined my system's registered system services and sure enough right up there at the top when sorted an alphabetical order was A-D-O-B-E, right? Adobe Flash Player update service. The services run state was set to manual. So next I went over to my systems task scheduler app and once again, along with scheduled tasks to keep Google Chrome and Microsoft Edge and a few other odds and ends updated was the task asked to run Adobe Flash update service hourly around the clock. My next stop was Windows programs and features where Adobe Flash player was once again at the head of the class. I highlighted it and clicked uninstall and to its credit, it did indeed remove every trace of itself from my system and good riddance. Okay, so this leaves us with two questions. First, how many of this podcast's security minded listeners might also still have flash player and it's very persistent updater present in their systems? We don't know. I did.
Ant Pruitt (00:21:51):
We don't know, but I think it's again, being someone that listens to this show, they're probably really security conscious and like you potentially had it on the system just for research purposes.
Steve Gibson (00:22:04):
Could have been or one of those I'll get around to doing it and never did anyway. Since it doesn't show unless you peek into the proper corners of your system, it might be worth taking a look at your various Windows machines under programs and features. Just make sure that it's not still represented there and while you're at it, why not scan through that list and remove any of the other cruft that most systems tend to accumulate over time? I bet you that there's a bunch of stuff there that you're never going to use again. Okay, the second question is why hasn't Adobe at least been proactive in shutting down the probable millions of Adobe Flash player updater instances that must still be running around the world? The idea of them still having their hooks literally into all of these systems is more than a bit disturbing.
(00:23:05):
Nearly three years ago they formally stopped further updating of Flash player. So if they were unwilling to proactively remove flash player from everyone's machines, at least they could use everyone's hourly query to remotely shut down all future queries by removing the task scheduler entry and the update service from everyone's machine. Adobe never did seem to be highly responsible with their shepherding of Flash player after they acquired it from Macromedia, but at this point it's everyone's individual to protect themselves. So I just wanted to give a heads up. This happened last week. I didn't know even suspected it was still there doing this if anybody finds it in their machine, clearly it's long since time to get rid of it. Yeah,
Ant Pruitt (00:24:00):
Well like I said, it's probably a data grab. I put nothing behind these companies, these big tech companies, it's all data and it's all cache and they're just going to figure out a way to continue to capitalize off of all the data that they can get. Mr. Gibson, one more thing I wanted to point out. One of our members here in the Discord mentioned that the API monitor URL, we must mention that it is not an H-T-T-T-S-U-R-L, so just
Steve Gibson (00:24:35):
That's a very good point
Ant Pruitt (00:24:36):
That would a grain of salt and thank you. I believe it was quippy
Steve Gibson (00:24:39):
There and actually that flows from the point I made a while ago, which got me in trouble with our listeners when I said there's a lot of still very useful stuff on the internet, which is not https. So it may be, I mean I'm wondering who's paying for this and where this is hosted. It is at his own domain, but that's a very good point. I just scrolled back and looked. It is not H-T-T-P-S, so just HTTP. So that's a good point and I don't think I checked the signature I normally do. I don't think I did. It was bad on me for not seeing if it was digitally signed, but still. Wow, beautiful, beautiful piece of work. So over the weekend I received a note from a desperate person. Now I don't know if he's a listener, it's unclear why he wrote to me perhaps GRC came up in a Google search for the term Vera crypt because it does, because we've talked about Vera Crypt a lot in the past, but in any event, this is what he wrote.
(00:25:45):
He said, hi, Vera Crypt, password lost. How can I get into my device? Vet site? Vera Krypto site says it's impossible, and then he provides a link. He says, so everything on this device is lost. Please if you can help appreciate any slash all help. And he just signed off with his initials CGS. He later sent a second email inquiring whether my consulting services were available for hire. They're not, but I would've told him the same thing and I did write back to him, so sorry, as we might be for this hapless person, the entire reason he or someone presumably chose to encrypt his device with Ryt is because assuming the use of a good password, just as Vera Crips FAQ correctly stated, no help is possible or available by deliberate design, and I said he or someone just now because we only have his statement to lead us to believe that he has any actual legal or ethical right to the data that has been encrypted on that device.
(00:27:14):
Right? Knowing nothing more, it could just as easily be that a thief has stolen someone else's drive knowing that it contains the password information for that person's cryptocurrency, which could be worth millions of dollars. Where the only thing protecting that crypto from the theft is the device's Vera Crypt encryption. And that right now at this very minute, the original true owner of this device is thanking his lucky stars that first he chose Vera Crypt, and second, he also locked that drive up with a password that no one will ever be able to brute force. However, in the meantime, out of an abundance of caution, this person whose jewels have been stolen, has had plenty of time to relocate his crypto to some other wallet where it will now again, be safe in any event, the lesson here is A use vevera crypt. It remains the go-to solution for open source audited whole drive or partition encryption. B, no matter what, always use a really strong and difficult to brute force password. And C, be very careful to create ample backups of the password you assigned. Again, I know our listeners know this, but it's just as a reminder, there is no way to get your vevera crypt data back on purpose. You don't want anybody else who were to steal your drive to be able to get your data back. So make a copy of your impossible to remember password.
Ant Pruitt (00:29:03):
You have to that phrase right there, make a copy of your password, could sometimes be problematic depending on the person you're saying that too. What type of suggestions do you or recommendations do you have for someone that's going to make a copy of their quote master password far as what should it be in, where should it be stored, that kind of thing. Because we're not necessarily saying we're write your password down, put it on a sticky note and stick it up under the seat cushion.
Steve Gibson (00:29:31):
Right? I would not post it behind you when you're doing web conferences. That would not be good.
Ant Pruitt (00:29:39):
Or that
Steve Gibson (00:29:41):
Bruce Schneider, the security guru that we refer to frequently on the podcast, made a comment once that has stuck with me. When asked about that, he said, write it down. He said, we are very good at managing little bits of paper. He said, we are not good at storing things securely. So the point being, I would print it out on a piece of paper and put it somewhere and consider the risk profile. It is often the case that you're protecting yourself from someone in Russia or China, some hostile foreign nation. They're not going to come to your home from their country and get into the shoebox you have tucked away under the bed. That's not going to happen. So that would be a safe place to destroy your password. Now, it would not be safe to store it from your kids because they would get into the shoebox that you have.
(00:30:49):
So you have to keep the threat model in mind if you keep a safety deposit box or if you have an attorney you trust. And also remember, you don't have to actually store the correct password. You could store the password with one change being made to it and nobody would ever know what that change was or drop off a chunk of text that you know, always add to the end of your passwords, that kind of thing. So there are lots of things you could do in order to arrange to have it available for sure when you need it, but it's worth taking those kinds of measures. It's sort of a variation on the theme of what happens if you die and like now what about your spouse and people you care about and their need to access your stuff in order to help manage the existence that you had up until then.
(00:31:52):
These sorts of things really do need to be given some consideration. Good point. Good point. So exactly one week ago, last Tuesday, Firefox released to their so-called release channel, their version 120. And while this is going on all the time with all of our browsers, this one is worth taking a moment to examine. As we noted last week with the impending end of Chrome's support for manifest 2.0, which will disrupt the operation of some of Chrome's more popular advertising and tracking controlling extensions. We may soon be seeing a welcome resurgence in Firefox's popularity because presumably they will continue to support you block origin and privacy badger and ad blocker and the other things that people really liked to use. So I Firefox release one 20, as I said, brings us a few new features that are worth noting. For one thing, it's right click popup context menu when you right click on a link now adds a new feature down toward the bottom named copy link without site tracking, which Mozilla says ensures that any copy links will no longer contain tracking information and I think that's a great new feature.
(00:33:31):
Why would you not do that? As we know, one of the ways that we are being tracked is that links are being embellished with unique identifiers and if you just copy the whole link, you're going to copy that identifier. Wherever that link goes, whoever clicks on it in the future is going to be sending that identifier to the links target unwittingly. So copy link without site tracking, cool new feature. Firefox now also supports the welcome setting. It's under preferences, privacy and security to enable GPC, which we did a whole podcast on a while back. That's global privacy control, which is a newly defined beacon, which is receiving some legal support in order to enforce and encourage its adoption by websites. So although this is opt-in during normal browsing, it is enabled in private browsing mode by default. Also in that same privacy and the privacy and security region, you'll find the do not track request, which can also and should be enabled as I mentioned a few weeks ago after rediscovering the E'S privacy.
