When Disclosure Backfires: The Dlink NAS Vulnerability Debacle
AI written, human edited.
In a recent episode of the Security Now podcast, hosts Steve Gibson and Leo Laporte delved into a troubling discovery about Dlink network-attached storage (NAS) devices - the revelation of a hardcoded backdoor that left thousands of these devices exposed to potential exploitation.
The discussion began with Gibson highlighting the persistent issue of manufacturers embedding remote access credentials into their products, even after repeated instances of this practice being deemed insecure. He outlined five best practices that could have prevented such vulnerabilities, including the elimination of default credentials, requiring physical access to change security settings, and ensuring automatic firmware updates.
However, the crux of the conversation centered around the actions of a researcher who discovered the Dlink NAS backdoor. Dubbed "network security fish," the researcher publicly disclosed the vulnerability without prior notice to Dlink, leading to the immediate detection of active exploitation attempts by malicious actors.
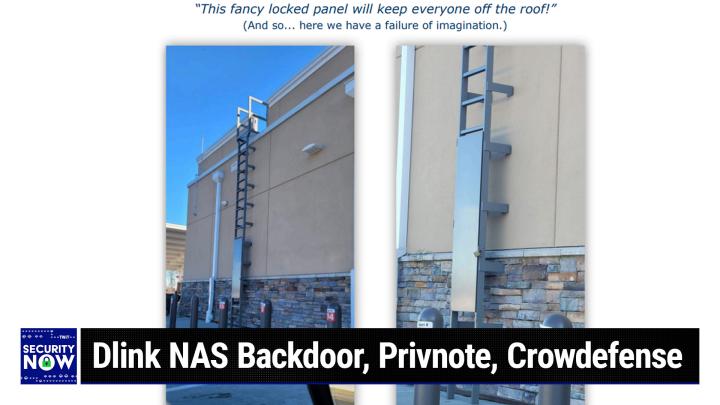
Gibson expressed deep concern over this disclosure, arguing that the researcher's actions had effectively "compromised the security of 92,589 still online, still functioning, still in use and still sitting on other people's networks" without any opportunity for Dlink to address the issue. He likened the vulnerability to a "ScriptKitty class" flaw, implying that it was low-hanging fruit ripe for exploitation by a wide range of threat actors.
Laporte echoed Gibson's sentiment, describing the researcher's actions as "showing off" rather than serving any meaningful purpose. The hosts pondered whether a more responsible approach, akin to Google's Project Zero 90-day disclosure policy, would have been more appropriate in this case, given that the affected devices were no longer actively supported by Dlink.
The discussion highlighted the delicate balance between responsible disclosure and the potential risks of premature or unnecessary public exposure of vulnerabilities. The hosts lamented the likely consequences of this disclosure, with thousands of devices now potentially compromised and vulnerable to malware infections or further exploitation.
The Dlink NAS vulnerability episode serves as a cautionary tale, underscoring the importance of coordinated and thoughtful vulnerability management, as well as the need for manufacturers to uphold robust security practices in their product design and support. As the podcast hosts emphasized, complex devices that are no longer actively maintained pose significant risks and should be retired or isolated from public-facing networks whenever possible.
This incident exemplifies the ongoing challenges in the cybersecurity landscape, where the actions of well-intentioned researchers can sometimes have unintended and potentially damaging consequences. The Security Now podcast's deep dive into this issue provides valuable insights for both security professionals and device owners, highlighting the need for a collaborative and responsible approach to addressing vulnerabilities in the ever-evolving world of networked technologies.
Become a subscriber and never miss an episode: Security Now