(00:34:57):
Badger Privacy badger also adds those beacons to every user's web requests, but there's no harm in adding a belt to go with those suspenders. So I also have some very encouraging news about the future of d and t to share in a minute, but a few more Firefox features first Firefox's private Windows and its ETP Strict privacy configuration now also enhances its canvas APIs with fingerprinting protection. Essentially continuing to protect the user's online privacy as we've discussed in the past, allowing websites to probe various subtle details of how a given browser renders specific pixel illumination to the user's. Viewing canvas is just one more trick that the trackers have developed to follow us around the internet. So Firefox has taken measures to obfuscate that. Okay, outstanding. Outstanding. Yes and listen to this one. This is a cool one. Firefox is rolling out cookie banner blocking in the browser by default in private windows, but only for users in Germany during the coming weeks.
(00:36:19):
Firefox well, but first Firefox will now auto refuse cookies and dismiss annoying cookie banners for supported sites. Furthermore, also only for all users in Germany for the time being. Firefox has enabled URL tracking protection by default in private windows. Firefox will remove non-essential URL query parameters just like we were talking happens if you right click on a link and select that option now, which are often used to track users across the web. Again, I'll allow more to say about Germany in a minute. Firefox now imports TLS trust anchors Web Security security certificate authority certificates from the operating systems root store. Now that's a little controversial for reasons we'll explain. This will be enabled by default on Windows, Mac, OSS, and Android and if needed can be turned off in settings under preferences, privacy and security certificates. On my Firefox one 20, this checkbox is labeled and yes, it was enabled by default.
(00:37:39):
It says Allow Firefox to automatically trust third party route certificates you install. Okay, now my problem with this wording is that it's misleading. It sounds as though users you, because the word it uses as though users would be the ones to install those third party certificates, but that's almost never the case. Presumably Mozilla is attempting to be more compatible with the third party TLS Proxying middle boxes increasingly employed by enterprises to filter their network traffic. The use of any of those requires that the browser trusts the certificates that those boxes mint on the fly. Those third party route certs are typically installed directly into the operating system over the network through active directory and group policies. Firefox has been unique in that it has always used its own root store, which it has brought along and has not been dependent upon the hosting operating systems root store.
(00:38:49):
So it must be that this recent move just now with Firefox one 20 is intended to make the use of Firefox easier in such enterprise settings. Now that's great for the enterprise. We'd like to see more use of Firefox there. The worry is that if the EU gets its way with this misdirected E-I-D-A-S 2.0 quacks certificates mess and is able thereby to force browsers and operating systems to install their member countries web certificates into their root stores, then this mechanism, which has just now been added to Firefox one 20 would automatically place it into compliance with that EU effort. Okay, now given Mozilla's clearly and quite strongly publicly stated position on the eus E-I-D-A-S 2.0 crack certificates, it seems unlikely to me that pre-compliance with something to which Microsoft and Mozilla and others quite strongly disagrees is likely. Remember that rather than signing onto that large open letter that most others co-signed, Mozilla chose to write one of their own, which the likes of CloudFlare Fastly and the ISRG and the Linux Foundation and others all co-signed.
(00:40:25):
So my guess is that it's the smoother functioning within the enterprise, which was the sole motivation. And note that we do have a simple checkbox that any of us can uncheck if we do not want to have Firefox's root store augmented or polluted by its use of the underlying Hostos's root store. Okay, so what about Firefox and this Germany business? Yes, please. There were several interesting changes in Firefox, which I just mentioned, which only benefit German users. What's up with that? It turns out that German courts have been weighing several issues and that their decisions have come down on the side of user privacy and choice. TechRadar pulled together a nice piece providing this recent news and also some backstory about the DNT and GPC beacons. So with a bit of editing by me, here's what TechRadar explained. They said Germany is perhaps the most proactive country when it comes to protecting its citizens' privacy.
(00:41:38):
Something that privacy advocates and enthusiasts have been aware of for a while now and the country recently reiterated its stance against Microsoft owned LinkedIn. A Berlin Court found in favor of the Federation of German consumer organizations, which filed a lawsuit against LinkedIn for ignoring users who turned on the do not track function in their browsers. According to the German judge, companies must respect these settings under the GDPR. So that's big news. It's a small victory for privacy, but this do not track ruling might end up reshaping how websites and other online platforms have to handle our data more broadly. Adoption and support of DNT has been in sharp decline from its initial introduction back in 2009. Now AdBlocker and VPN service provider Agar was asked by TechRadar. Agar believes this is a potentially game-changing court decision, which could, as they put it, exhume the once abandoned and apparently buried privacy initiative for good. A little bit more backstory here.
(00:43:11):
Do not track headers as we know are beacons sent by browsers to proactively inform a website not to collect or track that visitors browsing. DNT was first proposed by security researchers, Christopher Ian SSID STA and Dan Kaminsky, well back in 2009 to limit web tracking and I just jumped on this thing full on because it was such a clean, beautiful, simple idea. Just simply turn on a header that says, I don't thank you very much. I'm a person who does not want to be tracked. A year later after 2009, the U-S-F-T-C, our Federal Trade Commission gave its approval and called for the creation of a universal mechanism to give users more agency over their data. The first web browser to support the new initiative was Mozilla Firefox, which added the feature in March of 2011. Other services followed suit including Microsoft's Internet Explorer and that back then IE was the big browser at the time.
(00:44:23):
So them adding it was a big deal. Apple safari and opera were included. Google Chrome embrace the industry trend back in 2012. Now, as our longtime listeners may remember, the problem was IE from Microsoft turned this on by default. The fact that it was on by default allowed those who were fighting against it to take the position that well wait a minute, if it's on by default, then it doesn't necessarily reflect what the user wants. Choice, no choice there. So because it's always on, we're going to ignore it. Thank you very much. Anyway, so Agar said the early 2010s was perhaps the time when the enthusiasm for the DNT and its potential to improve privacy was at its peak. Okay, so unfortunately after initial success with browsers, the DNT wave seemed destined to dwindle. The problem started from the lack of similar support among websites and advertisers. They didn't want to do it. I mean they didn't want to obey it and nobody was making them obey it. So why would they? That's where GPC stands to benefit and why this recent decision in Germany is significant. The German court is saying you have to pay attention to this.
(00:45:52):
Wow. Even Google that implemented the DNT feature on its browser refused to change its behavior on its own websites and web services. In other words, naturally they declined to honor DNT requests themselves, even from users on their own browser who had turned it on. Shocking. Yeah, the final nail in the coffin came in 2019 when the group working on standardizing DNT was finally dismantled just due to lack of anything happening. And we talked about this at the time on the podcast. So privacy advocacy groups did not want to renounce giving users a better way to help protect their personal data and browsing activities they wanted to hold on. Agar explained, they said quote, while d and t failed to gain much support, the need for a mechanism that would allow people to opt out of having their personal information shared or sold was still strong privacy focused experts believe organizations should allow their customers to decide whether to have their information shared or sold in the first place.
(00:47:10):
It was from this need for an alternative that the global Privacy control GPC was born a couple years ago in 2020, like DNT, the GPC is a signal sent with every web request over H TT P and h TT PS to opt out. Having browsing data collected or sold. Supporters of this new initiative include many privacy first browsers and search engines like DuckDuckGo, brave and Firefox and browser extensions such as Abby's Blur Disconnect, opt me out, and the EFS privacy Badger. As I mentioned before, GPC seems to have gained more traction than DNT was ever capable of until now, at least where DNT may be catching up. And I think it's just that in back in 2009 it was still ahead of its time. The idea was correct, but pressure hadn't built up enough against all of this going on as it has now. I mean we even have Google designing their own non tracking system in order to perform some user profiling in order to deliver more relevant ads.
(00:48:26):
So clearly tracking is in trouble at this point in our entire industry. So in August of last year, GPC won its first legal battle in California against the commercial retail brand Sephora. And now on October 30th, 2023. That date may be remembered as a milestone for the DNT initiative because that was the date that the Berlin Regional Court ruled that LinkedIn can no longer ignore its users' DNT requests. Now LinkedIn was not silent on this. We'll get to that in a second, but Rosemary rotten, a legal officer with the German consumer rights group who brought the lawsuit said, when consumers activate the do not track function of their browser, it sends a clear message. They do not want their surfing behavior to be spied on for advertising and other purposes. Now, website operators must respect this signal. It turned out that the judge agreed with Rosemary ruling that LinkedIn is no longer allowed to warn its users that it will be ignoring their DNT signals.
(00:49:45):
That's because under the GDPR, the right to opt out of web tracking and data collection can also be exercised using automated procedures. In other words, the court found that A DNT signal is legally binding. This sets a precedent and revives the all but abandoned idea of do not track. Now as I said, not everyone is happy with this decision. The LinkedIn spokesperson told cyber news, we disagree with the court's decision, which relates to an outdated version of our platform and intend to appeal the ruling. Now outdated. What's outdated, the LinkedIn platform, if the ruling only applies to an outdated version of the LinkedIn platform, then why appeal it? And surely you could see with the growing support for the closely related GPC signal and with Google, as I said, developing their own non tracking means to obtain interest categories for web users. This is a tide that is finally beginning to shift.
(00:51:00):
So anyway, more enforcement is likely coming on the horizon. One decision in one country doesn't change the world overnight, but it is sure a step in the right direction. And there are times when having some ambulance chasing attorneys around can come in handy, can come in handy, let's let them sick them on some other large websites that are not abiding by this court order and we'll begin to get things turned around. And Anna, I think we should take our second break so I can catch my breath and then we will proceed to talk about phone cloud. Well,
Ant Pruitt (00:51:40):
I wanted to ask you something and following up on this here with the d and t because I think about all of the websites that I've gone through throughout the year that are just random websites, whether it be a photography site or some online shopping or what have you. Some of them they put the banner up about tracking cookies and it gives you the option to reject so on and so forth. And then there's others that say, Hey, our site uses tracking cookies, period. You can close this window and carry on or you can get the heck off our website. So this is only going to apply for German sites because I guess we're still going to see a bit of the wild wild west everywhere else and still have those banners pop up and say, you know what? You don't have a choice, we're going to track you anyway. Is that what you're saying?
Steve Gibson (00:52:30):
Right. So the pop-up banners and the asking the user for permission or acknowledging that that was something that the GDPR instigated and required that sites do that they proactively get users permission that the DNT and the GPC and it's kind of dumb to have two, it'd be nice if we just amalgamated them into a single beacon, but those are settings that the user can set in their browser so that the browser is itself saying, I don't want to be tracked. I don't want to have my information aggregated and sold or shared with others. So I think where we are at the moment is in this confusing set of changing times. So the GDR said to websites, if you're going to be using tracking, you need to inform the user and obtain their permission. That's why we got all these ridiculous banners that you have to click in order to make go away. Now the court is saying even that is obsolete. If the user has DNT and GPC beacons on period, you are never allowed to track them. No reason to put up a cookie banner because you can't be using cookies that are going to be tracking them, right?
Ant Pruitt (00:53:58):
And then that's if they use an automated beacon is what you're right
Steve Gibson (00:54:02):
And all the browsers, I mean that's the thing that Firefox just added and other browsers are beginning to return to. And so I think this is what's going to happen. Basically browsers are simply going to be saying this and websites are going to start having to conform form. They're going to be kicking and screaming. On the other hand, Google has now formally rolled out their interest category system. That's what everyone's going to have to switch to and remember, it's way weaker than tracking. I mean tracking allows the aggregation of all kinds of crap instead of just like what are the interests that your recent web behavior has suggested that you might have, which is the Google replacement system. So I have a feeling tracking's not long for the world as we know things don't change soon, but they do eventually change,
Ant Pruitt (00:55:00):
Right? This is a start. This is a start. Sweet. Well sir, go ahead and take a quick break and get your breath back. Before we get into OnCloud and phone cloud, I'm going to take a few minutes to think this week's fine sponsor. This episode of Security Now is brought to you by Melissa, the data quality experts. For over 38 years, Melissa has helped companies harness the value of their customer's data to drive insight, maintain data quality, and support global intelligence. Now listen, all data expires up to 25% per year. Having clean and verified data helps customers have a smooth error-free purchase experience, especially this time of year, the holiday season, and people are getting ready for holiday gifts and holiday cards and mailing lists and all of that. This is definitely the time to consider this flexible to fit any business model. Melissa verifies addresses for more than 240 countries and to ensure only valid billing and shipping addresses enter your system, Melissa's international address validation, cleans and corrects street addresses worldwide automatically transliterating from one system to another.
(00:56:22):
For example, like Chinese to Relic. Pretty easy stuff there. No, it's not easy, but they make it look easy. Focus your spending where it matters to most. Melissa offers free trials and sample codes and flexible pricing, even offer an ROI guarantee unlimited technical support to customers all around the globe. Once you're signed up with Melissa, it's easy to integrate their service, their other services. So you have Melissa identity verification. This will allows you to increase compliance, reduce fraud, and improve onboarding. Then there's Melissa and Rich here you can gain insight into who and where your customers are now. Then there's also Melissa's education portal, which is available to individuals with a valid.edu email address. Now that's pretty awesome. The popular feature is designed to introduce future data scientists to the inherent value of data and its global relevance in an ever increasing range of industries and applications.
(00:57:31):
So you can download the free Melissa's lookup apps on Google Play or the Apple App store and there's no signup required, validate and address and personal identity in the US or Canada. Check global phone numbers to find caller, carrier and geographical information. You can also check global IP address information is so much more. Melissa has achieved the highest level of security status available by gaining FedRAMP authorization. Now while these technologies are exclusively for governmental agencies, all Melissa users benefit from the superior level of security. Melissa's solutions and services are GDPR and CCPA compliant and they meet SOC two and HIPAA HITRUST standards and information security management. Make sure your customer contact data is up to date. Get started today with 1000 records clean for free at melissa.com/twit. One more time. That's melissa.com/twit for all of your data cleaning up processes. Good stuff. Thank you so much for supporting the show Melissa. Really do appreciate you. Now Mr. Gibson, so ownCloud P cloud, tomato, tomatoes, one of those things. What's the deal here? It
Steve Gibson (00:59:03):
Appears that anyone running any instance of the very popular open source own cloud file sharing system needs to take immediate action as in stop listening to this podcast right now and immediately anything running on cloud to get it off the internet. Unfortunately, due to today's ultra swift nature of the exploitation of any publicly announced new vulnerabilities in this case, it's a remotely exploitable CVSS 10 out of 10, which is difficult to get. It may already be too late, but even if so, at least closing the unlocked front door and working to clean up any damage still needs to be done. Okay, so here's the story. Gray noise reported the following in their coverage of CVE 20 23 49 1 0 3. Yesterday they wrote under the title own cloud critical vulnerability Quickly Exploited in the Wild. They said on November 21st, 2023. So that's exactly one week ago today, own ownCloud publicly disclosed a critical vulnerability with A-C-V-S-S severity of 10 out of 10.
(01:00:24):
This vulnerability tracked as CVE 20 23 49 1 0 3 affects the graph API app used in ownCloud. ownCloud they wrote is a file server and collaboration platform that enables secure storage sharing and synchronization of commonly sensitive files. The vulnerability allows attackers to access admin passwords, mail server credentials, and license keys. Gray noise has observed a mass exploitation of this vulnerability in the wild as early as November 25th, 2023. Okay, so it took four days from the announcement for mass exploitation to take off. They said the vulnerability arises from a flaw in the graph API app present in ownCloud version 0.20 to 0.30. This app utilizes a third party library that will reveal sensitive PHP environment configurations, including passwords and keys disabling the app does not entirely resolve the issue. And even non-con containerized own cloud instances remain at risk. Docker containers before February, 2023 are not affected. Mitigation information listed in the vendor's disclosure includes manual efforts such as deleting a directory and changing any secrets that may have been accessed.
(01:01:53):
In addition to this vulnerability 49 1 0 3 ownCloud has also disclosed other critical vulnerabilities including an authentication of bypass flaw 49 105 and a critical flaw related to the OAuth two app. That's 49 1 0 4. Organizations using OMM Cloud should address these vulnerabilities immediately. Okay, that's bad for ownCloud users. We have a potential four alarm fire situation. There are three newly disclosed CVEs with ratings of the difficult to obtain 10.0 a highly critical 9.8 and a still very bad 9.0. That 49 1 with A-C-V-S-S of 10.0 allows for a disclosure of sensitive credentials and configuration in both containerized and non-con containerized deployments. The 49 1 0 5 CE is the second worst with A-C-V-S-S of 9.8. It's a I authentication bypass using pre-signed URLs, which impacts core versions, which 10.60 to 10 point 13.0. And the third 49 1 with a CSS of 9.0 is a subdomain validation bypass impacting OAuth two prior to version 0.6 0.1.
(01:03:28):
So in the case of this first worst mistake and really a mistake is what it is. It's not some fancy log for J. Tricky to exploit vulnerability. Anyone who has any experience with PHP knows that you never want to expose PHPs HP info appt to the public internet yet. That's exactly what this Graph API has done. Located down the path slash API slash microsoft slash microsoft graph slash tests is a HP file and it can be accessed remotely to disgorge all of the systems internal sensitive data, including all the environment variables of the web server and in containerized deployments. This includes the ownCloud admin password mail, server credentials, and license keys. ownCloud themselves recommends deleting that file and administratively disabling the very dangerous HP info function. This can be done by simply adding PHP info to the disable functions list in the system's PHP, any file.
(01:05:02):
And sadly, that list is empty by default, meaning HP ships with HP info enabled not on my PHP instances, but by default. After doing this, however, do not make the mistake of not also immediately rotating all of the systems credentials, the admin password, the mail server and database credentials as well as object store S3 access keys of the own cloud instance was hosted by an S3 cloud provider. Again, multiple, I think it was 12 independent, probably malicious, we don't know, maybe they were some security firms, but there were 12 unique ipss identified scanning the internet looking for instances of own cloud. So in this instance you have to presume your instance was infected by something if it was exposed to the internet since essentially they all were. The second problem makes it possible that is that the other CVE at 9.8 to access, modify or delete any file without any authentication if only the username of the target is known.
(01:06:28):
And if they have no signing key configured on their account, which is the default behavior that is not to have one. That's also obviously quite a potentially serious vulnerability to be able to access, modify or delete any file without any authentication, knowing only the username of the target. And the third 9.0 flaw relates to a case of improper access control that allows an attacker to pass a specially crafted redirect RL, which bypasses the validation code and thus allows the attacker to redirect callbacks to A TLD controlled by the attacker, a top level domain controlled by the attacker. Anyway, bottom line, everyone using OM cloud should update to the latest builds and make sure that everything else is still okay. As I did say 12 unique ipss were found to be scanning the internet looking for instances of OMM Cloud and were carrying through with exploits.
(01:07:28):
So update, change all of your sensitive credentials. It's a must do. Unfortunately, while we're on the topic of critical vulnerabilities that will wreck your day or your week or maybe even your month. Anyone using the sadly named crush FTP Enterprise Suite and are therefore currently somewhere around 10,000 publicly exposed instances of it on the internet must immediately update version 10.5 0.2 or later. Back in August, the security firm converged technology solutions responsibly disclosed a critical unauthenticated zero day vulnerability, meaning you don't need authentication to use it to exploit it, which affects the crush FTP Enterprise Suite. Having 10,000 of these instances publicly exposed is bad enough, but a great many more are known to be residing behind corporate firewalls, which malware might manage to crawl behind. The exploit permits an unauthenticated attacker to access all crush FTP sites run arbitrary programs on the hosts server and acquire plain text passwords.
(01:08:54):
The vulnerability was fixed in crush FTP version, as I said, 10.5 0.2, and it affects software in the default configuration on all operating systems. What's more converges threat intelligence has discovered that the security patch, which resolved this problem has been reverse engineered, and adversaries have developed proofs of concepts so forthcoming exploitation can be presumed. Update immediately. The attack chain hinges upon an unauthenticated query when crush FTP parses request headers for a data transfer protocol called AS two. By exploiting the a s two header parsing logic, which obviously has a flaw, the attacker gains partial control over user information Java properties. This properties object can then be leveraged to establish an arbitrary file read and delete primitive on the host system. Using that capability, the attacker can escalate to full system compromise, including route level remote code execution. So it's really bad. 10,000 instances are public, the patch has been reverse engineered. Those 10,000 servers are going to get attacked. Update to 10.5 0.2 ASAP if your enterprise is using the crush FTP, because as I noted at the top, you don't want to have your spirits crushed.
Ant Pruitt (01:10:35):
Wow. With something like this, because I just looked up this crush, FTP, you're saying this is 10.5 or graders where we need to step up to, they're already up to like 10.9 with this application. Is there any reason why someone would use this? Because there are plenty of other FTPs options out there, including some open source options that are out there. Why would an enterprise not even look at the open source side of things?
Steve Gibson (01:11:07):
Well, I did not look to see what crush FDP Enterprise Suite means. And for example, this as two protocol is something I've never encountered by ftp. So it may be that it's got a bunch of extra special features that specifically target it to the enterprise. And who knows a suite implies there are other components to it. So it may be a big package that has a whole bunch of other stuff that is targeted at the enterprise. And this crush FTP server is just one of the modules. Unfortunately, it only takes one to be bad in order to give the whole thing, make the whole thing problematic. True.
(01:11:53):
So a very interesting set of flaws has been found in the fingerprint sensors manufactured by GoodEx, G-O-O-D-I-X Synaptics. They're a very popular supplier I ran across Synaptics. They make the touch pads in most laptops and Elon, ELAN, the OEMs who purchase and integrate those sensors and whose equipment is therefore vulnerable to fingerprint sensor based authentication Bypasses include the Dell Inspiron 15, the Lenovo ThinkPad T 14, and Microsoft Surface Pro X laptops just to name a few, which are known to contain these popular sensors. So this is what happens when a hardware savvy security firm takes a close look at what's going on inside of fingerprint sensors and as is often the case, the result is frightening. All three of the fingerprint sensors are the good kind, which perform something known as MOC verification, which stands for match on chip. That's what you want since it integrates the matching and other biometric management functions directly onto the sensor's integrated chip.
(01:13:18):
But the researcher said, while MOC prevents replaying stored fingerprint data to the host for matching, it does not in itself prevent a malicious sensor from spoofing a legitimate sensor's communication with the host and thus falsely claiming that an authorized user has successfully authenticated. Okay, so to thwart this problem in general, Microsoft created something known as the Secure Device Connection Protocol, SDCP. It's designed to eliminate this problem by establishing an end-to-end secure channel between the sensor and the machine's motherboard and how this can be done in practice TLS. That is the protocol that HTTP uses to establish a secure connection between endpoints in full public view. It works. So SDCP can theoretically work. You're able to share secret keys, establish a symmetric key, and as long as you have authentication of the endpoints that can potentially be secure. But the researchers designed a novel technique that can successfully circumvent these SDCP protections to create adversary in the middle attacks as they called them.
(01:14:58):
Oh, of course they did. Now that's, if this is turned on, get a load of this. The ELLAN sensor, which interfaces over USB doesn't even offer SDCP. So it's easily spoofed simply by sending clear text security identifiers. This allows any device, any USB device to masquerade as a fingerprint sensor and claim that an authorized user is logging in. In the case of the Synaptics fingerprint sensors, not only was SDCP found to be turned off by default, the implementation used a known flawed custom TLS stack to secure its USB communications between the host driver and the sensor. So once again, it was possible to defeat the biometric authentication. The exploitation of the good X-G-O-O-D-I-X sensors leverages a fundamental difference in enrollment operations carried on all out on a machine that's using Windows versus Linux, or a machine that transiently boots a copy of Linux. This takes advantage of the fact that Linux does not support SDCP.
(01:16:24):
So we have what is essentially a protocol downgrade attack. This truly lovely hack is done as follows, boot Linux enumerate valid IDs, enroll the attacker's fingerprint using the same ID as a legitimate Windows user. And again, you can do this because SDCP is not supported by Linux intercept the connection between the host and the sensor by leveraging the clear text USB communication, then boot to Windows intercept and rewrite the configuration packet to point to the Linux database, and finally log in as the legitimate Windows user with the attacker's fingerprint. Essentially, this allows for the installation of an attacker's fingerprint and association to the legitimate user's fingerprint. It's also worth noting that although the good sensor design anticipated this bait and switch weakness and therefore uses separate fingerprint template databases for Windows and for non Windows systems, the attack is still possible thanks to the fact that the host driver sends an unauthenticated configuration packet to the sensor to specify what database to use during sensor initialization.
(01:17:52):
So you simply change that, point it to the Linux database, and now you log in with a fingerprint that you set up when the system had been booted under Linux to mitigate such attacks. The researchers have recommended that OEMs enable SDCP and ensure that the fingerprint sensor implementation is audited by independent qualified experts. These guys did that. So we insert our standard refrain there, have the security audited by somebody who wants to find flaws, not by your own people who've just finished writing it themselves and assume it works. Just for the record, this is not the first time windows. Hello. Biometrics based authentication has been successfully defeated In July of 2021, Microsoft issued patches for a medium severity security flaw, 20 21, 34, 4 66 that had A-C-V-S-S of only 6.1, but it could still permit an adversary to spoof a target's face and get around the login screen.
(01:18:59):
The researchers said that Microsoft did a good job designing SDCP to provide a secure channel between the host and biometric devices, but unfortunately, device manufacturers seem to misunderstand some of the objectives. Additionally, like having it turned off by default. I would call that a misunderstanding. Additionally, SDCP only covers a very narrow scope of a typical device's operation, while most devices have a sizable attack surface exposed that is not covered by SDCP at all. Okay? So I think our takeaway from this should be to not over rely upon the convenience offered by biometric authentication. Yes, it's convenient to be able to hold your phone up and have it look at you and say, oh, that's Steve, or that's Ant, or whomever, but this is why Apple whose biometric authentication has been very tightly designed by security. Crazed engineers will require the something you know to be provided initially when you're unlocking your device following any restart. If I had any device who security was truly critical to me, I'd encrypt its drive and I would supply the key with an outboard USB dongle, not something biometric. In fact, that's what I did when I was in Europe traveling with a laptop during the squirrel tour tour years ago was it was deeply encrypted and I used a physical dongle in order to supply the unlock key.
Ant Pruitt (01:20:53):
Mr. Gibson, looking at this story, I think about, there's an old adage of if there's a problem, typically you can throw some money at it to fix it. And I know that may not apply for everything, especially when it comes to hardware, computer hardware and whatnot, but I'm looking at these manufacturers, these OEMs that provide this, what was that one touch pad? Hold on, I got to scroll up. In everything, that touch pad is in everything, and typically it's in the less expensive laptops that are out there. Microsoft, is this on Microsoft or is this on Synaptics? Because Microsoft clearly got a deal for that licensing to put it in all of these devices, but yet synapsis dropped the ball by cutting that off by cutting off SDCP by default.
Steve Gibson (01:21:52):
So it's probably the case that Synaptics sensors offer SDCP, but I would imagine so we don't know which of these sensors goes with which of the OEMs that I mentioned. I would imagine that Microsoft would require SDCP be enabled. The only one of those three of Elan, Synaptics and GoodEx, where the researchers found SDCP actually enabled and running was on the Microsoft Surface tablets. So that would be my guess. I would be surprising if Microsoft supported this protocol and Synaptics was allowed to leave it off, it would probably have to be turned on.
Ant Pruitt (01:22:39):
Yeah, I was thinking about it and then you brought up Apple and I was like, yep, that's exactly my thought because Apple spends a lot of money on this stuff for pharma security standpoint and those relationships and making sure things are done in a particular way. So I was like, is this just where people are cheaping out on things and should just spend a little bit more money with these relationships and
Steve Gibson (01:23:03):
With these licenses? And is that, as we know, apple did a really strong job of implementing a fingerprint sensor. We covered it in detail when it happened on the podcast. They nailed this technology. The problem is other people come along with a fingerprint sensor and the consumer thinks, oh, it's a fingerprint. Mine's unique, and it's not going to be like anybody else's. They're only looking literally at the surface of their skin that says nothing about the technology that implements what happens when that skin hits the road and actually has the fingerprint red. So just the fact that it requires some biometrics, it implies nothing about the security behind that and that Elam sensor, it doesn't hit us no security at all. It's just wide open. Crazy.
Ant Pruitt (01:24:07):
Yikes. Yikes. Unbelievable. So what's going on with Apache mq, sir?
Steve Gibson (01:24:13):
Well, so we talked about this a few months ago. They had a horrible problem with something known as Apache mq, a message queuing vulnerability. It was another of those 10 point zeros. I just wanted to mention that it remains under very active exploitation. A proof of concept exploit was initially posted on GitHub. It was later updated to add an English language translation, and then two weeks ago it was further improved to change and basically bolster its TLS support. So by now, pretty much any Apache MQ server that has been left unattended will be spinning its fans as fast as possible because crypto miners have been observed being installed into any still vulnerable servers. They've just been turned into crypto miners for as long as they can run generating cryptocurrency for the bad guys.
(01:25:19):
Okay, so public service announcement by way of our major credit reporting bureaus, two of them, TransUnion and Experian were both just hacked with their super sensitive consumer data. Exfiltrated, the hacking group named n numeral four U-G-H-T-Y capital S-E-C-T-U. So that's naughty. SEC two is asking for $30 million from each firm threatening to release its customer's online, and this is the second time the naughty SEC two group has attacked TransUnion having previously done so back in March of last year, 2022. So let me just take this opportunity to once again remind everyone that all four of the major credit reporting bureaus support credit locking and that everyone should be taking advantage of this feature given today's cybercrime environment and the fact that those who are holding and aggregating our private information without our permission, no one ever gave these credit reporting agencies the right to collect all this stuff on us.
(01:26:49):
They just do it and they resell it for money and they track us. So without our permission, they have been proven unable to keep it private. So we need to minimize the chance that our private information will, if it escapes, will then be leveraged against us for identity theft. Identity theft is one of the most debilitating and difficult to recover from things that can happen to an individual. A few years ago, I decided that since I was such a large customer of Amazon, I would start routing my purchases through their card to obtain an additional several percent of savings to apply for their card. I needed to briefly drop my credit reporting agency Shields to allow Amazon's credit folks to verify my credit worthiness. What I learned at the time was that it is now possible to ask the bureaus to temporarily drop our shields for a specified duration like seven days after which time they will automatically snap back up. So that really removes the last barrier of inconvenience from having one's credit reporting blocked. By default, everyone listening and everyone you care about should be running with their shields up full time. There's just no reason not to.
(01:28:30):
Yeah, I agree with you. As we start taking some listener questions, why don't we take our last break and then we will see what Christian has asked.
Ant Pruitt (01:28:38):
Sure, yeah. I'm looking forward to some of the feedback from our fine listeners. Thank you again, Mr. Gibson. Another great episode so far here on security now, and thank you to everybody hanging out watching this live, whether it be in the IRC or here in our club TWI Discord. Really do appreciate y'all being here. But while we take a break, we're going to take the time to thank another fine sponsor for this of security now with our friends at IT Pro tv. But wait a minute, they're actually called a CI Learning now in today's IT shortage, whether you operate as your own department or part of a larger team, your skills must be up to date. 94% of CIOs and CISOs agree that attracting and retaining talent is increasingly critical to their roles access to more than 7,200 hours of content available. A CI Learning consistently adds new content to keep you at the top of your game.
(01:29:33):
Your team will thank you for the entertaining training and a CI learning's completion rate is 50% higher than their competitors. That says a lot right there. A CI Learning is excited to introduce the cyber skills. This is a solution to future-proof your entire organization, not just the IT squad. A lot of people assume that security is all about what's happening in the IT department. Well, the folks outside it, they ought to be up to date on simple security matters too. There's a lot of little simple steps that one can take to keep things secure from the information standpoint. This is a new cybersecurity training tool for all the members of the organization. It's cybersecurity awareness training for all of your non-IT professionals with cyber skills. Get flexible on-demand training, covering everything from password security and phishing scams, which is usually the main one. Phishing scams that gets people to malware prevention and network safety.
(01:30:34):
Your employees will stay motivated and engaged throughout their learning process with easy to follow material with a simple one hour course overview. Your employees gain attack specific training and knowledge check assessments based on common cyber threats that they'll encounter pretty much on a daily basis because those bad guys out there, they're relentless when it comes to trying to attack data. They'll also gain access to bonus courses, documentary style episodes so your employees can learn about cyber attacks and breaches in their own style. I love that that's pretty flexible because some people, they're not geared towards just the standard lecture, if you will. Some people learn more from a story in different types of tutorials, so it's cool that they have this flexibility out there. A CI Learning helps you invest in your team and entrust them to thrive while increasing the entire security of your business.
(01:31:36):
Boost your enterprise cybersecurity confidence today with ACI Learning. Be bold train smart folks. Visit go dot ACI learning.com/twit and twit listeners can receive up to 65% off an IT Pro enterprise solution plan after completing their form. Now this is based on your team's size and your receiver properly quoted discount that is tailored specifically to your needs. So yeah, make sure you check it out. Go do ACI learning.com/twit and we appreciate them for all of their support of us here at TWIT and on security now. All right, so Mr. Gibson, about time to close the loop and check out what our awesome listeners have sent in, right?
Steve Gibson (01:32:25):
Yep. So Christian, I think his name, I would pronounce it Ru Rec, R-U-T-R-E-C-H-T. He's in. I'm
Ant Pruitt (01:32:35):
Going to try to pronounce it,
Steve Gibson (01:32:36):
Not sure, yeah, if you have managed to catch up to Passkey support in Bit Warden. I have not heard it mentioned lately in security. Now I've just started testing it on selective services and it works flawlessly across my various devices. I am very impressed, I must say. And we need to mention that Bit. Warden is a sponsor of the TWIT network. He said, what I would like to know is the view you have on adding all your PA keys to a combined password vault. I know that you have a standpoint that MFA verification apps or physical token devices should be separated, but what about pass keys? Personally, I prefer combining everything for the sake of convenience. I have family members and colleagues that I try to nudge toward using a password manager for them to be able to use it. It must be easygoing. Even the concept of having something, remembering their password for them is complicated to comprehend.
(01:33:38):
For some in my research, I found that the best way of keeping my password security posture up, I'm sorry, posture up to date and readily available for access, is to have a single vault slash app for everything. I chose bid warden for that purpose at the conclusion of my research two years ago as it was the best hardened platform available, including the support for authentication tokens and now pass keys. Keep up the good work. So Christian, I would classify pass keys exactly as I would passwords. Passkey are just superior passwords because by using public key asymmetric crypto instead of secret key symmetric crypto pass keys are inherently immune to a great many of the attacks and failure modes that have always beset passwords. In other words, I think it's entirely acceptable to keep pass keys in the same vault managed right alongside your traditional passwords.
(01:34:50):
And as you noted, I do feel strongly that the entire point of multifactor authentication is to create a clean and clear security boundary for use when remotely authenticating to a higher than usual security facility. For that reason, the idea of having a password manager also able to fill in the time varying six digit MFA token makes me shake my head, why bother at all if that's what you're going to do? It's true that some benefit will be derived from the inherent time varying nature of the token. So simple replay attacks will be thwarted, but if you're going to go to the trouble of using some form of multifactor authentication, why not get as much benefit from it as you can? And that means keeping it separate from your web browser that is able to fill in all the rest of your information, don't have it also fill in your multifactor authentication.
(01:35:56):
But sir, we want convenience. Users want convenience and stuff to be done like right now, duh. In fact, if you want convenience, I would say don't bother adding multifactor authentication to any accounts. If you're going to have your browser automatically fill them in, it's nutty. Okay, so here's the one that's I think interesting aunt that I asked you if you had kids about earlier. I'll read his question. I'll share my reply to him and then let's talk about it. So a listener named Victor wrote, he said, howdy, Steve, longtime IT guy here, but recent about a year listener as I didn't really do podcasts until security. Now I have a question for you that may be something of a rabbit hole, but I'm seeking opinions on parental controls. I consider myself a well enough accomplished IT guy, but I'm facing a problem that one of my kids is about to step into the realm of getting a phone.
(01:36:59):
My wife and I have held off until now citing COPA laws, but we are out of excuses at this point. The issue is that for all of my IT experience, this kid, my third is exceedingly more tech savvy than any of my other kids having already proven their ability to circumvent restrictions on school operated technology and continuing to do so without any repercussion as the school can't seem to collect any evidence of their wrongdoing. I've done my best to protect the home front pie hole PF sense router with static routes to nowhere for undesired sites, et cetera. But once on the phone, the kid will be able to connect when wherever they please, and I have yet to find a truly secure parental control app, which will do all the standard watchdog things and self-protect from deletion on Apple and or Android. Any advice is welcome.
(01:38:07):
Here's to 9, 9, 9 and beyond signed Victor. Okay, so I wrote to him though I never had my own kids during my late twenties, thirties and forties, I participated in raising several long-term girlfriend's, kids from preteen through their teens. And although I was never more than mom's boyfriend, I was around during some important years. So we bonded and I've remained in touch with several of them who are now married and with their own kids. So I'm not a total newbie on this front. Victor didn't share the age of his youngest and most technically savvy of the three. So this might not apply if this individual is too young, but if this person is this tech savvy, then perhaps they're not that young. What occurs to me is to wonder whether this particular problem has a technical solution. I think that perhaps the solution lies in parenting rather than in technology.
(01:39:09):
I'm not horrified. I'm not horrified by what I am horrified. I'm sorry, by what is now available. I was distracted. I should explain to our listeners by Ant who just did a big yay. Congratulations by my saying that the solution lied in parenting rather than technology. My bad, my bad. No, that's okay. Thank you for that. I'm horrified by what is now available on the internet, and I completely get it that age appropriateness is a real thing. There are many salacious adult depravities that young minds should not be exposed to until they've obtained sufficient context and maturity to understand them for what they are. But at the same time, blocking feels like a losing uphill battle. The internet is truly pervasive. If this youngster wants access to the internet, he or she is going to obtain that access, if not at home where it security is strict, then over at a friend's house whose parents never considered this to be a problem, or by breaking through the school's security and erecting technical blockades might just present a challenge to make what's hiding behind them seem all the more intriguing given what's out there.
(01:40:38):
I understand the dilemma that today's parents face, and I would not want to be in that position today. But I also believe that there's a very real limit to a parent's ability to control what a free ranging person is exposed to. I think that if I were in this place in Victor's place, I would sit down with all of my kids as a group and talk to them honestly and openly about what's on the internet and why, about how a great deal of what's there does not represent what most people think and feel about how it's often deliberately extreme about how behind a lot of it is a profit motive trying to separate people from their money one way or the other. And I would also take some time to explain about predation on the internet, about how there are truly dangerous people hiding behind fake names, photos, and identities, that these people are often not who they claim to be. They may well be in a far off country and not be at all nice people, and that the only thing you ever really know are the people who you've met in the real physical world. I would not pull any punches. I'd tell them that I'm terrified by the idea of them being exposed to what's out there on the internet and that the only thing that will keep them safe is their own common sense and keeping lines of communication open with their true friends in the real world and with their parents.
Ant Pruitt (01:42:22):
And look here, first off, let me just give you an applause because everything you just said, we're pretty much in agreement here. I echo you this stuff with the internet, and I think back to my time with my kids. Granted, they're older now. I have one in college, he's a junior in college. I have a high school senior and my oldest boy and my stepson, he is, I believe he's 25 now, so they're out and about. But when phones began to be a big thing in their lives, I was tough. I was hard on, I was like, no, you're not getting the phone, period. You're not getting the phone. And it sucked. I hate to say it that way, it was hard to do that, but I knew that having a phone wouldn't necessarily help them far as getting their work done and being good students and whatnot. But I also thought that it was going to lead to some social issues with kids being kids because kids will make fun of you if you don't wear the right type of t-shirt for whatever reason.
Steve Gibson (01:43:34):
And if you don't have a phone, oh, your mommy will let you have a
Ant Pruitt (01:43:37):
Phone. Exactly. So I knew I was going to be in it for that, but I thought in the long run they were going to be better off. But just as you mentioned, I explained to them why I explained to them the realities of the internet. There's a lot of things out there that are just wild, but then there's also some good stuff on the internet, great information, and I had to teach them, there's going to need to be a balance. And right now at this particular age, you're not ready for a phone. I did the same thing with particular video games. Grand Theft Auto wasn't allowed in my house for a little while now when it got older, sure, now you can play it because you have a little bit more common sense and no, that's not the reality. But mention here in our discord, I believe it was berserk, it says a hundred percent this kid would see the parents as a quote challenge. I agree that right there, I did not want to use tech to get in the way and put up firewalls and things like that because all they were going to do is just try to figure out a way to get around it and put a lot of effort in that that they didn't need to when they should have been putting that same amount of effort into stuff that matters, like homework.
(01:44:54):
So I didn't want to just throw up a brick wall for everything. I just tried to be upfront and say no when I needed to say no. And when it was time for them to be able to get phones and access to the internet and stuff like that, I gave it to 'em with a couple caveats and just sort of eased them into it.
Steve Gibson (01:45:13):
Well, and if nothing else, your being that strong, even if they did go to a friend's house in order to have their curiosity satisfied, the fact that you made such an issue of it that, I mean someone who their dad was saying this is really bad. Even that would tend to create a barrier of caution. It planted a seed that would serve to help them.
Ant Pruitt (01:45:40):
It planted a seed because there were instances where they would come back to the house after visiting. So-and-so relative, this cousin, this friend or what have you, and they would pretty much tell me everything they saw the other kids doing, and they were not comfortable. And I had to tell 'em, okay, yes, thank you for letting me know. It's all right that they did this and that or what have you, but that's in their own home under their own parents' jurisdiction, not my jurisdiction. I appreciate you honoring our relationship and our agreement. Well,
Steve Gibson (01:46:13):
It's very cool too that those lines of communication are kept open because that's the crucial thing you want. That's the key, is for them not to be sneaking around and keeping secrets and thinking that they can't share with their parents what's going on.
Ant Pruitt (01:46:28):
And don't get me wrong, my kids are known as Hardhead. I call 'em the hashtag hardhead on
Steve Gibson (01:46:35):
Wait your kids. I can't imagine
Ant Pruitt (01:46:37):
That there's a reason for that. But at the same time, I do appreciate them being able to come to me and their mother when it comes to stuff about technology and just information security and so forth, or social media. And we still have those talks, and like I said, they're a lot older now, and every now and then, we still have some conversations about things we see on TikTok or things we see on Instagram or what have you, because
Steve Gibson (01:47:04):
It's a crazy world out
Ant Pruitt (01:47:05):
There. It's not just the fact that something could be pornographic or whatever. Some things are just flat out lies sold as truth and they need to say, Hey, I need to check my sources here because that doesn't look right. But yeah, kudos to you and I'm, it's the applause to you, sir.
Steve Gibson (01:47:27):
So Alpha Geek asked, he said, I'm interested in your take of this from a security standpoint and amp. This is about cameras, so you're going to like this too from a security standpoint. He said, thanks for the years of helping keep my brain sharp as a double E. Your podcast has helped me look smart at important times. So great. So what Alpha Geek was curious about, he provided me a link, was an interesting solution to the problem with deep fake photos talking about things being fake on the internet just now, the IEEE Spectrum Magazine carried an interesting story about a new Leica camera that binds authenticating metadata into the photos it takes, then digitally signs them as they are taken, and there's more. So here's where the article explained. Article said, is that photo real? There's a new way to answer that question. Like as M 11 P announced in late October is the world's first camera with support for content credentials, an encryption technology that protects the authenticity of photos taken by the camera.
(01:48:36):
The metadata system can track track a photo from shutter snap to publication, logging every change made along the way. Award-winning photographer David Buto said in the last few years, it's become easier to manipulate pictures digitally photographers can do it, and when the photos are out on the web, other people can do it. I think that puts in jeopardy the strength of photography, the sense that it's a true representation of what someone saw in November of 2019. Adobe, the New York Times and Twitter partnered to solve this problem by founding the Content Authority Initiative. CAI Twitter left the CAI after Elon Musk purchased the company. But CAI now boasts over 200 partners, gave itself the difficult task of finding a long-term holistic solution for verifying the authenticity of photos. In 2021, it joined with another initiative called Project Origin to form the Coalition for Content Provenance and Authenticity.
(01:49:50):
The C two pa, like is M 11 P, is the first hardware embodiment of its solution. The camera has a toggle to flip on content credentials, which is based on the C two PA's open technical standard. The M 11 P then embeds identifying metadata such as the camera, lens, date, time, and location. In an encrypted C two PA manifest, the M 11 P digitally signs the manifest with a secure chip set that has a stored private key. The manifest is attached to the image and can be edited only by C two PA compatible software, which in turn leaves its own signature in the manifest. Once published, the image can display a small interactive icon that reveals details about the photo, including the device used to take the photo, the programs used to edit it, and whether the image is wholly or partially AI generated, it's still early days for content credentials, however, so support is slim.
(01:50:57):
Adobe Software is the only popular image editing suite to support the standard so far. The presentation of the data is also an issue. The interactive icon isn't visible unless an application or program is programmed to present it. David Buto said The way this technology is integrated into Photoshop and Lightroom, which is what I use, is still a bit beta ish. David used the Leica M 11 P for several weeks prior to its release. But he says, these early problems are countered by one key win. The standard is easy for photographers to use. You shoot normally, right? There's nothing that you see, nothing that you're aware of when you're taking the picture. The ikas M 11 P support for content credentials wasn't the only reason it made headlines. It arrived with an intimidating price tag of 9,000 to $195. Oh, that's just typical for leika. The article said that's a high price for authenticity, but Leica says exactly as you said, ant says the camera's cost has more to do with Leicas heritage. Kieran Ani Leicas, vice President of Marketing said, if you look at the price points for our M series cameras, there's absolutely no added cost to have the content credentials feature in the M 11 P.
(01:52:27):
And the M 11 P is just the tip of the iceberg. Canon and Nikon already have prototype cameras with content credentialing support. Smartphones will also get it, get in on the action true pick a startup that builds authenticity infrastructure has partnered with Qualcomm to make Qualcomm's Snapdragon eight Gen three chips support content credentials. Those chips will power flagship Android smartphones next year. No news organization currently requires photographers to use content credentials, but the C two PA standards influence is beginning to be felt. Kani points out that the New York Times and BBC are members of the CAI, as are the Wall Street Journal, the Washington Post, the Associated Press, Reuters, and Gannet Kani notes that adoption is certainly a goal. So back to Alpha Geek's question. This all sounds great On the surface, A digital camera contains a digital representation of an image which can be digitally signed by the camera itself.
(01:53:39):
The way this would be done is that metadata would be added to the image, then a cryptographic hash would be taken of the combined file. That hash would then be encrypted using the camera's private key. Then at a later time, it would be possible to verify that not a single pixel of the original image had been tampered with by rehashing the image and using Leicas published public key to decrypt and verify that the hash bound to the image matches the one that was just made. But from everything we know of crypto, there would appear to be one glaring problem with this entire concept detail. A web server's private key is secure only because no unauthorized people are able to obtain its key. If that key is in a hardware HSM, then that key won't even exist in the machine's memory, making it even less acceptable.
(01:54:45):
Although asymmetric encryption offers many cool features and powers, it does still rely upon a secret being kept. Its private key must remain private, and that's the Achilles heel that I fear. Any digitally signing camera will face a web server's. Private keys are safe only because no one has unauthorized physical access to its hardware. If you can get to the hardware, all betts are off. Just ask the folks that thought that encrypting DVD discs was a great idea. They thought, Hey, no problem. We'll just embed all of the decryption keys into every consumer DVD player so that they'll be able to decrypt the discs right back in the day. My copy of DVD Decryptor was one of my favorite tools. I have
Ant Pruitt (01:55:48):
No comment on
Steve Gibson (01:55:48):
That. It was, oh, it was. And still is entirely legal to decrypt one's own DVDs. And I appreciated the freedom that afforded. In order for this Leica or any other camera to digitally sign anything, it must carry a secret. It's the camera's secret that makes its signature mean something. But the camera is obviously not locked up in some data center somewhere, just like a DVD player. It must be out in the open to do its job. And everything history has taught us is that these secrets cannot be kept, not under these conditions. And if that's true, it creates another new problem that we never had before. Digitally verified deep fakes. Once a camera's secret signing key escapes, deep fakes will be signed and digitally authenticated making the problem worse than it was before. So it'll be interesting to see how this all turns out. Mark me down as skeptical and a bit worried.
Ant Pruitt (01:57:06):
Okay. So yes, this story got my attention, and I spoke about this back in October on Tech News Weekly with our host, Mr. Micah, Sergeant and Mr. Jason Howell, October 12th, 2023. This was right after the Adobe Max Creator Conference. And the big discussion was of course, ai, but it was also about content authenticity. Adobe, as the emailer mentioned, has been working with the C two PA for quite a while now, a handful of years now. And so we've had some developments on this and it was all good news, but just as you said, there are a couple caveats. First of all, the presentation. I could shoot something with my camera that is certified and has all of the proper encryption to put that badge on the image. But what if I put that on Instagram? Instagram's not going to show that badge. It's not going to mean a hill of beans.
(01:58:10):
And then I never thought about the aspect that you brought up of that key being out in the public and available to anyone. They could take it and make some totally ridiculous images that are fake, but they're properly signed, so they're still considered official. So yeah, I'm glad that this is in place. I'm glad that there's some headway being made here with the different partners with the C tpa, A because it was Microsoft. I'm looking at the page now. Microsoft, BBC, Intel, Sony. So people are talking about this and they have good intentions, especially right now with this being November here in the US and the official start of the US election season. I think this is really important to figure out a way to get our hands on some of this content that's being put out there is missing and disinformation, but again, this is very early. It's not perfect, but it's a start.
Steve Gibson (01:59:19):
So Andrew Draper said, if the EU demand their certificates are in our root store, could we not just remove them or have a script or extension that does? Okay, so great question. Many questions remain about this whole unresolved mess. For example, would the EU certs be counters signing traditional certificate authority certs based on the behavior that the EU wants? That could be a requirement, but if not, then removing those trust routes would prevent access to those EU web services that had only been signed by the EU certificates and had not been countersigned. Would these EU certs be trusted all?
(02:00:17):
Would they be trusted all by themselves if they're standing alone? If not, then we really don't have anything to worry about. So long as a traditional CA also needs to sign a website certificate, the EU signing would simply be adding additional information. But if this were the case, everyone would not be all up in arms over this and everyone is. So it sounds like the EU certs are going to be able to stand alone, and that's a problem. So it appears that the EU wants their certs that way to be able to stand alone. Would these EU certs carry some distinguishing mark that would allow an automated sweeper to uniquely identify and remove them? I suspect that the ca browser forum would require some form of clear designation. And the good news is that certs have all manner of means for carrying such markings. This will make a cleaner entirely safe.
(02:01:17):
It would be able to identify those certs, which were based on this EU E-I-D-A-S law. One potential problem is that users of affected machines, such as in the enterprise, may have limited access to their machine's, certificate root stores. But the biggest problem is that while those listening to this podcast and other in the know techies might know enough to clean their root stores, most of the world would not. So yeah, even if some of us were to keep our machines clean, that doesn't help everyone else in the world, right? I Mike asked, Hey Steve, what company do you recommend for a domain registrar? I currently have all my domains with Google Domains, and they're moving to Squarespace. I only need a place to store the domains as my name servers are with various other providers. Thanks, Mike. So without any hesitation, I would and do always recommend Hover Woo.
(02:02:21):
And I cannot imagine why I would ever move. I did move once, and that was away from Network Solutions. They were the original primary registrar of domains for the internet. But let's just say they did not age well. I became so tired of network solutions, constant upselling attempts. When I did anything there, I would be forced to decline one special limited time offer after another endlessly just to renew a domain. I'm inherently loyal, so I did stick with them as long as I could, but finally it was too much. So I went looking for an alternative. A good ultra techie friend of mine, Mark Thompson, at Analog X all has all of his domains with GoDaddy. But GoDaddy's style doesn't appeal to me either. They just don't seem serious. And the one thing you want in a domain registrar is seriousness. They've also had security problems in the past with some of their services, though I don't think what their domain registrar business, by comparison, hover is just a clean and simple domain registrar.
(02:03:36):
They do offer some other services, but they are never pushed for a long while. They were advertisers here on twit. But it was one of those situations where I had switched to hover and was already singing their praises every chance I got long before they began advertising here. And I still am for the same reason singing their praises. So anyone who's looking for a clean and simple, no frills, no annoying upselling domain registrar, I think will find that in Hover. And I know that Leo feels the same way, as do I. Cool. And our last question from Glenn F. He said, hi, Steve. I was just listening to SSN 9 49. I wanted to let you know that you may have been a bit overly charitable when describing Apple's motives around RCS. Looks to me like Google got creative and used the EU as a cudgel to encourage Apple to adopt RCS.
(02:04:42):
From what I can tell, Apple's RCS announcement appears to coincide with the deadline for their response to the eu Love the show, and just recently joined Club Twit due to all the great content, Glen, thank you. Okay. So yeah, Glenn's tweet linked to an interesting article at the Verge. The Verges headline reads, Google turns to regulators to make Apple Open up iMessage. And their tagline is, in addition to shaming Apple for not supporting R css, the search giant has reportedly co-signed a letter arguing that iMessage should, I'm sorry, should be designated a core platform service under the eus Digital Markets Act. Okay, so I read the entire piece, and I agree with Glenn's assessment. What Google really appears to want is to force Apple to open iMessage. Since today's green bubbles are lame by comparison to the blue ones, I have a text messaging group where one of its five members is an Android user.
(02:05:53):
As a consequence, the entire group is forced out of iMessage into SMS and thus reduced to this lowest common denominator due to the presence of this one individual in our group who is not an iPhone user. So if Apple were to upgrade the rest of US iPhone people to RCS, then the Green Bubbles would be at parody with iMessage Blue Bubbles. But as for opening up iMessage from a technical standpoint, I cannot see how that's really possible due to the closed security ecosystem iMessage lives within. I bet that's the last thing that Apple would consider doing. But the addition of RCS does seem like a clever countermeasure designed to take the pressure off Apple in this regard. And I think the Google should be happy with it. I know I would be, again, what more do they need to do? Right? Right. Basically giving iMessage features to the Android user community and allowing that to cross over into the iOS ecosystem.
(02:07:11):
I think that sounds right, and I'll just wrap up by saying, reminding everyone. The title of today's podcast is Leo Turns 67, and as I mentioned, last week's podcast was titled Ethernet Turned 50. So I decided to go with Leo turned 67 since that's happening tomorrow on November 29th. And even though he's currently sequestered in some far off cave somewhere with no internet and no other technology doubtless, contemplating the nature of life, the universe and everything, you might want to send him birthday wishes, which I am sure he'll discover once he emerges and rejoins the rest of humanity much as he'll be rejoining us this time next week. And aunt, thank you for being my host this week.
Ant Pruitt (02:08:00):
Oh, Mr. Gibson, thank you so much. This was another fine and fun time here on security now. And yeah, kudos to you, Mr. LaPorte. Happy birthday to you and hope everything is going well in that cave or wherever it is you are right now, this week. Oh man. Again, Mr. Gibson, thank you so much. A lot of fun here on security. Now, I always enjoyed talking to you and listening to your coverage about what's happening here in the cybersecurity space. Granted, a lot of it is, I'm not smart enough to understand, but you tend to break it down for even me, and it does help go a long way when I have to talk to those hardhead of mine about cybersecurity and what's going on out here in these internet. So thank you again, sir.
Steve Gibson (02:08:49):
It's my pleasure. Great to be with you.
Ant Pruitt (02:08:51):
Alright, everybody, we really do appreciate y'all hanging out with us today here in security. Now we do this show each and every Tuesday. It's usually about one 30 Pacific time, somewhere in that area. If Mr. LaPorts hosting is probably going to be a little bit later, because y'all know how he rolls. Oh, wait a minute. I said that into the mic. Sorry. Yeah, it is usually about one 30 Pacific Time, according to the website. 2130 UTCI don't know if that's right. Don't check my math. Make sure you check us out in whatever podcast application you enjoy and download the shows each and every week. Just go ahead and set your app to auto download. Okay. Because that really helps us out. And of course, we appreciate all of our Club TWIT members for hanging out with us each and every week and supporting us. Club Twit, you say?
(02:09:40):
Yeah, club Twit is our awesome membership group here at twit. It's just seven bucks a month and it offers you the opportunity to get all of our shows ad free. You get access to our Discord server. We have a live chat going on in the Discord every time the shows are going on and recording a bunch of different channels in there for forums and great conversations and discussions and memes and lots of fun stuff in there, including people like Mr. Joe Esposito that likes to make funny stickers of some of us hosts here at twit. So that's just one of the benefits, but it also just, it's another way to help support us at the network because real talk folks, it's hard out here in these podcast. It's pretty hard out here. So every little bit helps us out. We really do appreciate it's just seven bucks a month ad free content.
(02:10:31):
You get Discord access, you get only Club Twit exclusive shows, such as Hands on Mac, hands on Windows, the Untitled Linux Show. There's a Twit plus bonus feed that has things in there like pre and post show stuff that where we have some interesting conversations to say the least, such as what is Lily doing today before Security Now, or the Stacey's Book Club? We have that coming up here soon and some other interviews that we have in Twit plus feed. So make sure y'all sign up and check that out and tell others about Club Twit. Alright, that is going to do it for us here today. Thank you to Mr. Gibson. Thank you to the squad there in the studio for making us look and sound good today, Mr. Berg, Mr. Jamer b. Hey, we appreciate all the support and we shall see you all next time. Take care. Bye.
Rod Pyle (02:11:28):
Hey, I'm Rod Pyle, editor in Chief VAD Astor magazine. And each week I joined with my co-host to bring you this week in space, the latest and greatest news from the Final Frontier. We talk to NASA chiefs, space scientists, engineers, educators, and artists, and sometimes we just shoot the breeze over what's hot and what's not in space books and tv, and we do it all for you, our fellow true believers. So whether you're an armchair adventurer or waiting for your turn to grab a slot in Elon's Mars Rocket, join us on this week in space and be part of the greatest adventure of all time.
Ad (02:12:07):
Now's the time to start your next adventure behind the wheel of an exciting new Toyota hybrid with the largest lineup of hybrid plug-in hybrid and electrified vehicles to choose from. Toyota has the one for you. Every new Toyota hybrid comes with ToyotaCare, two year complimentary scheduled maintenance, an exclusive hybrid battery warranty, and Toyota's legendary quality and reliability. Visit your local Toyota dealer today. Toyota, let's go places. See your local Toyota dealer for hybrid battery warranty details.